Australian special forces member allegedly stole and published personal data of intelligence officialADF is investigating alleged theft and use of cybertools to hack private accounts of...
Mobiles are ‘potential goldmines’ for hostile states, MPs warned
Mobiles are ‘potential goldmines’ for hostile states, MPs warnedCommons speaker suggests phones not be taken into meetings as UK cyber security centre issues 10 ‘top tips’...
Palo Alto Networks to Buy Cider Security for $300M: Report
Palo Alto Networks to Buy Cider Security for $300M: ReportPalo Alto's First Big M&A Since Early 2021 Will Help Secure Engineering ProcessesPalo Alto Networks will make...
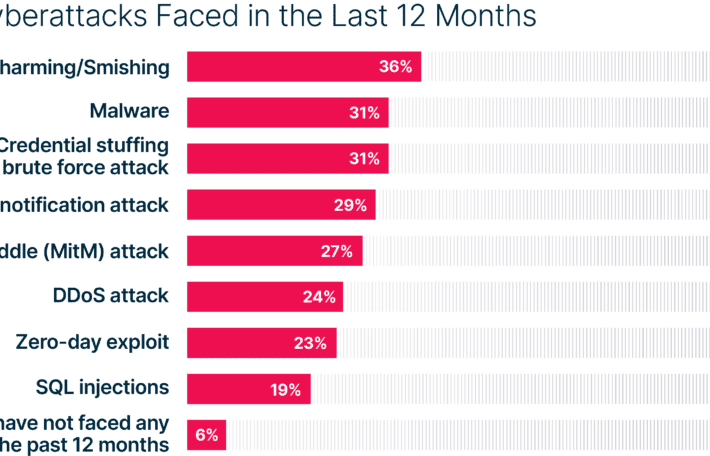
Global Cyber Risk at Elevated Level
Global Cyber Risk at Elevated LevelNorth America Least Prepared for CyberattacksLeer másTrend Micro Research, News, PerspectivesNorth America Least Prepared for Cyberattacks
Smashing Security podcast #298: Housing market scams, Twitter 2FA, and the fesshole
Smashing Security podcast #298: Housing market scams, Twitter 2FA, and the fessholeElon Musk is still causing chaos at Twitter (and it's beginning to impact users), are...
Department of Financial Services Proposes Cybersecurity Regulation Updates
Department of Financial Services Proposes Cybersecurity Regulation UpdatesEarlier this month, Superintendent of Financial Services Adrienne A. Harris announced that the New York State Department of Financial...
Botnets, Trojans, DDoS From Ukraine and Russia Have Increased Since Invasion
Botnets, Trojans, DDoS From Ukraine and Russia Have Increased Since InvasionThe news comes from a report by Top10VPN and is based on data by the Shadowserver...
Iran-linked threat actors compromise US Federal Network
Iran-linked threat actors compromise US Federal NetworkIran-linked threat actors compromised a Federal Civilian Executive Branch organization using a Log4Shell exploit and installed a cryptomining malware. According...
Majority of Companies Reduce Cybersecurity Staff Over Holidays
Majority of Companies Reduce Cybersecurity Staff Over HolidaysCybereason’s latest report is based on a survey of more than 1200 cybersecurity professionalsLeer másCybereason’s latest report is based...
Higher Education Organization Improves Cybersecurity Posture with NodeZero
Higher Education Organization Improves Cybersecurity Posture with NodeZeroWhen the director of technology for a higher education organization went looking for a better way to identify and...
Scottish Embassy Guard in Berlin Caught Spying for Russia
Scottish Embassy Guard in Berlin Caught Spying for RussiaYou might wonder who in the world right now would be caught spying for Putin. Well have I...
Android Privacy Sandbox Beta to Roll Out By Early 2023
Android Privacy Sandbox Beta to Roll Out By Early 2023The project aims to bring new and more private advertising solutions to mobileLeer másThe project aims to...
Open banking: Tell me what you buy, and I’ll tell you who you are
Open banking: Tell me what you buy, and I’ll tell you who you areThe convenience with which you manage all your financial wants and needs may...
It’s Official. Tesla Has Reduced Driver Safety
It’s Official. Tesla Has Reduced Driver SafetyYou may recall that Elon Musk was a CEO fired from PayPal for his gross incompetence. Somehow he kept all...
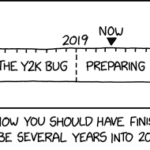
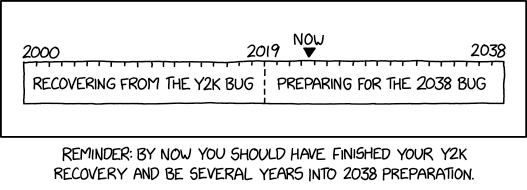
Randall Munroe’s XKCD ‘Y2K And 2038’
Randall Munroe’s XKCD ‘Y2K And 2038’Randall Munroe’s XKCD ‘Y2K And 2038’ via the comic artistry and dry wit of Randall Munroe, resident at XKCD! Permalink The...
WWII British Soldiers Successfully Deployed God and Sugar to Defeat Nazi Disinformation
WWII British Soldiers Successfully Deployed God and Sugar to Defeat Nazi DisinformationIt’s really a footnote to stories about Nazi Germany losing the war in 1942, yet...
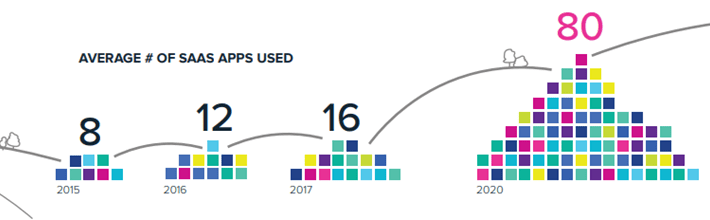
A Detailed Orientation To SaaS Application and its Security Aspect
A Detailed Orientation To SaaS Application and its Security AspectWith the enormous utilization of the internet and business goals to save additional expenses, SaaS applications are...
High Severity Vulnerabilities Reported in F5 BIG-IP and BIG-IQ Devices
High Severity Vulnerabilities Reported in F5 BIG-IP and BIG-IQ DevicesMultiple security vulnerabilities have been disclosed in F5 BIG-IP and BIG-IQ devices that, if successfully exploited, to...
Iranian Hackers Compromised a U.S. Federal Agency’s Network Using Log4Shell Exploit
Iranian Hackers Compromised a U.S. Federal Agency’s Network Using Log4Shell ExploitIranian government-sponsored threat actors have been blamed for compromising a U.S. federal agency by taking advantage...
North Korean Hackers Targeting Europe and Latin America with Updated DTrack Backdoor
North Korean Hackers Targeting Europe and Latin America with Updated DTrack BackdoorHackers tied to the North Korean government have been observed using an updated version of...
DAST tools as force multipliers for human cybersecurity skills
DAST tools as force multipliers for human cybersecurity skillsModern DAST tools help humans and technology work together at peak efficiency, allowing development and security teams to...
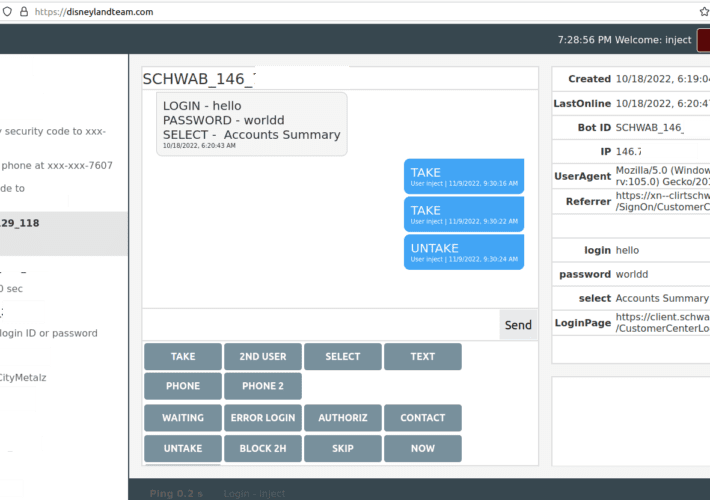
Disneyland Malware Team: It’s a Puny World After All
Disneyland Malware Team: It’s a Puny World After AllA financial cybercrime group calling itself the Disneyland Team has been making liberal use of visually confusing phishing...
Creating a culture of giving back
Creating a culture of giving back{{consumer="/components/cta/consumer"}} The team at the J.P. Morgan Corporate Challenge in 2015. It’s been almost two years since I moved from Boston...
Randall Munroe’s XKCD ‘Y2K And 2038’
Randall Munroe’s XKCD ‘Y2K And 2038’ via the comic artistry and dry wit of Randall Munroe, resident at XKCD! Permalink The post Randall Munroe’s XKCD ‘Y2K...
Why Cyber Risk in Critical Infrastructure Needs to be Understood and Prioritized
Why Cyber Risk in Critical Infrastructure Needs to be Understood and PrioritizedPart 1 of Axio’s multi-part series on cyber risk in critical infrastructure - why it’s...
Construction Firm Strengthens its ITDR Foundation with Purple Knight
Construction Firm Strengthens its ITDR Foundation with Purple KnightBetween remote users and contractors, construction company Maple Reinders needed to get control of Active Directory (AD) user...
Physical Threat Assessment: What to Know About the 2022 Qatar World Cup
Physical Threat Assessment: What to Know About the 2022 Qatar World CupFrom accusations of human rights abuses and corruption to negative reactions from religious extremists, the...
New Paradigm in Endpoint Protection
New Paradigm in Endpoint ProtectionDevice security has evolved over the last 10-20 years. With new devices (employee-owned smartphones) and new technologies (SaaS and the cloud), the...
Why Security & IT Teams in the Financial Industry Are Under Enormous Strain
Why Security & IT Teams in the Financial Industry Are Under Enormous StrainSecurity and IT teams in the financial services industry face incredible pressure to shore...
Researchers Discover Hundreds of Amazon RDS Instances Leaking Users’ Personal Data
Researchers Discover Hundreds of Amazon RDS Instances Leaking Users' Personal DataHundreds of databases on Amazon Relational Database Service (Amazon RDS) are exposing personal identifiable information (PII),...