How to hack an unpatched Exchange server with rogue PowerShell codeReview your servers, your patches and your authentication policies - there's a proof-of-concept outLeer másNaked SecurityReview...
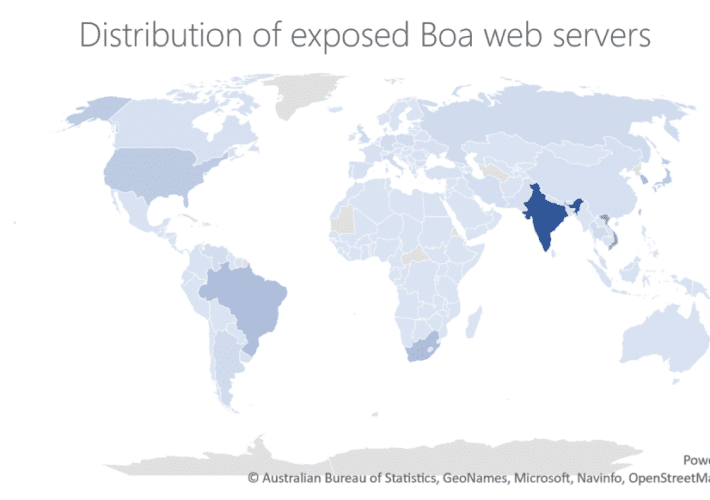
Discontinued Server Flaws Used by Hackers to Target Energy Orgs
Discontinued Server Flaws Used by Hackers to Target Energy OrgsFlaws from a web server discontinued since 2005 have been used to attack organizations from the energy...
CryptoRom “pig butchering” scam sites seized, suspects arrested in US
CryptoRom “pig butchering” scam sites seized, suspects arrested in USFive tips to keep yourself, and your friends and family, out of the clutches of "chopping block"...
Speed up your computer with these 5 quick tips
Speed up your computer with these 5 quick tips When you turn on your computer in the morning, do you have enough time to brew a...
Happy Thanksgiving 2022
Happy Thanksgiving 2022Image courtesy of the Veterans of Foreign Wars The post Happy Thanksgiving 2022 appeared first on Security Boulevard. Leer másSecurity BoulevardImage courtesy of the...
SharkBot Malware Infects Thousands Of Android Users With A Hidden File Manager App
SharkBot Malware Infects Thousands Of Android Users With A Hidden File Manager AppThe latest surge of Android apps making their way onto the Google Play app...
Introducing Security Spotlights
Introducing Security SpotlightsGain the Cybersecurity Insights Needed to Reduce Noise, Prioritize Work and Quickly Secure Your Environment. Your cybersecurity needs are constantly changing as cybersecurity threats...
EPSS explained: How does it compare to CVSS?
EPSS explained: How does it compare to CVSS?The Common Vulnerability Scanning System (CVSS) is the most frequently cited rating system to assess the severity of security...
Exclusive – Quantum Locker lands in the Cloud
Exclusive – Quantum Locker lands in the CloudThe gang behind Quantum Locker used a particular modus operandi to target large enterprises relying on cloud services in...
Hackers Are Increasingly Using Aurora Infostealer Malware
Hackers Are Increasingly Using Aurora Infostealer MalwareThreat actors are increasingly using a new information stealer known as “Aurora”, written in the Go programming language to exfiltrate...
DUCKTAIL malware campaign targeting Facebook business and ads accounts is back
DUCKTAIL malware campaign targeting Facebook business and ads accounts is backA group of attackers, likely based in Vietnam, that specializes in targeting employees with potential access...
Microsoft releases out-of-band update to fix Kerberos auth issues caused by a patch for CVE-2022-37966
Microsoft releases out-of-band update to fix Kerberos auth issues caused by a patch for CVE-2022-37966Microsoft released an out-of-band update to fix problems tied to a recent...
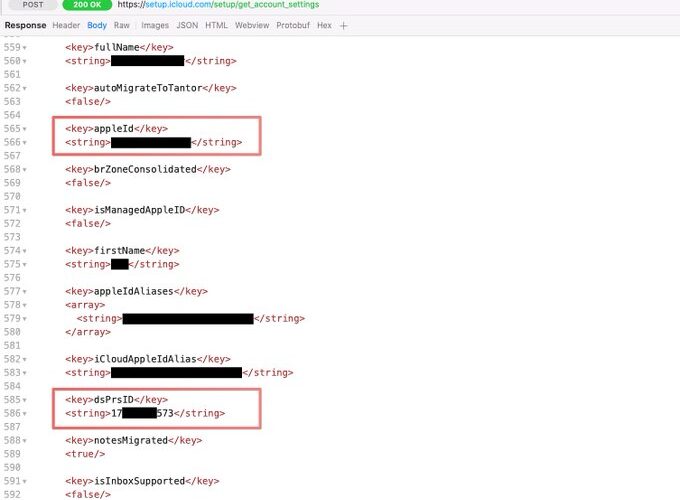
Experts claim that iPhone’s analytics data is not anonymous
Experts claim that iPhone’s analytics data is not anonymousResearchers discovered that analytics data associated with iPhone include Directory Services Identifier (DSID) that could allow identifying users....
Top Cybersecurity Trends – Current Landscape and 2023 Predictions
Top Cybersecurity Trends – Current Landscape and 2023 PredictionsThe last few years have been truly transformational, and as 2023 approaches, you may be wondering what will...
Pro-Russian group Killnet claims responsibility for DDoS attack that has taken down the European Parliament site
Pro-Russian group Killnet claims responsibility for DDoS attack that has taken down the European Parliament sitePro-Russian hacker collective Killnet took down the European Parliament website with...
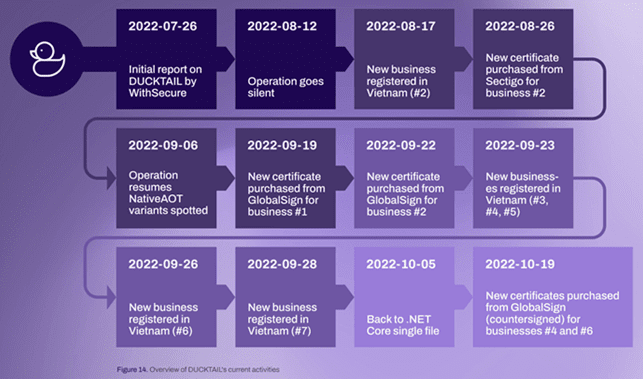
Ducktail information stealer continues to evolve
Ducktail information stealer continues to evolveThe operators behind the Ducktail information stealer continue to improve their malicious code, operators experts warn. In late July 2022, researchers...
Microsoft Email Security Eluded by Instagram Credential Phishing Attacks
Microsoft Email Security Eluded by Instagram Credential Phishing AttacksMalicious actors operated a brand impersonation phishing campaign on 22,000 students and managed to bypass the Microsoft email...
Russian DDoS Briefly Downs European Parliament Site
Russian DDoS Briefly Downs European Parliament SiteParliament had declared Russia a state-sponsor of terrorismLeer másParliament had declared Russia a state-sponsor of terrorism
UK Cops Lead Action Against Fraud Site that Made £100m+
UK Cops Lead Action Against Fraud Site that Made £100m+Over 100 admins and users of iSpoof site arrestedLeer másOver 100 admins and users of iSpoof site...
Threat actors exploit discontinues Boa web servers to target critical infrastructure
Threat actors exploit discontinues Boa web servers to target critical infrastructureMicrosoft reported that hackers have exploited flaws in a now-discontinued web server called Boa in attacks against...
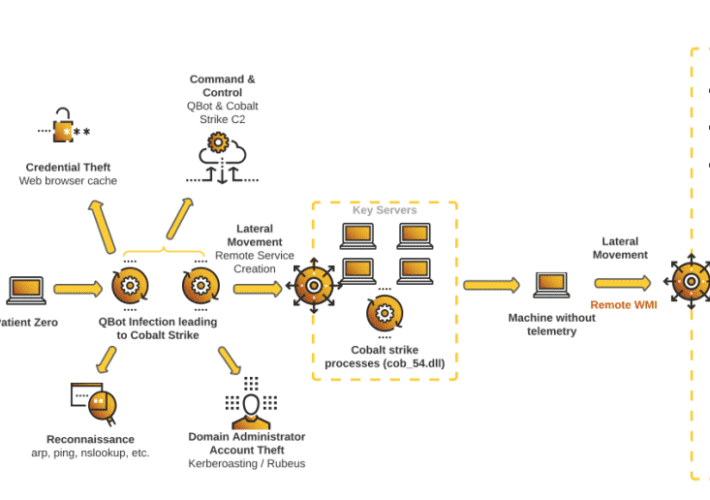
An aggressive malware campaign targets US-based companies with Qakbot to deliver Black Basta Ransomware
An aggressive malware campaign targets US-based companies with Qakbot to deliver Black Basta RansomwareResearchers warn of an ongoing aggressive Qakbot malware campaign that leads to Black...
The Anatomy of PTaaS: What Is Penetration Testing as a Service
The Anatomy of PTaaS: What Is Penetration Testing as a ServiceIn this article, we’ll go over what penetration testing as a service is and how it...
EU Parliament Site Attacked by Russian Hacktivists
EU Parliament Site Attacked by Russian HacktivistsThe European Parliament’s official website was taken down for hours on Wednesday, November 23, by a DDoS attack. The attack...
Black Basta Ransomware Gang Infiltrates U.S. Companies via Qakbot Malware
Black Basta Ransomware Gang Infiltrates U.S. Companies via Qakbot MalwareAffiliates of Black Basta gang are notorious for employing the banking trojan known as QakBot for initial...
Sales Director (US)
Sales Director (US)Our Perfect Candidate You are a self-starter with strong attention to detail and the ability to work in a fast-paced environment. You possess...
Smashing Security podcast #299: EV charging risks, FTX, and an ancient apocalypse
Smashing Security podcast #299: EV charging risks, FTX, and an ancient apocalypseDeepfake shenanigans strike users of troubled crypto firm FTX, the perils of charging your electric...
Revising your backup strategy in 2023
Revising your backup strategy in 2023The data backup strategies that prevent loss and protect suspension of company activitiesLeer másArticles RSS FeedThe data backup strategies that prevent...
6 simple & straightforward Cyber Monday fraud prevention tips
6 simple & straightforward Cyber Monday fraud prevention tipsEXECUTIVE SUMMARY: Starting on November 28th, Cyber Monday is the season’s second-major shopping event, second-only to Black Friday,...
MSA-22-0032: Blind SSRF risk in LTI provider library
MSA-22-0032: Blind SSRF risk in LTI provider libraryby Michael Hawkins. Moodles LTI provider library did not utilise Moodles inbuilt cURL helper, which resulted in a blind...
K91021753: Apache MINA vulnerability CVE-2022-45047
K91021753: Apache MINA vulnerability CVE-2022-45047Apache MINA vulnerability CVE-2022-45047 Security Advisory Security Advisory Description Class org.apache.sshd.server.keyprovider.SimpleGeneratorHostKeyProvider in Apache MINA SSHD <= 2.9.1 uses ... More info: https://support.f5.com/csp/article/K91021753?utm_source=f5support&utm_medium=RSSLeer...