Microsoft fixes ProxyNotShell Exchange zero-days exploited in attacksMicrosoft has released security updates to address two high-severity Microsoft Exchange zero-day vulnerabilities collectively known as ProxyNotShell and exploited...
MSA-22-0027: Quiz sequential navigation bypass using web services
MSA-22-0027: Quiz sequential navigation bypass using web servicesот Michael Hawkins. Insufficient limitations in some quiz web services made it possible for students to bypass sequential navigation...
MSA-22-0026: No groups filtering in H5P activity attempts report
MSA-22-0026: No groups filtering in H5P activity attempts reportот Michael Hawkins. The H5P activity attempts report did not filter by groups, which in separate groups mode...
MSA-22-0025: Minor SQL injection risk in admin user browsing
MSA-22-0025: Minor SQL injection risk in admin user browsingот Michael Hawkins. A limited SQL injection risk was identified in the "browse list of users" site administration...
Influencer ‘Ray Hushpuppi’ jailed over plan to launder $300m
Influencer ‘Ray Hushpuppi’ jailed over plan to launder $300mRamon Abbas, described by FBI as one of world’s most prolific money launderers, sentenced to 11 years A...
Tech giants accuse Labor of ‘overreach’ over bill fining companies $50m for data breaches
Tech giants accuse Labor of ‘overreach’ over bill fining companies $50m for data breachesFacebook parent company Meta, Google, Twitter and Business Council of Australia warn of...
Medibank says ransomware group’s threat to release customer information a ‘distressing development’
Medibank says ransomware group’s threat to release customer information a ‘distressing development’‘Data will publish within 24 hours’ post to darknet blog says, after Australian health insurer...
Who Is Extorting Australian Health Insurer Medibank?
Who Is Extorting Australian Health Insurer Medibank?A Ransomware Group Has Given Medibank 24 Hours to Pay. But Medibank Says It Won't.Who is attempting to extort Australian...
Live Webinar | How to Implement a Security Awareness Program in Practice
Live Webinar | How to Implement a Security Awareness Program in PracticeContenido de la entradaLeer másDataBreachToday.com RSS Syndication
Using Student Data for Gambling Apps Is Bad, Says UK ICO
Using Student Data for Gambling Apps Is Bad, Says UK ICOOffice Reprimands Department, Says Fine Would Have Been Over 10 Million PoundsThe British data watchdog says...
Aveanna Healthcare Data Breach Could Cost Firm More Than $1M
Aveanna Healthcare Data Breach Could Cost Firm More Than $1MPhishing Onslaught Caused Breach Affecting 166,000 Individuals NationwideA Georgia-based home health and hospice provider will pay $425,000...
FortiGuard Labs: 2023 Threat Landscape Insights
FortiGuard Labs: 2023 Threat Landscape InsightsDerek Manky on How Cybercrime as a Service Will Enable More Destructive AttacksConvergence of the threat landscape looms large for defenders,...
Feds Announce Silk Road Cryptocurrency Haul
Feds Announce Silk Road Cryptocurrency HaulReal Estate Developer Stole 50,000 Bitcoins From the Dark Web Emporium a Decade AgoFederal agents seized more than 50,000 in bitcoin...
Business Email Compromise: Low-Tech, High-Impact Threat
Business Email Compromise: Low-Tech, High-Impact Threat One of the least technologically sophisticated cyberattacks, business email compromise (BEC), is also one of the most damaging. According to...
CISOs, Security Leaders Eyeing Other Job Options
CISOs, Security Leaders Eyeing Other Job Options Nearly a third of CISOs or IT security leaders in the United States and the United Kingdom are considering...
How DevOps Drive Business Growth?
How DevOps Drive Business Growth?The world of information technology is constantly advancing. As time passes, technological tools, trends, and usage behavior change. Integration of DevOps within...
Safely Test Your Malware, Ransomware and Virus Defenses
Safely Test Your Malware, Ransomware and Virus Defenses What’s the best way for a company to test its malware defenses in real-life scenarios? The past few...
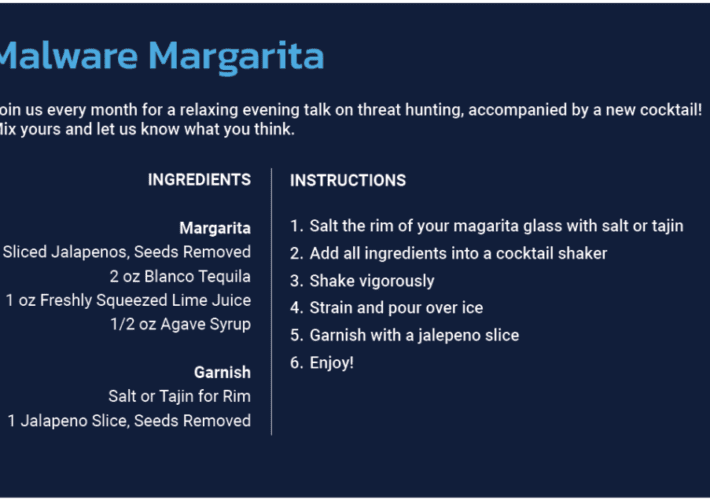
Episode 3
Episode 3Cyborg Security is launching a podcast with a twist! Join us for the first fully interactive threat hunting podcast where you can hang out with...
BSidesPDX 2022 – Devin Gaffney’s ‘Reverse Engineering: How WAFs (Fail To) Identify Bots’
BSidesPDX 2022 – Devin Gaffney’s ‘Reverse Engineering: How WAFs (Fail To) Identify Bots’Our sincere thanks to BSidesPDX 2022 for publishing their outstanding conference videos on the...
Medibank Refuses to Pay Ransom After 9.7 Million Customers Exposed in Ransomware Hack
Medibank Refuses to Pay Ransom After 9.7 Million Customers Exposed in Ransomware HackAustralian health insurer Medibank today confirmed that personal data belonging to around 9.7 million...
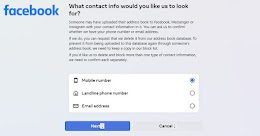
This Hidden Facebook Tool Lets Users Remove Their Email or Phone Number Shared by Others
This Hidden Facebook Tool Lets Users Remove Their Email or Phone Number Shared by OthersFacebook appears to have silently rolled out a tool that allows users...
Ukraine’s Response to Cyber Threats a Model in DDoS Prevention
Ukraine’s Response to Cyber Threats a Model in DDoS PreventionWith the disruption, loss of life and heartbreaking images that the Russia-Ukraine conflict has produced, it is...
Experts Find URLScan Security Scanner Inadvertently Leaks Sensitive URLs and Data
Experts Find URLScan Security Scanner Inadvertently Leaks Sensitive URLs and DataSecurity researchers are warning of "a trove of sensitive information" leaking through urlscan.io, a website scanner for...
Island-hopping attacks | Brand protection in an era of island hopping | Contrast Security
Island-hopping attacks | Brand protection in an era of island hopping | Contrast Security How many vulnerabilities are lurking, ready to boobytrap your apps and lay...
Public URL scanning tools – when security leads to insecurity
Public URL scanning tools – when security leads to insecurityNever make your users cry/By how you use an APILeer másNaked SecurityNever make your users cry/By how...
Voices from Validate – Simplifying Posture Management
Voices from Validate – Simplifying Posture ManagementLearn from Zscaler how zero trust, MITRE ATT&CK, and BAS can work together to optimize security posture across complex environments....
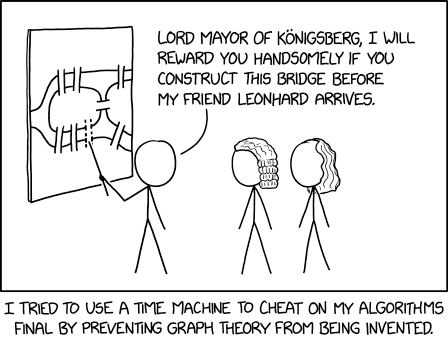
Randall Munroe’s XKCD ‘Königsberg’
Randall Munroe’s XKCD ‘Königsberg’ via the comic artistry and dry wit of Randall Munroe, resident at XKCD! Permalink The post Randall Munroe’s XKCD ‘Königsberg’ appeared first...
Cyber Insurance Market Stabilizing as Security Awareness Improves
Cyber Insurance Market Stabilizing as Security Awareness ImprovesThe cyber insurance market is beginning to stabilize following several years of steep rate increases, according to a recent...
Android RAT Group Targets Indian Defense Personnel
Android RAT Group Targets Indian Defense PersonnelThe app asked for several permissions, including camera, microphone, internet and storageLeer másThe app asked for several permissions, including camera,...
Medibank Refuses to Pay Ransom After Data Breach
Medibank Refuses to Pay Ransom After Data BreachMedibank believes there is a limited chance paying a ransom would return customers' dataLeer másMedibank believes there is a...