Researchers show techniques for malware persistence on F5 and Citrix load balancersOver the past several years, hackers have targeted public-facing network devices such as routers, VPN...
High-Severity Flaw Reported in Critical System Used by Oil and Gas Companies
High-Severity Flaw Reported in Critical System Used by Oil and Gas CompaniesCybersecurity researchers have disclosed details of a new vulnerability in a system used across oil...
Malicious Package on PyPI Hides Behind Image Files, Spreads Via GitHub
Malicious Package on PyPI Hides Behind Image Files, Spreads Via GitHubThe findings indicate that PyPI malicious packages and their obfuscation techniques are evolvingLeer másThe findings indicate...
Citrix Issues Patches for Critical Flaw Affecting ADC and Gateway Products
Citrix Issues Patches for Critical Flaw Affecting ADC and Gateway ProductsCitrix has released security updates to address a critical authentication bypass flaw in the application delivery controller (ADC)...
5 Tips to Secure a Windows Environment
5 Tips to Secure a Windows EnvironmentBecause Microsoft Windows is such a key component of so many enterprise and development environments, securing the platform is vital...
Exchange 0-days fixed (at last) – plus 4 brand new Patch Tuesday 0-days!
Exchange 0-days fixed (at last) – plus 4 brand new Patch Tuesday 0-days!In all the excitement, we kind of lost track ourselves. Were there six 0-days,...
High-Risk Vulnerability Found in ABB’s Flow Computers
High-Risk Vulnerability Found in ABB's Flow ComputersAttackers could exploit it by sending a specially crafted message to an affected system nodeLeer másAttackers could exploit it by...
Emergency code execution patch from Apple – but not an 0-day
Emergency code execution patch from Apple – but not an 0-dayNot a zero-day, but important enough for a quick-fire patch to one system library...Leer másNaked SecurityNot...
Space Force CIO Calls for Greater Collaboration, Secure Commercial Software
Space Force CIO Calls for Greater Collaboration, Secure Commercial Software Whether it’s our navigation systems or systems that manage our everyday communications, the modern world is...
Okta streamlines IAM portfolio with consumer identity management cloud
Okta streamlines IAM portfolio with consumer identity management cloudPotential access management customers got a new option from Okta Wednesday, as the identity and access management (IAM)...
Manual Vs. SSPM: Streamlining SaaS Security Management
Manual Vs. SSPM: Streamlining SaaS Security Management An interesting trend is unfolding in companies around the globe. They are investing in a growing number of SaaS...
Thousands of Sites Hacked in Massive Google SEO Poisoning Campaign
Thousands of Sites Hacked in Massive Google SEO Poisoning CampaignThis week, almost 15,000 sites were compromised during a massive black hat search engine optimization (SEO) campaign....
Couple Get 40 Years for Navy Espionage Plot
Couple Get 40 Years for Navy Espionage PlotDuo tried to sell secrets of nuclear propulsionLeer másDuo tried to sell secrets of nuclear propulsion
Outlook and Thunderbird Accounts Threatened by StrelaStealer
Outlook and Thunderbird Accounts Threatened by StrelaStealerOutlook and Thunderbird accounts are being targeted by a new info stealer malware known as StrelaStealer. The malware behaves as most...
PCI DSS 4.0 is coming: how to prepare for the looming changes to credit card payment rules
PCI DSS 4.0 is coming: how to prepare for the looming changes to credit card payment rulesFor enterprises that handle credit card data, which means just...
Malware Redirects 15,000 Sites in Malicious SEO Campaign
Malware Redirects 15,000 Sites in Malicious SEO CampaignCampaign designed to improve search engine rankings of spammy sitesLeer másCampaign designed to improve search engine rankings of spammy...
Surveillance vendor exploited Samsung phone zero-days
Surveillance vendor exploited Samsung phone zero-daysGoogle Project Zero researchers reported that a surveillance vendor is using three Samsung phone zero-day exploits. Google Project Zero disclosed three...
10 common security mistakes and how to avoid them
10 common security mistakes and how to avoid themDo you make these security mistakes and put yourself at greater risk for successful attacks? The post 10...
Some 98% of Global Firms Suffer Supply Chain Breach in 2021
Some 98% of Global Firms Suffer Supply Chain Breach in 2021Two-fifths still trust suppliers to handle their own securityLeer másTwo-fifths still trust suppliers to handle their...
Lenovo warns of flaws that can be used to bypass security features
Lenovo warns of flaws that can be used to bypass security featuresLenovo fixed two high-severity flaws impacting various laptop models that could allow an attacker to...
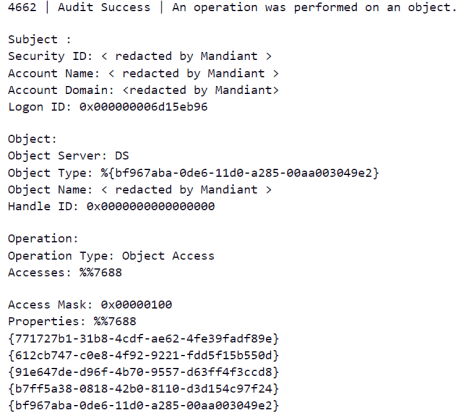
APT29 abused the Windows Credential Roaming in an attack against a diplomatic entity
APT29 abused the Windows Credential Roaming in an attack against a diplomatic entityRussia-linked APT29 cyberespionage group exploited a Windows feature called Credential Roaming to target a...
Test delete post – 10-11
Test delete post – 10-11This is test data lorem ipsum… This is test data lorem ipsum.. This is test data lorem ipsum.. This is test data...
Social Media Influencer Sentenced to 11 Years in Prison for Cyber Fraud
Social Media Influencer Sentenced to 11 Years in Prison for Cyber Fraud‘Ray Hushpuppi’, an Instagram celebrity, was sentenced to 11 years in jail for conspiring to...
Don’t Get Caught Offsides with These World Cup Scams
Don’t Get Caught Offsides with These World Cup Scams Authored by: Christy Crimmins and Oliver Devane Football (or Soccer as we call it in the U.S.)...
Medibank warns customers their data was leaked by ransomware gang
Medibank warns customers their data was leaked by ransomware gangAustralian health insurance giant Medibank has warned customers that the ransomware group behind last month's breach has started...
Private Information of Thousands of COVID-19 Patients Exposed in Resileo Leak
Private Information of Thousands of COVID-19 Patients Exposed in Resileo LeakA leak that exposed the private information of thousands of COVID-19 patients was discovered on Resileo’s...
Top 6 multi-cloud security solution providers of 2022
Top 6 multi-cloud security solution providers of 2022If you're in the process of constructing a multi-cloud security plan, these providers can help you avoid the most...
15,000 sites hacked for massive Google SEO poisoning campaign
15,000 sites hacked for massive Google SEO poisoning campaignHackers are conducting a massive black hat search engine optimization (SEO) campaign by compromising almost 15,000 websites to...
Secure Shadow IT
Secure Shadow ITAn astonishing 98% of cloud services are adopted without any IT oversight. And when your employees act as their own tech professionals to use...
Smashing Security podcast #297: Mastodon 101, and the Hushpuppi saga
Smashing Security podcast #297: Mastodon 101, and the Hushpuppi sagaGraham offers some security and privacy advice for those exodusing Twitter to Mastodon, and Carole slams the...