The security skills shortage is here, here’s how to prepareCorporate security is near the top of the list of CIO concerns for 2023 — but a...
Two-Thirds of Security Pros Have Burnt Out in Past Year
Two-Thirds of Security Pros Have Burnt Out in Past YearExcessive workload is the most common contributing factorLeer másExcessive workload is the most common contributing factor
LogRhythm Partners with SentinelOne to Accelerate Prevention, Detection and Response for Enterprise Environments
LogRhythm Partners with SentinelOne to Accelerate Prevention, Detection and Response for Enterprise EnvironmentsNew integration empowers security teams to identify behavioral anomalies, internal and external threats, and...
Social Blade Confirms Data Breach Exposing PII on the Dark Web
Social Blade Confirms Data Breach Exposing PII on the Dark WebThe company confirmed the data does not include any credit card informationLeer másThe company confirmed the...
The Smart Home Security Guide
The Smart Home Security Guide The smarts behind a smart home come from you. At least when it comes to keeping it more private and secure. ...
Why Privileged Access Management is a priority task
Why Privileged Access Management is a priority taskExploring how PAM can help mitigate and prevent threats to customer dataLeer másArticles RSS FeedExploring how PAM can help...
Hacked Ring Cams Used to Record Swatting Victims
Hacked Ring Cams Used to Record Swatting Victims Photo: BrandonKleinPhoto / Shutterstock.com Two U.S. men have been charged with hacking into the Ring home security cameras...
Meta’s Bug Bounty Program Shows $2m Awarded in 2022
Meta's Bug Bounty Program Shows $2m Awarded in 2022The total amount since the program's establishment in 2011 is reportedly $16mLeer másThe total amount since the program's...
The global state of DevSecOps
The global state of DevSecOpsHow DevOps teams are embracing new approaches of embedding application security testing into their development pipelines to truly achieve DevSecOps and application...
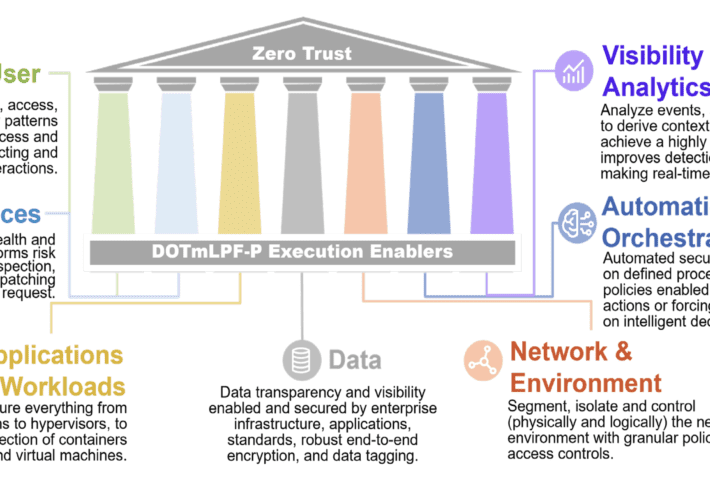
ForgeRock and the new DoD Zero Trust Strategy
ForgeRock and the new DoD Zero Trust StrategyOn November 7, 2023, the United States Department of Defense (DoD) released a new Zero Trust strategy, clarifying the...
How to Surrender to a Drone
How to Surrender to a DroneThe Ukrainian army has released an instructional video explaining how Russian soldiers should surrender to a drone: “Seeing the drone in...
Agenda Ransomware Switches to Rust to Attack Critical Infrastructure
Agenda Ransomware Switches to Rust to Attack Critical InfrastructureVictim companies have a combined revenue of around $550mLeer másVictim companies have a combined revenue of around $550m
Analysts Rate Tesla Mediocre Car Not Even Worth $20 Stock: “too unreliable for widespread use”
Analysts Rate Tesla Mediocre Car Not Even Worth $20 Stock: “too unreliable for widespread use”A car collector is angry the Tesla fraud happened to him. Soon...
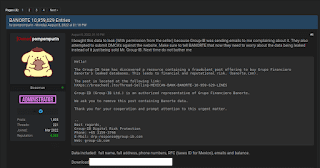
Exposing the “Data Leaks” Paradise – An Analysis
Exposing the "Data Leaks" Paradise – An Analysis In a world dominated by a countless number of malicious and fraudulent cyber threat actor adversaries including the...
Ostrich Cyber-Risk Welcomes Chip Whitmer as Vice President of Software Development
Ostrich Cyber-Risk Welcomes Chip Whitmer as Vice President of Software Development Ostrich Cyber-Risk Appoints Chip Whitmer as Vice President of Software Development. Former VP of Platform Architecture at...
API Vulnerabilities Discovered in LEGO Marketplace
API Vulnerabilities Discovered in LEGO MarketplaceThe vulnerabilities, which are now fixed, could have put sensitive customer data at riskLeer másThe vulnerabilities, which are now fixed, could...
Glupteba botnet is back after Google disrupted it in December 2021
Glupteba botnet is back after Google disrupted it in December 2021The Glupteba botnet is back, researchers reported a surge in infection worldwide after Google disrupted its...
NIST to Scrap SHA-1 Algorithm by 2030
NIST to Scrap SHA-1 Algorithm by 2030The agency said it will stop using SHA-1 in its last remaining specified protocols by December 31 2030Leer másThe agency...
FBI Charges 6, Seizes 48 Domains Linked to DDoS-for-Hire Service Platforms
FBI Charges 6, Seizes 48 Domains Linked to DDoS-for-Hire Service PlatformsThe U.S. Department of Justice (DoJ) on Wednesday announced the seizure of 48 domains that offered...
Three Steps Towards a More Secure OT Infrastructure
Three Steps Towards a More Secure OT InfrastructureBy Jason Weber, Vice President of Product, Veracity Industrial Networks Years ago, the biggest concern from the plant […]...
Threat Actors Target Ukraine’s DELTA Military System with Info-Stealing Malware
Threat Actors Target Ukraine’s DELTA Military System with Info-Stealing MalwareHackers used an email account belonging to the Ukrainian Ministry of Defense for launching a phishing campaign...
US Gov warns of BEC attacks to hijack shipments of food products
US Gov warns of BEC attacks to hijack shipments of food productsUS government is warning of business email compromise (BEC) attacks aimed at hijacking shipments of...
Mobile App Users at Risk as API Keys of Email Marketing Services Exposed
Mobile App Users at Risk as API Keys of Email Marketing Services ExposedLeaked API keys allow threat actors to perform a variety of unauthorized actionsLeer másLeaked...
Experts spotted a variant of the Agenda Ransomware written in Rust
Experts spotted a variant of the Agenda Ransomware written in RustResearchers spotted a new variant of the Agenda ransomware which is written in the cross-platform programming...
Meta Takes Down Over 200 Covert Influence Operations Since 2017
Meta Takes Down Over 200 Covert Influence Operations Since 2017The most common location for influence operations was Russia, according to MetaLeer másThe most common location for...
Ransomware Groups to Increase Zero-Day Exploit-Based Access Methods in the Future
Ransomware Groups to Increase Zero-Day Exploit-Based Access Methods in the FutureTrend Micro’s latest research paper analyzed ways in which ransomware groups could evolve to stay on...
Old vulnerabilities in Cisco products actively exploited in the wild
Old vulnerabilities in Cisco products actively exploited in the wildIT giant Cisco is warning of threat actors exploiting many old vulnerabilities in attacks in the wild....
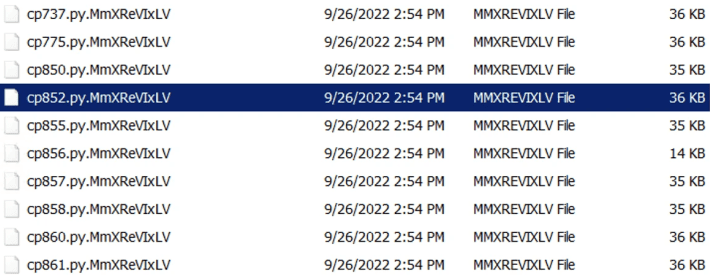
Hackers Bombard Open Source Repositories with Over 144,000 Malicious Packages
Hackers Bombard Open Source Repositories with Over 144,000 Malicious PackagesNuGet, PyPi, and npm ecosystems are the target of a new campaign that has resulted in over...
Ukraine’s Delta Military Intel System Hit by Attacks
Ukraine's Delta Military Intel System Hit by AttacksPhishing campaign spotted by CERT-UALeer másPhishing campaign spotted by CERT-UA
Top 5 Web App Vulnerabilities and How to Find Them
Top 5 Web App Vulnerabilities and How to Find ThemWeb applications, often in the form of Software as a Service (SaaS), are now the cornerstone for...