Z-Library eBook site domains seized by U.S. Dept of JusticeInternet domains for the popular Z-Library online eBook repository were seized early this morning by the U.S....
British govt is scanning all Internet devices hosted in UK
British govt is scanning all Internet devices hosted in UKThe United Kingdom's National Cyber Security Centre (NCSC), the government agency that leads the country's cyber security mission,...
NSA on Supply Chain Security
NSA on Supply Chain SecurityThe NSA (together with CISA) has published a long report on supply-chain security: “Securing the Software Supply Chain: Recommended Practices Guide for...
LinkedIn Adds Verified Emails, Profile Creation Dates
LinkedIn Adds Verified Emails, Profile Creation DatesResponding to a recent surge in AI-generated bot accounts, LinkedIn is rolling out new features that it hopes will help...
Friday Squid Blogging: Newfoundland Giant Squid Sculpture
Friday Squid Blogging: Newfoundland Giant Squid SculptureIn 1878, a 55-foot-long giant squid washed up on the shores of Glover’s Harbour, Newfoundland. It’s the largest giant squid...
ACE seizes 42 soccer and live TV piracy web domains with millions of visitors
ACE seizes 42 soccer and live TV piracy web domains with millions of visitorsThe Alliance for Creativity and Entertainment (ACE) has shut down 42 websites for...
FBI: Hacktivist DDoS attacks had minor impact on critical orgs
FBI: Hacktivist DDoS attacks had minor impact on critical orgsThe Federal Bureau of Investigation (FBI) said on Friday that distributed denial-of-service (DDoS) attacks coordinated by hacktivist...
Crime group hijacks hundreds of US news websites to push malware
Crime group hijacks hundreds of US news websites to push malwareContenido de la entradaLeer másProofpoint News Feed
Microsoft sued for open-source piracy through GitHub Copilot
Microsoft sued for open-source piracy through GitHub CopilotProgrammer and lawyer Matthew Butterick has sued Microsoft, GitHub, and OpenAI, alleging that GitHub's Copilot violates the terms of...
More than 250 US news sites inject malware in possible supply chain attack
More than 250 US news sites inject malware in possible supply chain attackContenido de la entradaLeer másProofpoint News Feed
New Microsoft Teams update, you can ‘assign seats’ in meetings
New Microsoft Teams update, you can ‘assign seats’ in meetingsEXECUTIVE SUMMARY: Together Mode is an option in Microsoft Teams that makes your participants look as though...
Live Panel | Why You Have an MFA Emergency on Your Hands And What to do about it
Live Panel | Why You Have an MFA Emergency on Your Hands And What to do about itContenido de la entradaLeer másDataBreachToday.com RSS Syndication
2023 Power Panel: Mapping Your Future Cybersecurity Strategy
2023 Power Panel: Mapping Your Future Cybersecurity StrategyContenido de la entradaLeer másDataBreachToday.com RSS Syndication
LockBit Claims Attack on German Auto Parts Giant Continental
LockBit Claims Attack on German Auto Parts Giant ContinentalCompany Acknolweged an Attack in August, Silent Since on HackersRansomware-as-a-service group LockBit is threatening the release of data...
Cyberattack at Boeing Disrupts Flight Planning
Cyberattack at Boeing Disrupts Flight PlanningServices from Boeing Subsidiary Jeppesen Affected By Ongoing IncidentDistribution of airspace safety notices are affected by a cyber incident at Boeing...
Sexual Assault, Abuse Victims’ Data at Risk in Australia
Sexual Assault, Abuse Victims' Data at Risk in AustraliaInvestigators to Determine if Hacker Accessed Legal Aid Group’s Client InformationA hack of an Australian legal aid group...
Phishing-as-a-Service Platform Offers MFA Bypass for $1500
Phishing-as-a-Service Platform Offers MFA Bypass for $1500Robin Banks Now Offers a New Cookie-Stealing FeatureCybercrime syndicate Robin Banks is back with a new cookie-stealing feature that cybercriminals...
The Week in Security: OpenSSL danger downgraded but still real, GitHub exposed
The Week in Security: OpenSSL danger downgraded but still real, GitHub exposed Welcome to the latest edition of The Week in Security, which brings you the...
Security Awareness Needs a New Experience, Not More New Content
Security Awareness Needs a New Experience, Not More New ContentIf you are shopping for a security awareness vendor, you have Netflix-style variety at your fingertips. The...
BSidesPDX 2022 – Ken Westin’s ‘Opening Remarks’
BSidesPDX 2022 – Ken Westin’s ‘Opening Remarks’Our sincere thanks to BSidesPDX 2022 for publishing their outstanding conference videos on the organization's YouTube channel. Permalink The post...
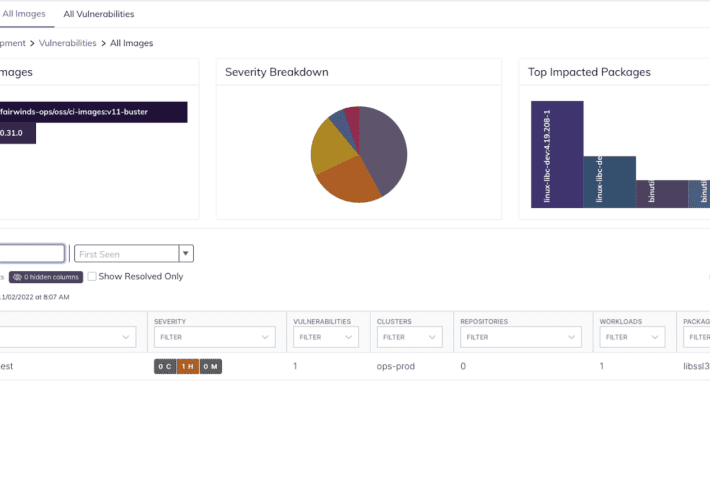
CVE-2022-3602 and CVE-2022-3786 OpenSSL Vulnerabilities: Scanning Container Images
CVE-2022-3602 and CVE-2022-3786 OpenSSL Vulnerabilities: Scanning Container Images On November 1st, 2022, OpenSSL announced a pair of High Severity vulnerabilities in version 3.0.0-3.0.6 of OpenSSL. The...
Analyzing CISA Known Exploited Vulnerabilities with Business Context
Analyzing CISA Known Exploited Vulnerabilities with Business ContextWhat is CISA Directive BOD 22-01? In November 2021, the US Cybersecurity and Infrastructure Security Agency (CISA), an agency...
What You Need to Know About SBOM Generation Tools
What You Need to Know About SBOM Generation ToolsWhen it comes to tools for generating a software bill of materials (SBOM), organizations basically have three options:...
Zurich and Mondelez Reach NotPetya Settlement, but Cyber-Risk May Increase
Zurich and Mondelez Reach NotPetya Settlement, but Cyber-Risk May IncreaseThe parties have mutually resolved the matter, but details of the settlement were not providedLeer másThe parties...
RomCom Weaponized KeePass and SolarWinds Instances to Target Ukraine, Maybe UK
RomCom Weaponized KeePass and SolarWinds Instances to Target Ukraine, Maybe UKThe discovery comes from the BlackBerry Research & Intelligence TeamLeer másThe discovery comes from the BlackBerry...
Five Tips for Low-Friction Authentication
Five Tips for Low-Friction Authentication Authentication processes often introduce unwelcome friction into the user experience. Generally speaking, friction equates to the effort needed from the end...
How can Identity Verification prevent scams in MLM and D2C industries?
How can Identity Verification prevent scams in MLM and D2C industries?In India, there have been several Multi-Level-Marketing (MLM) frauds. Investing in stock shares and commodities, paid...
Researchers Find Links b/w Black Basta Ransomware and FIN7 Hackers
Researchers Find Links b/w Black Basta Ransomware and FIN7 HackersA new analysis of tools put to use by the Black Basta ransomware operation has identified ties...
CISA Warns of Critical Vulnerabilities in 3 Industrial Control System Software
CISA Warns of Critical Vulnerabilities in 3 Industrial Control System SoftwareThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) has published three Industrial Control Systems (ICS) advisories about multiple...
TikTok Confirms Chinese Staff Can Access UK and EU User Data
TikTok Confirms Chinese Staff Can Access UK and EU User DataThe news comes from the social media giant’s head of privacy in Europe, Elaine FoxLeer másThe...