F5 expands security portfolio with App Infrastructure ProtectionF5 on Thursday announced the launch of F5 Distributed Cloud Services App Infrastructure Protection (AIP), expanding its SaaS-based security...
Microsoft Reclassifies SPNEGO Extended Negotiation Security Vulnerability as ‘Critical’
Microsoft Reclassifies SPNEGO Extended Negotiation Security Vulnerability as 'Critical'Microsoft has revised the severity of a security vulnerability it originally patched in September 2022, upgrading it to "Critical"...
BrandPost: How to Choose Security Technology That Works
BrandPost: How to Choose Security Technology That WorksThe role of a security practitioner is difficult. From operational workflow changes to accommodating the latest application requirement impacting...
Two-Thirds of Security Pros Have Burnt Out in Past Year
Two-Thirds of Security Pros Have Burnt Out in Past YearExcessive workload is the most common contributing factorLeer másExcessive workload is the most common contributing factor
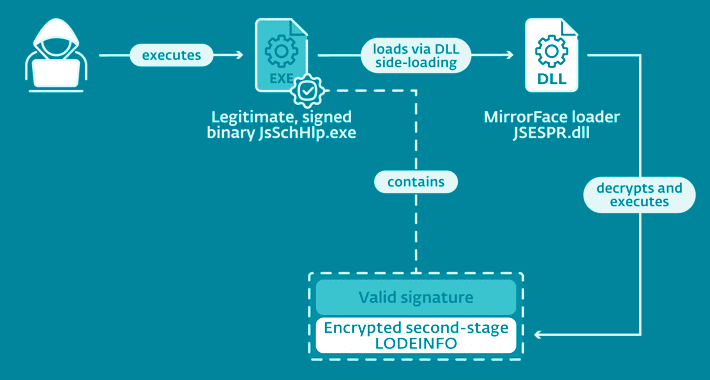
Researchers Uncover MirrorFace Cyber Attacks Targeting Japanese Political Entities
Researchers Uncover MirrorFace Cyber Attacks Targeting Japanese Political EntitiesA Chinese-speaking advanced persistent threat (APT) actor codenamed MirrorFace has been attributed to a spear-phishing campaign targeting Japanese political establishments....
CISA Alert: Veeam Backup and Replication Vulnerabilities Being Exploited in Attacks
CISA Alert: Veeam Backup and Replication Vulnerabilities Being Exploited in AttacksThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two vulnerabilities impacting Veeam Backup & Replication software...
MTTR “not a viable metric” for complex software system reliability and security
MTTR “not a viable metric” for complex software system reliability and securityMean time to resolve (MTTR) isn’t a viable metric for measuring the reliability or security...
Cybersecurity Insights with Contrast CISO David Lindner | 12/16
Cybersecurity Insights with Contrast CISO David Lindner | 12/16 Insight #1 " Lobbying from ITIC has pushed back on the recent OMB 22-18 directive to require...
Minecraft Servers Under Attack: Microsoft Warns About Cross-Platform DDoS Botnet
Minecraft Servers Under Attack: Microsoft Warns About Cross-Platform DDoS BotnetMicrosoft on Thursday flagged a cross-platform botnet that's primarily designed to launch distributed denial-of-service (DDoS) attacks against...
Goodbye SHA-1: NIST Retires 27-Year-Old Widely Used Cryptographic Algorithm
Goodbye SHA-1: NIST Retires 27-Year-Old Widely Used Cryptographic AlgorithmThe U.S. National Institute of Standards and Technology (NIST), an agency within the Department of Commerce, announced Thursday that it's...
S3 Ep113: Pwning the Windows kernel – the crooks who hoodwinked Microsoft [Audio + Text]
S3 Ep113: Pwning the Windows kernel – the crooks who hoodwinked Microsoft [Audio + Text]Return o' the rookit, super-sneaky wireless spyware, credit card skimming, and patches...
Nikesh Arora on Palo Alto’s Approach to Supply Chain Defense
Nikesh Arora on Palo Alto's Approach to Supply Chain DefenseThe $250 million acquisition of Cider Security will allow Palo Alto Networks to secure a piece of...
Combating Ransomware Attacks: Which Strategies Hold Promise?
Combating Ransomware Attacks: Which Strategies Hold Promise?Defenders have made strides in disrupting ransomware, but assessing the effectiveness of countermeasures is tough due to a scarcity of...
Assessing Cyber Risk, Maturity in Healthcare M&As
Assessing Cyber Risk, Maturity in Healthcare M&AsWhen healthcare organizations come together through mergers or acquisitions, it is critical for the entities to carefully assess the cyber...
How Criminals Extort Healthcare Victims With Ransomware
How Criminals Extort Healthcare Victims With RansomwareVictims Urged to Prepare Rather Than Pay, Especially for False Data-Wiping PromisesRansomware operations have become expert at finding ways to...
Patch Tuesday December 2022 – Microsoft Fixes Spoofing and Elevation of Privilege Vulnerabilities
Patch Tuesday December 2022 – Microsoft Fixes Spoofing and Elevation of Privilege VulnerabilitiesThe end of the year is here, and with it, Microsoft is trying to...
Dental Practice Hit With HIPAA Fine for Posting PHI on Yelp
Dental Practice Hit With HIPAA Fine for Posting PHI on YelpHHS Settlement Is Latest Involving Similar Social Media BlundersA California dental practice that for years revealed...
Indian Ministry of External Affairs Platform Leaked Expats’ Passport Information
Indian Ministry of External Affairs Platform Leaked Expats’ Passport InformationSensitive information, such as names and passport numbers, was exposed through the Global Pravasi Rishta Portal, India’s...
Microsoft Patches Zero-Day Magniber Ransomware Hackers Used
Microsoft Patches Zero-Day Magniber Ransomware Hackers UsedSecureScreen Treated Malformed Signature the Same as a Valid SignatureMicrosoft's last monthly dump of patches for 2022 includes a fix...
New Actively Exploited Zero-Day Vulnerability Discovered in Apple Products
New Actively Exploited Zero-Day Vulnerability Discovered in Apple ProductsEarlier this week, Apple released updates to reinforce their security against a new zero-day vulnerability that could lead...
EmoLoad: Loading Emotet Modules without Emotet
EmoLoad: Loading Emotet Modules without EmotetOur latest report exposing Emotet’s supply chain would not have been possible without custom-made tools, tailored to analyze the core Emotet...
Hacker Reportedly Breaches US FBI Cybersecurity Forum
Hacker Reportedly Breaches US FBI Cybersecurity ForumBureau Ushered a Phony CEO Who Stole Emails Into a Seat at InfraGardA hacker selling a data set purportedly containing...
K35253541: Java vulnerabilities CVE-2020-14779, CVE-2020-14781, CVE-2020-14782, CVE-2020-14797
K35253541: Java vulnerabilities CVE-2020-14779, CVE-2020-14781, CVE-2020-14782, CVE-2020-14797Java vulnerabilities CVE-2020-14779, CVE-2020-14781, CVE-2020-14782, CVE-2020-14797 Security Advisory Security Advisory Description CVE-2020-14779 Vulnerability in the Java SE, Java SE Embedded...
K71522481: Java vulnerability CVE-2021-2163
K71522481: Java vulnerability CVE-2021-2163Java vulnerability CVE-2021-2163 Security Advisory Security Advisory Description Vulnerability in the Java SE, Java SE Embedded, Oracle GraalVM Enterprise Edition product of Oracle...
Microsoft: Windows 10 21H1 has reached end of servicing
Microsoft: Windows 10 21H1 has reached end of servicingMultiple editions of Windows 10 21H1 have reached their end of service (EOS) on this month's Patch Tuesday,...
K50343021: Node-vm2 vulnerability CVE-2022-36067
K50343021: Node-vm2 vulnerability CVE-2022-36067Node-vm2 vulnerability CVE-2022-36067 Security Advisory Security Advisory Description vm2 is a sandbox that can run untrusted code with whitelisted Nodes built-in modules. In...
California State Finance Department, Lockbit Ransomware’s Latest Victim
California State Finance Department, Lockbit Ransomware’s Latest VictimLockbit, the notorius Russian-linked ransomware group, claims to have added nine new victims to its growing list of conquests....
Uber Hit By New Data Breach After Attack on Third-Party Vendor
Uber Hit By New Data Breach After Attack on Third-Party VendorCompany information was stolen from third-party vendor Teqtivity and posted on a dark web forumLeer másCompany...
GoTrim Botnet Goes After WordPress Admin Accounts
GoTrim Botnet Goes After WordPress Admin AccountsGoTrim, a new Go-based botnet malware, scans the internet for WordPress websites and attempts to brute force the administrator’s password and...
Russian Medibank hackers could be first targets of Australian sanctions against cyber-attackers
Russian Medibank hackers could be first targets of Australian sanctions against cyber-attackersDfat confirms it has provided advice to minister Penny Wong about using cyber-related powers introduced...