Android file manager apps infect thousands with Sharkbot malwareA new collection of malicious Android apps posing as harmless file managers had infiltrated the official Google Play...
Harris Center ISO perspective: Product evaluation, board engagement & career advice
Harris Center ISO perspective: Product evaluation, board engagement & career adviceIn this interview, Wes Farris, Information Security Officer for the Harris Center for Mental Health and...
FIRESIDE CHAT: Anchoring security on granular visibility, proactive management of all endpoints
FIRESIDE CHAT: Anchoring security on granular visibility, proactive management of all endpointsEndpoints are where all are the connectivity action is. Related: Ransomware bombardments And securing endpoints...
Covering Data Breaches in an Ethical Way
Covering Data Breaches in an Ethical WayHow Do We Avoid Data Dump Voyeurism and Victim Shaming?Data breaches are tricky to cover, and we want to report...
Cybersecurity Analysis of the FTX Crypto Heist: Part Two
Cybersecurity Analysis of the FTX Crypto Heist: Part TwoOn the heels of the recent FTX financial meltdown came the theft of millions of dollars that left...
K05403841: BIG-IP and BIG-IQ improvements disclosed by Rapid7
K05403841: BIG-IP and BIG-IQ improvements disclosed by Rapid7BIG-IP and BIG-IQ improvements disclosed by Rapid7 Security Advisory Security Advisory Description BIG-IP and BIG-IQ improvements disclosed by Rapid7...
Digital Army 2030: US Army Modernizes Technology at Scale: Part 1
Digital Army 2030: US Army Modernizes Technology at Scale: Part 1In the first episode of this exclusive two-part series, Dr. Raj Iyer, CIO of the U.S....
Central Depository Attack Delays Trade Settlement in India
Central Depository Attack Delays Trade Settlement in IndiaSystems Are Back Online But Brokers Say Some Systems Are Still AffectedTrade-related services resumed Monday at Central Depository Services...
Chinese APT Using Google Drive, Dropbox to Drop Malware
Chinese APT Using Google Drive, Dropbox to Drop MalwareEvolved Mustang Panda Malware Targets Government, Education, Other Sectors GloballyA large-scale cyberespionage campaign by notorious China-based advanced persistent...
5 Hospital Workers Charged with Selling Patient Information
5 Hospital Workers Charged with Selling Patient InformationData of Patients Hurt in Auto Accidents Allegedly Sold to Chiropractors, AttorneysAuthorities charged six people, including five former Tennessee...
RSA CEO Rohit Ghai on Authenticating Users to Mobile Devices
RSA CEO Rohit Ghai on Authenticating Users to Mobile DevicesHow to Defend BYOD Devices Without Installing Software or Creating FrictionThe divide between mobile app detection and...
GUEST ESSAY: The rising need to defend against super hackers, master thieves and digital ghosts
GUEST ESSAY: The rising need to defend against super hackers, master thieves and digital ghostsConsider what might transpire if malicious hackers began to intensively leverage Artificial...
GUEST ESSAY — Security practices companies must embrace to stop AI-infused cyber attacks
GUEST ESSAY — Security practices companies must embrace to stop AI-infused cyber attacksConsider what might transpire if malicious hackers began to intensively leverage Artificial Intelligence (AI)...
Building a World-Class eSIM Registration Process
Building a World-Class eSIM Registration ProcessTelcos are part of the vital infrastructure that serves as a forerunner for the rest of the industry as their digital...
Aviation Starting to Get Hit with Rise of Cyberattacks Post-Pandemic
Aviation Starting to Get Hit with Rise of Cyberattacks Post-PandemicThreat actors are turning their attention to the aviation industry post-pandemic, but what motivations and challenges are...
What is Security Service Edge(SSE) and How Does It Help to Achieve SASE?
What is Security Service Edge(SSE) and How Does It Help to Achieve SASE?Introduction Every technology has its downside. Likewise, internet use also has its drawback of...
Fall lawn cleaning – AppSec style | Contrast Security
Fall lawn cleaning – AppSec style | Contrast Security Every year toward the end of September, I get anxious about the falling leaves. This year, I...
Google Wins Lawsuit Against Russians Linked to Blockchain-based Glupteba Botnet
Google Wins Lawsuit Against Russians Linked to Blockchain-based Glupteba BotnetGoogle has won a lawsuit filed against two Russian nationals in connection with the operation of a...
Webinar – Manage “Achieving DOD Impact Level 4 – Lessons Learned & Much More”
Webinar – Manage “Achieving DOD Impact Level 4 – Lessons Learned & Much More”If you are an ISV or SaaS solutions provider looking to pursue US...
Google Identifies 34 Cracked Versions of Popular Cobalt Strike Hacking Toolkit in the Wild
Google Identifies 34 Cracked Versions of Popular Cobalt Strike Hacking Toolkit in the WildGoogle Cloud last week disclosed that it identified 34 different hacked release versions...
Supreme Court to Consider Identity Theft Case
Supreme Court to Consider Identity Theft Case William Dubin, a licensed psychologist in Austin, Texas, provided psychological services to a youth facility known as Williams House....
Been Doing It The Same Way For Years? Think Again.
Been Doing It The Same Way For Years? Think Again.[Want Bob to stop complaining? Change your practices.] [Don't delay change – it can cost you] ["Always...
How to Add DMARC Record in Namecheap
How to Add DMARC Record in NamecheapFor any organization, its email infrastructure must be crucial. The first step to start protecting your domain for your clients,...
Achieve Defense-in-Depth in Multi-Cloud Environments
Achieve Defense-in-Depth in Multi-Cloud Environments Today, 90% of organizations are operating in hybrid and multi-cloud environments—a number that has increased over the past two years due...
How remote working impacts security incident reporting
How remote working impacts security incident reportingThe ability for employees to work remotely comes with many benefits, from better work-life balance to lower expenses to higher...
Tor vs. VPN: Which should you choose?
Tor vs. VPN: Which should you choose?Both Tor and a VPN can greatly help you keep prying eyes away from your online life, but they’re also...
Netflix Phishing Emails Surge 78%
Netflix Phishing Emails Surge 78%Social engineers are using Unicode techniques to bypass filtersLeer másSocial engineers are using Unicode techniques to bypass filters
CISA, NSA, ODNI Publish Software Supply Chain Guidelines For Customers
CISA, NSA, ODNI Publish Software Supply Chain Guidelines For CustomersThe come after the August release of guidance for developers and the October one for suppliersLeer másThe...
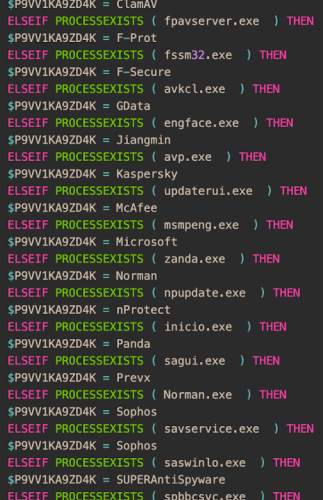
New improved versions of LodaRAT spotted in the wild
New improved versions of LodaRAT spotted in the wildCisco Talos spotted multiple updated versions of LodaRAT that were deployed alongside other malware families, including RedLine and...
Emerging Threat Actor DEV-0569 Expands Its Toolkit to Deliver Royal Ransomware
Emerging Threat Actor DEV-0569 Expands Its Toolkit to Deliver Royal RansomwareAs well as malvertising and phishing links, the new threat actor is now also using contact...