Experts observed Amadey malware deploying LockBit 3.0 RansomwareExperts noticed that the Amadey malware is being used to deploy LockBit 3.0 ransomware on compromised systems. Researchers from AhnLab Security...
Microsoft: Windows 10 21H1 reaches end of service next month
Microsoft: Windows 10 21H1 reaches end of service next monthMicrosoft has reminded customers today that all editions of Windows 10 21H1 (also known as the May...
Malicious Extension Grants Threat Actors Remote Access to Google Chrome
Malicious Extension Grants Threat Actors Remote Access to Google ChromeCybersecurity researchers discovered ‘Cloud9’ – a new Chrome browser botnet that uses malicious extensions to steal user...
Armageddon APT Hacker Group aka UAC-0010 Spreads Phishing Emails Masquerading as the State Special Communications Service of Ukraine
Armageddon APT Hacker Group aka UAC-0010 Spreads Phishing Emails Masquerading as the State Special Communications Service of Ukraine The russia-linked Armageddon APT aka Gamaredon or UAC-0010...
VMware fixes three critical auth bypass bugs in remote access tool
VMware fixes three critical auth bypass bugs in remote access toolVMware has released security updates to address three critical severity vulnerabilities in the Workspace ONE Assist solution...
Having refused to pay ransom, health insurer Medibank sees customer data posted online by hackers
Having refused to pay ransom, health insurer Medibank sees customer data posted online by hackersA ransomware gang has begun to publish data on the dark web...
Malicious extension lets attackers control Google Chrome remotely
Malicious extension lets attackers control Google Chrome remotelyA new Chrome browser botnet named 'Cloud9' has been discovered in the wild using malicious extensions to steal online...
Patch Tuesday, November 2022 Election Edition
Patch Tuesday, November 2022 Election EditionLet’s face it: Having “2022 election” in the headline above is probably the only reason anyone might read this story today....
Defeating Phishing-Resistant Multifactor Authentication
Defeating Phishing-Resistant Multifactor AuthenticationCISA is now pushing phishing-resistant multifactor authentication. Roger Grimes has an excellent post reminding everyone that “phishing-resistant” is not “phishing proof,” and that...
TeamTNT Returns — Or Does It?
TeamTNT Returns — Or Does It?Our honeypots caught malicious cryptocurrency miner samples targeting the cloud and containers, and its routines are reminiscent of the routines employed...
LockBit affiliate uses Amadey Bot malware to deploy ransomware
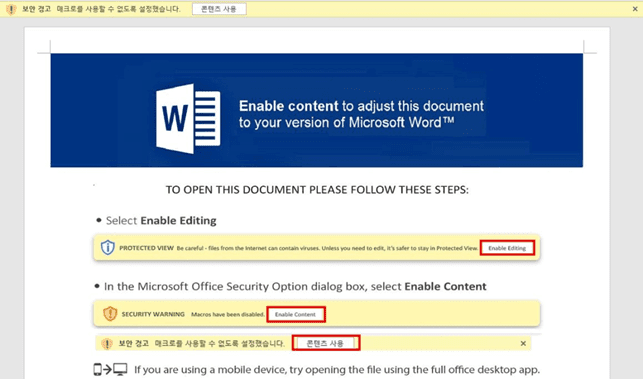
LockBit affiliate uses Amadey Bot malware to deploy ransomwareA LockBit 3.0 ransomware affiliate is using phishing emails that install the Amadey Bot to take control of...
Hack the Real Box: APT41’s New Subgroup Earth Longzhi
Hack the Real Box: APT41’s New Subgroup Earth LongzhiWe looked into the campaigns deployed by a new subgroup of advanced persistent threat (APT) group APT41, Earth...
Lenovo fixes flaws that can be used to disable UEFI Secure Boot
Lenovo fixes flaws that can be used to disable UEFI Secure BootLenovo has fixed two high-severity vulnerabilities impacting various ThinkBook, IdeaPad, and Yoga laptop models that...
MSA-22-0024: Remote code execution risk when restoring malformed backup file from Moodle 1.9
MSA-22-0024: Remote code execution risk when restoring malformed backup file from Moodle 1.9от Michael Hawkins. A remote code execution risk when restoring backup files originating from...
China Likely Amasses 0-Days Via Vulnerability Disclosure Law
China Likely Amasses 0-Days Via Vulnerability Disclosure LawMicrosoft Finds Increased Use of Zero-Days by Chinese Hackers Over Past YearIt's been a year since Beijing imposed regulations...
Feds Warn of Iranian Threats to Healthcare Sector
Feds Warn of Iranian Threats to Healthcare SectorTehran Hackers Use Social Engineering to Close Sophistication GapThe healthcare industry should be aware of Iranian hackers using social...
Ransomware group starts publishing Medibank data as company warns customers to be vigilant for scammers
Ransomware group starts publishing Medibank data as company warns customers to be vigilant for scammersHundreds of names, addresses, birthdates and Medicare details posted under ‘good list’...
EU Complicit in Spread of Advanced Spyware, Charges Veld
EU Complicit in Spread of Advanced Spyware, Charges VeldPEGA Committee Rapporteur Sophie in 't Veld Calls for Spyware MoratoriumA Dutch member of the European Parliament accused...
Spotlight: STEM Day 2022
Spotlight: STEM Day 2022DataDome spotlights STEM Day 2022, emphasizing science, technology, engineering, & math education, careers, & women empowerment. The post Spotlight: STEM Day 2022 appeared...
MFA Adoption is Improving, but Cybercriminals are Keeping Up
MFA Adoption is Improving, but Cybercriminals are Keeping Up While multifactor authentication has historically been hailed as one of the most significant forms of defense against...
6 Kubernetes Cost Control Strategies You Need in Place for 2023
6 Kubernetes Cost Control Strategies You Need in Place for 2023 Organizations have moved increasingly to the cloud, adopting containers and Kubernetes to change their infrastructure...
Social Engineering Attacks on New Employees
Social Engineering Attacks on New EmployeesOpportunistic cybercriminals increasingly opt for psychological manipulation over technical hacks to gain entry points into networks. Many personnel – employees, business...
What you should know about cloud workload protection platforms (CWPP)
What you should know about cloud workload protection platforms (CWPP)Learn how to secure web applications with cloud workload protection platforms (CWPP), how these cloud security solutions...
SAP Patch Day: November 2022
SAP Patch Day: November 2022SAP Patch Day: November 2022 Onapsis Tue, 11/08/2022 - 14:46 Critical HotNews for SAP BusinessObjects and SAPUI5 November Summary - 14 new...
Can You Manage Change Management?
Can You Manage Change Management? In a recent podcast interview with Hillarie McClure, Multimedia Director of Cybercrime Magazine, Robert E. Johnson III, Cimcor CEO/President, discusses how...
Hacker Stole $3B of Bitcoin — Because ‘Crypto’ is Garbage
Hacker Stole $3B of Bitcoin — Because ‘Crypto’ is Garbage James Zhong admitted to stealing 50,000 bitcoins from the former dark web market, Silk Road The post...
Vultur Android Banking Trojan Reaches 100,000+ Downloads on Google Play Store
Vultur Android Banking Trojan Reaches 100,000+ Downloads on Google Play StoreThe dropper hides behind a fake utility app with limited permissions and a small footprintLeer másThe...
Silk Road Thief Pleads Guilty to $3.4bn Raid
Silk Road Thief Pleads Guilty to $3.4bn RaidMan stole 50,000 Bitcoin from notorious dark web marketplaceLeer másMan stole 50,000 Bitcoin from notorious dark web marketplace
Forrester Security & Risk talk: Go beyond the SBOM for software supply chain security
Forrester Security & Risk talk: Go beyond the SBOM for software supply chain security At the Forrester Security & Risk Forum, ReversingLabs Field CISO Matt Rose talks...
New Laplas Clipper Malware Targeting Cryptocurrency Users via SmokeLoader
New Laplas Clipper Malware Targeting Cryptocurrency Users via SmokeLoaderCryptocurrency users are being targeted with a new clipper malware strain dubbed Laplas by means of another malware known as...