Data Privacy and Remote Work: Three Things Businesses Need to Know Due to the COVID-19 pandemic, a large-scale and abrupt shift in employee work habits from...
People Are People: Gender Equality at Praetorian
People Are People: Gender Equality at PraetorianEarly this Summer, we shared our thoughts on the industry-wide shortage of cybersecurity talent to meet an ever-growing demand. One...
FBI-Wanted Leader of the Notorious Zeus Botnet Gang Arrested in Geneva
FBI-Wanted Leader of the Notorious Zeus Botnet Gang Arrested in GenevaA Ukrainian national who has been wanted by the U.S for over a decade has been...
Chinese Spy Gets 20 Years for Aviation Espionage Plot
Chinese Spy Gets 20 Years for Aviation Espionage PlotUS authorities land a rare win in fight against state-backed info-theftLeer másUS authorities land a rare win in...
100 Apps, Endless Security Checks
100 Apps, Endless Security ChecksOn average, organizations report using 102 business-critical SaaS applications, enabling operations of most departments across an organization, such as IT and Security, Sales, Marketing,...
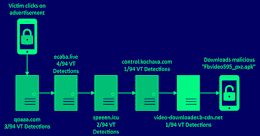
Chinese Hackers Using 42,000 Imposter Domains in Massive Phishing Attack Campaign
Chinese Hackers Using 42,000 Imposter Domains in Massive Phishing Attack CampaignA China-based financially motivated group is leveraging the trust associated with popular international brands to orchestrate...
Black Friday and retail season – watch out for PayPal “money request” scams
Black Friday and retail season – watch out for PayPal “money request” scamsDon't let a keen eye for bargains lead you into risky online behaviour...Leer másNaked...
US: Iranian Hackers Breached Government with Log4Shell
US: Iranian Hackers Breached Government with Log4ShellThreat actors installed crypto-miner and achieved persistenceLeer másThreat actors installed crypto-miner and achieved persistence
FBI issues warning over impersonation scam; New phishing campaign encourages targets to call malicious actors
FBI issues warning over impersonation scam; New phishing campaign encourages targets to call malicious actorsPhishing emails continue to be sent in high volumes. Earthweb has identified...
PCI Council Launches Flexible Mobile Payments Standard
PCI Council Launches Flexible Mobile Payments StandardAnnouncement recognizes growing volume of smartphone paymentsLeer másAnnouncement recognizes growing volume of smartphone payments
Android security: Which smartphones can enterprises trust?
Android security: Which smartphones can enterprises trust?Google’s Android operating system dominates smartphone usage throughout the world — in every region except North America and Oceania, in...
Cybersecurity Industry Must Maintain Public Faith in Technology, Says NCSC Founder
Cybersecurity Industry Must Maintain Public Faith in Technology, Says NCSC FounderThe NCSC's founding CEO, Ciaran Martin, explains why the cyber industry is now a public goodLeer...
MFA Fatigue Attacks Are on the Rise
MFA Fatigue Attacks Are on the RiseMFA Fatigue seems to be hackers` favorite tool this fall, as we have lately witnessed an increase in numbers of...
More Than Half of Black Friday Spam Emails Are Scams
More Than Half of Black Friday Spam Emails Are ScamsNew research analyzes email scam techniques in the build-up to this year's Black FridayLeer másNew research analyzes...
Hundreds of Amazon RDS Snapshots Discovered Leaking Users’ Data
Hundreds of Amazon RDS Snapshots Discovered Leaking Users' DataThe discovery was made by security researchers at MitigaLeer másThe discovery was made by security researchers at Mitiga
How to Prevent Privilege Escalation Attacks?
How to Prevent Privilege Escalation Attacks?Privilege escalation, like any cyberattack, takes advantage of flaws in network services and applications, especially those with weak access control systems....
Massive Wave of TrojanOrders Attacks Target Magento Stores
Massive Wave of TrojanOrders Attacks Target Magento StoresA significant increase in “TrojanOrders” attacks against Magento 2 websites is being attributed to at least seven hacker groups....
A U.S. Federal Agency Was the Victim of Iranian Government-Sponsored Hackers
A U.S. Federal Agency Was the Victim of Iranian Government-Sponsored HackersState-supported Iranian cybercriminals are suspected in an incident that led to a breach in a U.S....
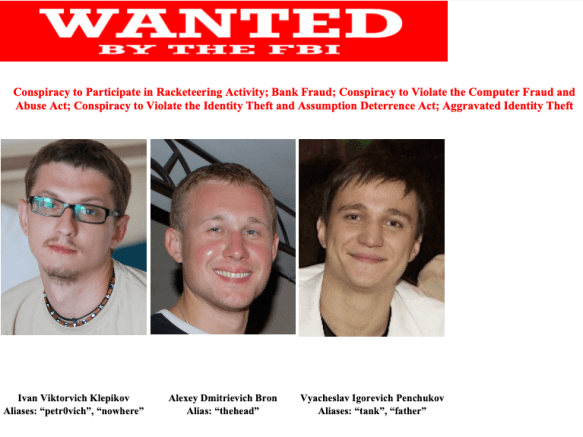
Tank, the leader of the Zeus cybercrime gang, was arrested by the Swiss police
Tank, the leader of the Zeus cybercrime gang, was arrested by the Swiss policeA suspected leader of the Zeus cybercrime gang, Vyacheslav Igorevich Penchukov (aka Tank), was...
Emotet Targets New Victims: Amazon, DHL, and the Ukrainian War
Emotet Targets New Victims: Amazon, DHL, and the Ukrainian WarAlthough other malware families are still prevalent and dangerous, Emotet has climbed to the top of the...
Suspected Leader of Zeus Cybercrime Gang Arrested in Switzerland
Suspected Leader of Zeus Cybercrime Gang Arrested in SwitzerlandOne of the leaders of the renowned JabberZeus cybercrime group, Vyacheslav Igorevich Penchukov (aka Tank), was detained in...
Microsoft fixes bug behind Windows 10 freezes, desktop issues
Microsoft fixes bug behind Windows 10 freezes, desktop issuesMicrosoft has resolved a known issue triggering errors and temporarily causing the taskbar and desktop to disappear on...
Failures in Twitter’s Two-Factor Authentication System
Failures in Twitter’s Two-Factor Authentication SystemTwitter is having intermittent problems with its two-factor authentication system: Not all users are having problems receiving SMS authentication codes, and...
U.S. charges Russian suspects with operating Z-Library e-Book site
U.S. charges Russian suspects with operating Z-Library e-Book siteAnton Napolsky (33) and Valeriia Ermakova (27), two Russian nationals, were charged with intellectual property crimes linked to...
Everything You Need to Know to Avoid a Man-in-the-Middle Mobile Attack
Everything You Need to Know to Avoid a Man-in-the-Middle Mobile Attack Monkey in the middle, the beloved playground staple, extends beyond schoolyards into corporate networks, home...
What Is Internet Security?
What Is Internet Security? Internet security is a broad term that refers to a wide range of tactics that aim to protect activities conducted over the...
What Is Bloatware and How Can It Impact Security?
What Is Bloatware and How Can It Impact Security? The joy of purchasing a new device is liberating. Now you can work, learn, and play faster...
Microsoft urges devs to migrate away from .NET Core 3.1 ASAP
Microsoft urges devs to migrate away from .NET Core 3.1 ASAPMicrosoft has urged developers still using the long-term support (LTS) release of .NET Core 3.1 to migrate to the...
ESET rolls out new consumer offerings to improve home security
ESET rolls out new consumer offerings to improve home securityESET's newest consumer product release has taken a comprehensive approach to security to guard against a full...
F5 fixes two remote code execution flaws in BIG-IP, BIG-IQ
F5 fixes two remote code execution flaws in BIG-IP, BIG-IQF5 has released hotfixes for its BIG-IP and BIG-IQ products, addressing two high-severity flaws allowing attackers to...