Misconfigured Server Exposed PHI of 600,000 InmatesClaims Processing Firm Says Affected Data Is Up to a Decade or More OldA server misconfiguration at Kentucky-based CorrectCare Integrated...
ExtraHop Taps Ex-Check Point Exec Chris Scanlan as President
ExtraHop Taps Ex-Check Point Exec Chris Scanlan as PresidentScanlan Wants to Get NDR Vendor to $500M ARR by Revamping the Go-to-Market PlanExtraHop has snagged high-profile Check...
Iranian Hacker Group Uses Log4Shell to Cryptojack US Agency
Iranian Hacker Group Uses Log4Shell to Cryptojack US AgencyHackers Exploited an Unpatched VMWare Horizon Server to Gain AccessIranian hackers used Log4Shell to penetrate the network of...
European Orgs Targeted with DTrack by North Korean Hacking Group Lazarus
European Orgs Targeted with DTrack by North Korean Hacking Group LazarusEuropean and Latin American organizations are at risk. North Korean hacking group Lazarus is using a...
The Importance of Responsible E-Waste Disposal for Enterprise Cybersecurity
The Importance of Responsible E-Waste Disposal for Enterprise CybersecurityAn Outline of the Importance of Proper E-Waste Disposal for Enterprise Best Practices in terms of both CSR...
Why Cybersecurity Is Critical for ESG
Why Cybersecurity Is Critical for ESGCyber-Awareness Can Help Companies Meet Esg Obligations By Shaun McAlmont, CEO, NINJIO One of the most important trends […] The post...
Pilfered Keys: Free App Infected by Malware Steals Keychain Data
Pilfered Keys: Free App Infected by Malware Steals Keychain DataOpen-source applications are a practical way to save money while keeping up with your productivity. However, this...
Electricity/Energy Cybersecurity: Trends & Survey Response
Electricity/Energy Cybersecurity: Trends & Survey ResponseBased on our survey of over 900 ICS security leaders in the United States, Germany, and Japan, we dig deeper into...
Windows Kerberos authentication breaks after November updates
Windows Kerberos authentication breaks after November updatesMicrosoft is investigating a new known issue causing enterprise domain controllers to experience Kerberos sign-in failures and other authentication problems...
42,000 sites used to trap users in brand impersonation scheme
42,000 sites used to trap users in brand impersonation schemeA malicious for-profit group named 'Fangxiao' has created a massive network of over 42,000 web domains that...
Microsoft fixes Windows DirectAccess connectivity issues
Microsoft fixes Windows DirectAccess connectivity issuesMicrosoft has resolved a known issue causing connectivity problems for Windows customers using the DirectAccess service to access their organizations remotely...
DuckDuckGo now lets all Android users block trackers in their apps
DuckDuckGo now lets all Android users block trackers in their appsDuckDuckGo for Android's 'App Tracking Protection' feature has reached open beta, allowing all Android users to...
‘Really poor form’: Medibank yet to contact hundreds of customers with leaked personal data
‘Really poor form’: Medibank yet to contact hundreds of customers with leaked personal dataCustomers whose personal details – but not medical information – were posted online...
Ransomware Attackers Don’t Take Holidays
Ransomware Attackers Don’t Take HolidaysCybereason's Sam Curry on the Financial and Business Impact of After-Hours StrikesCyber attackers love to strike on weekends and holidays - that's...
BSidesKC 2022 – Joshua Brown’s ‘So, You Want To Be A CISO…?’
BSidesKC 2022 – Joshua Brown’s ‘So, You Want To Be A CISO…?’Our sincere thanks to [BSidesKC 2022][1] for publishing their [outstanding conference videos][2] on the organization's...
Best Strategies For Stopping Business Email Compromise (BEC) Scams
Best Strategies For Stopping Business Email Compromise (BEC) ScamsAlso known as a 'man-in-the-email' attack, a BEC scam is intended to defraud companies, their customers, partners, and...
Stories from the Field: The Scare Factor Continues to Grow for Super Malicious Insiders
Stories from the Field: The Scare Factor Continues to Grow for Super Malicious InsidersOver the last few years, executive teams and board members have become increasingly...
This was 3rd Quarter 2022 — A Cybersecurity Look Back
This was 3rd Quarter 2022 — A Cybersecurity Look BackIn the third quarter of 2022, the four universal cyberattack drivers were accounted for: war, religion, politics...
Meta’s new kill chain model tackles online threats
Meta’s new kill chain model tackles online threatsIn April 2014, Lockheed Martin revolutionized the cyber defense business by publishing a seminal white paper Intelligence-Driven Computer Network...
New Updates for ESET’s Advanced Home Solutions
New Updates for ESET's Advanced Home SolutionsIt's no secret that antivirus software is as essential to your computer as a power cord. However, the threats don't...
Multiple High-Severity Flaws Affect Widely Used OpenLiteSpeed Web Server Software
Multiple High-Severity Flaws Affect Widely Used OpenLiteSpeed Web Server SoftwareMultiple high-severity flaws have been uncovered in the open source OpenLiteSpeed Web Server as well as its...
Russian-Canadian National Charged Over Involvement in LockBit Ransomware Attacks
Russian-Canadian National Charged Over Involvement in LockBit Ransomware AttacksThe U.S. Department of Justice (DoJ) has announced charges against a dual Russian and Canadian national for his...
Experts Uncover Two Long-Running Android Spyware Campaigns Targeting Uyghurs
Experts Uncover Two Long-Running Android Spyware Campaigns Targeting UyghursTwo long-running surveillance campaigns have been found targeting the Uyghur community in China and elsewhere with Android spyware...
Malicious Google Play Store App Spotted Distributing Xenomorph Banking Trojan
Malicious Google Play Store App Spotted Distributing Xenomorph Banking TrojanGoogle has removed two new malicious dropper apps that have been detected on the Play Store for...
VPN vs. DNS Security
VPN vs. DNS SecurityWhen you are trying to get another layer of cyber protection that would not require a lot of resources, you are most likely...
New KmsdBot Malware Hijacking Systems for Mining Crypto and Launch DDoS Attacks
New KmsdBot Malware Hijacking Systems for Mining Crypto and Launch DDoS AttacksA newly discovered evasive malware leverages the Secure Shell (SSH) cryptographic protocol to gain entry...
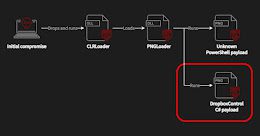
Worok Hackers Abuse Dropbox API to Exfiltrate Data via Backdoor Hidden in Images
Worok Hackers Abuse Dropbox API to Exfiltrate Data via Backdoor Hidden in ImagesA recently discovered cyber espionage group dubbed Worok has been found hiding malware in seemingly innocuous...
Global 2000 companies failing to adopt key domain security measures
Global 2000 companies failing to adopt key domain security measuresForbes Global 2000 companies are failing to adopt key domain security measures, exposing them to significant security...
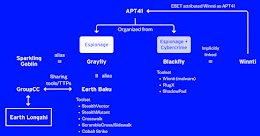
New “Earth Longzhi” APT Targets Ukraine and Asian Countries with Custom Cobalt Strike Loaders
New "Earth Longzhi" APT Targets Ukraine and Asian Countries with Custom Cobalt Strike LoadersEntities located in East and Southeast Asia as well as Ukraine have been...
Over 15,000 WordPress Sites Compromised in Malicious SEO Campaign
Over 15,000 WordPress Sites Compromised in Malicious SEO CampaignA new malicious campaign has compromised over 15,000 WordPress websites in an attempt to redirect visitors to bogus Q&A portals....