Godfather Trojan Targets 400 Financial Services FirmsMobile banking malware designed to steal bank and crypto credentialsLeer másMobile banking malware designed to steal bank and crypto credentials
UK Security Agency Wants Fresh Approach to Combat Phishing
UK Security Agency Wants Fresh Approach to Combat PhishingNCSC says "blame and fear" won’t workLeer másNCSC says "blame and fear" won’t work
Adult Google Ad Fraud Campaign Garnered Millions of Impressions
Adult Google Ad Fraud Campaign Garnered Millions of ImpressionsFraudster used "popunders" and obfuscation to generate cashLeer másFraudster used "popunders" and obfuscation to generate cash
Cyber-Incident Causes System Failures at Canadian Children’s Hospital
Cyber-Incident Causes System Failures at Canadian Children's HospitalThe ongoing incident has impacted clinical and corporate systems, as well as some hospital phone lines and webpagesLeer másThe...
US Most Impacted by Data Breaches in the Financial Industry in 2022
US Most Impacted by Data Breaches in the Financial Industry in 2022While 57% of these breaches were attributed to different types of malware, ATM skimming still...
Ransomware Attack Hits The Guardian Newspaper
Ransomware Attack Hits The Guardian NewspaperStaff told to work from home after compromiseLeer másStaff told to work from home after compromise
Researchers Develop AI-powered Malware Classification for 5G-enabled IIoT
Researchers Develop AI-powered Malware Classification for 5G-enabled IIoTA team of researchers came up with an ingenuous method leveraging AI to detect and classify malware in IIoT...
UK Government: Sharing Some Passwords is Illegal
UK Government: Sharing Some Passwords is IllegalIntellectual Property Office says it breaks copyright lawLeer másIntellectual Property Office says it breaks copyright law
BrandPost: The Next Big Attack Vector: Your Supply Chain
BrandPost: The Next Big Attack Vector: Your Supply ChainThere’s an old security adage: a chain is only as strong as its weakest link. The sentiment long...
FCC Proposes Massive $300m Fine for Robocall Firm
FCC Proposes Massive $300m Fine for Robocall FirmAuto-warranty campaign made billions of callsLeer másAuto-warranty campaign made billions of calls
An update on international data privacy protection
An update on international data privacy protection The 38 member countries of the Organization for Economic Cooperation and Development (OECD) have recently adopted a new international...
How to Use an HTTP Archive (HAR) With Mayhem
How to Use an HTTP Archive (HAR) With MayhemLearn how to fuzz an API without a specification by recording transactions with the API as an HTTP...
Report Surfaces Top Vulnerabilities of 2022
Report Surfaces Top Vulnerabilities of 2022 Rezilion, a vulnerability management platform provider, shared a list of the top vulnerabilities discovered in 2022. The report suggested that...
Best of 2022: The Role of AI in Cybersecurity
Best of 2022: The Role of AI in CybersecurityIt’s clear that AI can be a powerful tool in the fight against cybercrime. By automating many of...
Critical Microsoft Code-Execution Vulnerability
Critical Microsoft Code-Execution VulnerabilityA critical code-execution vulnerability in Microsoft Windows was patched in September. It seems that researchers just realized how serious it was (and is):...
Infostealer Malware Threat Grows as MFA Fatigue Attacks Spread
Infostealer Malware Threat Grows as MFA Fatigue Attacks Spread Information stealer malware flourished on underground criminal networks in 2022, along with a rise in multifactor authentication...
Microsoft dishes the dirt on Apple’s “Achilles heel” shortly after fixing similar Windows bug
Microsoft dishes the dirt on Apple’s “Achilles heel” shortly after fixing similar Windows bugIt happens to the best of us: Microsoft highlights a security bypass bug...
“Suspicious login” scammers up their game – take care at Christmas
“Suspicious login” scammers up their game – take care at ChristmasA picture is worth 1024 words - we clicked through so you don't have to.Leer másNaked...
Top 5 Tips for Choosing Endpoint Security
Top 5 Tips for Choosing Endpoint SecurityFollowing years now of digital transformation, cloud migration and deployment of hybrid workforces, enterprises have more endpoints than ever. Which...
Healthcare: Essential Defenses for Combating Ransomware
Healthcare: Essential Defenses for Combating RansomwareMove Infrastructure to the Cloud and Hone Incident Response Plans, Experts SayTo avoid having to even consider paying a ransom, experts...
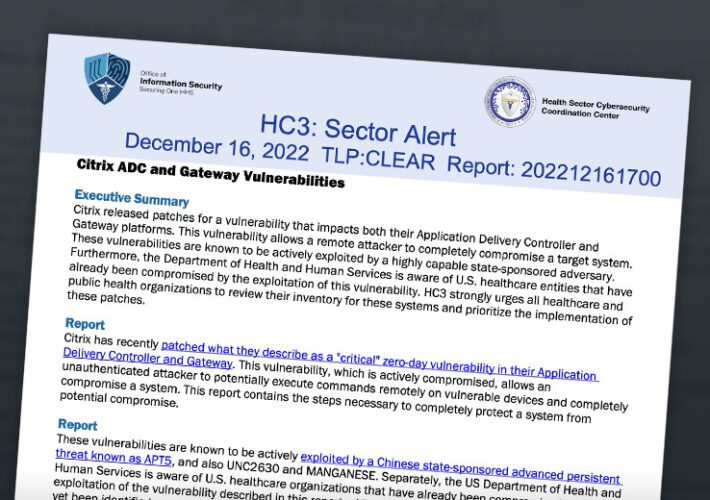
Chinese Hackers Exploit Citrix Vulnerabilities
Chinese Hackers Exploit Citrix VulnerabilitiesHealth Sector Entities Urged to Patch Citrix ADC, Gateway FlawsChinese hackers are exploiting known vulnerabilities in a Citrix networking appliance and virtual...
Microsoft Vulnerability Upgraded to Critical Due to RCE Risk
Microsoft Vulnerability Upgraded to Critical Due to RCE RiskCode-Execution Bug Has Broader Scope that Flaw Exploited by EternalBlue, IBM SaysMicrosoft upgraded a vulnerability first discovered in...
Nueva variante de Agenda Ransomware, escrita en Rust, dirigida a la infraestructura crítica
Nueva variante de Agenda Ransomware, escrita en Rust, dirigida a la infraestructura críticaSe ha observado una variante de Rust de una variedad de ransomware conocida como...
Samba emite actualizaciones de seguridad para parchar múltiples vulnerabilidades de alta gravedad
Samba emite actualizaciones de seguridad para parchar múltiples vulnerabilidades de alta gravedadSamba ha lanzado actualizaciones de software para remediar múltiples vulnerabilidades que, si se explotan con...
Phishing Targets Ukrainian Battlefield Awareness Tool Users
Phishing Targets Ukrainian Battlefield Awareness Tool UsersDigital Map Users Lured Into Installing Malware that Looked for Office FilesA phishing campaign against users of a Ukrainian battlefield...
Moving Containers: Uncovering Challenges. Finding Solutions.
Moving Containers: Uncovering Challenges. Finding Solutions. Get expert tips and best practices for securing containers in your business in our blog from Cloud Security experts, GuidePoint...
Iran-linked Charming Kitten espionage gang bares claws to pollies, power orgs
Iran-linked Charming Kitten espionage gang bares claws to pollies, power orgsContenido de la entradaLeer másProofpoint News Feed
Agenda Ransomware Uses Rust to Target More Vital Industries
Agenda Ransomware Uses Rust to Target More Vital IndustriesThis year, various ransomware-as-a-service groups have developed versions of their ransomware in Rust, including Agenda. Agenda's Rust variant...
How to Address the Skills Gap Crisis with DCIM Software
How to Address the Skills Gap Crisis with DCIM SoftwareData centers are essential components of the modern business landscape, providing the critical infrastructure that enables businesses...
Lacework Stiffens Cloud Security Posture Management
Lacework Stiffens Cloud Security Posture Management Lacework has added additional cloud security posture management (CSPM) capabilities to its platform to make it possible to create fine-grained...