As Long as We’re on the Subject of CAPTCHAsThere are these. Leer másSchneier on SecurityThere are these.
Friday Squid Blogging: Squid in Concert
Friday Squid Blogging: Squid in ConcertSquid is performing a concert in London in February. If you don’t know what their music is like, try this or...
USENIX Security ’22 – Yi Han, Matthew Chan, Zahra Aref, Nils Ole Tippenhauer, Saman Zonouz ‘Hiding In Plain Sight? On The Efficacy Of Power Side Channel-Based Control Flow Monitoring’
USENIX Security ’22 – Yi Han, Matthew Chan, Zahra Aref, Nils Ole Tippenhauer, Saman Zonouz ‘Hiding In Plain Sight? On The Efficacy Of Power Side Channel-Based...
Microsoft: Minecraft Servers Are Being Attacked by a Cross-Platform DDoS Botnet
Microsoft: Minecraft Servers Are Being Attacked by a Cross-Platform DDoS BotnetOn Thursday, Microsoft warned users about a cross-platform botnet that targets private Minecraft servers with distributed...
Emerging Cybersecurity Threats: Prepare Now for 2023
Emerging Cybersecurity Threats: Prepare Now for 2023As an eventful 2022 draws to a close, it’s worth analyzing and understanding the challenges organizations will be facing in...
Ex-Twitter employee Gets 3.5 Years Jail for Spying on Behalf of Saudi Arabia
Ex-Twitter employee Gets 3.5 Years Jail for Spying on Behalf of Saudi ArabiaA former Twitter employee who was found guilty of spying on behalf of Saudi...
Telegram App Scams & The Steps To Protect Against Them
Telegram App Scams & The Steps To Protect Against ThemProtect your company against Telegram scams. Achieve a seamless detection and takedown of fraudulent activity on Telegram...
Security Affairs newsletter Round 398 by Pierluigi Paganini
Security Affairs newsletter Round 398 by Pierluigi PaganiniA new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs free...
Cisco Event Response: September 2022 Semiannual Cisco IOS XR Software Security Advisory Bundled Publication
Cisco Event Response: September 2022 Semiannual Cisco IOS XR Software Security Advisory Bundled PublicationContenido de la entradaLeer másCisco Event Responses
Cisco Event Response: September 2022 Semiannual Cisco IOS and IOS XE Software Security Advisory Bundled Publication
Cisco Event Response: September 2022 Semiannual Cisco IOS and IOS XE Software Security Advisory Bundled PublicationContenido de la entradaLeer másCisco Event Responses
Cisco Event Response: November 2022 Semiannual Cisco ASA, FMC, and FTD Software Security Advisory Bundled Publication
Cisco Event Response: November 2022 Semiannual Cisco ASA, FMC, and FTD Software Security Advisory Bundled PublicationContenido de la entradaLeer másCisco Event Responses
USENIX Security ’22 – ‘Hertzbleed: Turning Power Side-Channel Attacks Into Remote Timing Attacks On x86’
USENIX Security ’22 – ‘Hertzbleed: Turning Power Side-Channel Attacks Into Remote Timing Attacks On x86’Complete Title: 'USENIX Security '22 - Yingchen Wang, Riccardo Paccagnella and Elizabeth...
Why do cyber-attacks increase during holidays?
Why do cyber-attacks increase during holidays?Why do cyber-attacks increase during holidays? Why do cyber-attacks increase during holidays? The holiday season is traditionally a golden opportunity for...
Trojanized Windows 10 Installer Used in Cyberattacks Against Ukrainian Government Entities
Trojanized Windows 10 Installer Used in Cyberattacks Against Ukrainian Government EntitiesGovernment entities in Ukraine have been breached as part of a new campaign that leveraged trojanized...
Facebook Security Failures Fueled Hate-Speech That Exacerbated Violence and Ethiopian Civil War
Facebook Security Failures Fueled Hate-Speech That Exacerbated Violence and Ethiopian Civil WarA recently filed lawsuit exposes the Facebook profit model, once again. Amare’s son, researcher Abrham...
BrandPost: One-Policy Framework, Zero Trust, and Ops teams
BrandPost: One-Policy Framework, Zero Trust, and Ops teamsIn today’s digital era, customers expect information, resources, and services to be readily available from anywhere in the world....
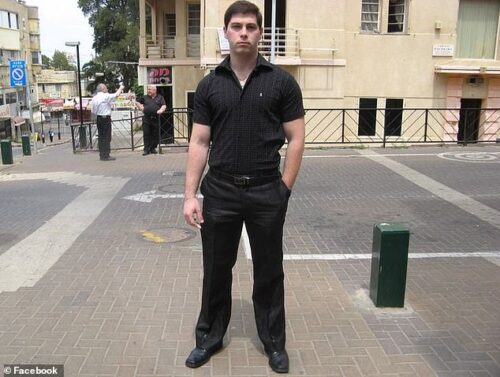
Ukrainian-born Israeli Living in America Arrested for Leaking Weapons Tech to Russia
Ukrainian-born Israeli Living in America Arrested for Leaking Weapons Tech to RussiaIt’s a less complicated story than it probably seems from the headlines. A 35-year-old Israeli...
5 Things Every Organization Should Consider When It Comes to Cybersecurity Awareness Training
5 Things Every Organization Should Consider When It Comes to Cybersecurity Awareness TrainingYour organization is assessing budgets, and security is high on the list. You’ve hired...
Are Technical Support Scams Getting More Advanced?
Are Technical Support Scams Getting More Advanced? Technical support scams (TSS) are responsible for a growing amount of financial losses year after year. Nevertheless, while the...
Samba Issues Security Updates to Patch Multiple High-Severity Vulnerabilities
Samba Issues Security Updates to Patch Multiple High-Severity VulnerabilitiesSamba has released software updates to remediate multiple vulnerabilities that, if successfully exploited, could allow an attacker to...
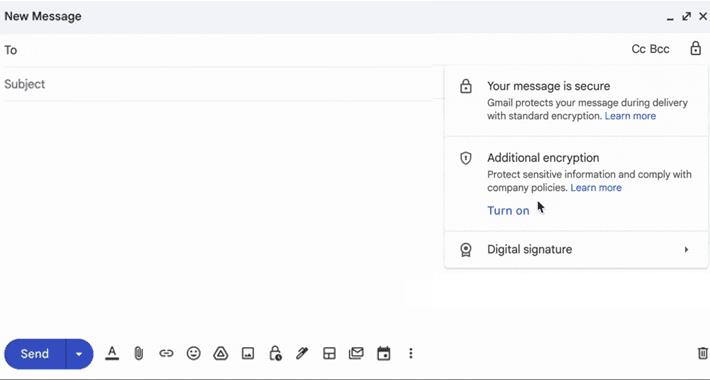
Google Takes Gmail Security to the Next Level with Client-Side Encryption
Google Takes Gmail Security to the Next Level with Client-Side EncryptionGoogle on Friday announced that its client-side encryption for Gmail is in beta for Workspace and...
Fortinet Warns of Active Exploitation of New SSL-VPN Pre-auth RCE Vulnerability
Fortinet Warns of Active Exploitation of New SSL-VPN Pre-auth RCE VulnerabilityFortinet on Monday issued emergency patches for a severe security flaw affecting its FortiOS SSL-VPN product...
Malware Strains Targeting Python and JavaScript Developers Through Official Repositories
Malware Strains Targeting Python and JavaScript Developers Through Official RepositoriesAn active malware campaign is targeting the Python Package Index (PyPI) and npm repositories for Python and...
Reported ECR Public Gallery Issue
Reported ECR Public Gallery IssueInitial Publication Date: 12/13/2022 9:00AM EST On November 14, 2022, a security researcher reported an issue in Amazon Elastic Container Registry (ECR)...
Proofpoint Nabs Illusive, Signaling a Sunset for Deception Tech
Proofpoint Nabs Illusive, Signaling a Sunset for Deception TechContenido de la entradaLeer másProofpoint News Feed
VMware Carbon Black Products and “User-Mode Hooking” Evasion Techniques
VMware Carbon Black Products and “User-Mode Hooking” Evasion TechniquesAttackers are always looking for a single fundamental technique they can use to fully defeat a given security...
December 2022 Patch Tuesday: Get Latest Security Updates from Microsoft and More
December 2022 Patch Tuesday: Get Latest Security Updates from Microsoft and MoreTech giant Microsoft released its last set of monthly security updates for 2022 with fixes for...
A tell-all conversation: The biggest cloud security trends, challenges & solutions
A tell-all conversation: The biggest cloud security trends, challenges & solutionsEXECUTIVE SUMMARY: In this dynamic tell-all conversation, excerpted from The TechArena podcast, VP of Cloud Security...
FuboTV says World Cup streaming outage caused by a cyberattack
FuboTV says World Cup streaming outage caused by a cyberattackFuboTV has confirmed that a streaming outage preventing subscribers from watching the World Cup Qatar 2022 semifinal...
Dozens of cybersecurity efforts included in this year’s US NDAA
Dozens of cybersecurity efforts included in this year’s US NDAALast week, members of the US House of Representatives and Senate reconciled their versions of the annual...