EarSpy attack eavesdrops on Android phones via motion sensorsA team of researchers has developed an eavesdropping attack for Android devices that can, to various degrees, recognize...
Hackers steal $8 million from users running trojanized BitKeep apps
Hackers steal $8 million from users running trojanized BitKeep appsMultiple BitKeep crypto wallet users reported that their wallets were emptied during Christmas after hackers triggered transactions...
BTC.com lost $3 million worth of cryptocurrency in cyberattack
BTC.com lost $3 million worth of cryptocurrency in cyberattackBTC.com, one of the world's largest cryptocurrency mining pools, announced it was the victim of a cyberattack that...
Cisco Firepower Management Center Software XML External Entity Injection Vulnerability
Cisco Firepower Management Center Software XML External Entity Injection VulnerabilityA vulnerability in the module import function of the administrative interface of Cisco Firepower Management Center (FMC)...
5 essentials for boards to drive cyber readiness
5 essentials for boards to drive cyber readinessCheck Point Software’s cyber security evangelist Ashwin Ram shares 5 essentials for boards that will help drive cyber readiness....
Cisco Firepower Management Center Software Cross-Site Scripting Vulnerabilities
Cisco Firepower Management Center Software Cross-Site Scripting VulnerabilitiesMultiple vulnerabilities in the web-based management interface of Cisco Firepower Management Center (FMC) Software could allow an authenticated, remote...
Cisco Firepower Management Center Software Command Injection Vulnerabilities
Cisco Firepower Management Center Software Command Injection VulnerabilitiesMultiple vulnerabilities in the web management interface of Cisco Firepower Management Center (FMC) Software could allow an authenticated, remote...
Cisco Firepower Management Center Software Information Disclosure Vulnerability
Cisco Firepower Management Center Software Information Disclosure VulnerabilityA vulnerability in the web-based management interface of Cisco Firepower Management Center (FMC) Software could allow an unauthenticated, remote...
Cisco Adaptive Security Appliance Software and Firepower Threat Defense Software SNMP Denial of Service Vulnerability
Cisco Adaptive Security Appliance Software and Firepower Threat Defense Software SNMP Denial of Service VulnerabilityA vulnerability in the Simple Network Management Protocol (SNMP) feature of Cisco...
Cisco Adaptive Security Appliance Software and Firepower Threat Defense Software VPN Authorization Bypass Vulnerability
Cisco Adaptive Security Appliance Software and Firepower Threat Defense Software VPN Authorization Bypass VulnerabilityA vulnerability in the authentication and authorization flows for VPN connections in Cisco...
Cisco Firepower Threat Defense Software SIP and Snort 3 Detection Engine Denial of Service Vulnerability
Cisco Firepower Threat Defense Software SIP and Snort 3 Detection Engine Denial of Service VulnerabilityA vulnerability in the interaction of SIP and Snort 3 for Cisco...
Cisco Firepower Threat Defense Software SSL Decryption Policy Bleichenbacher Attack Vulnerability
Cisco Firepower Threat Defense Software SSL Decryption Policy Bleichenbacher Attack VulnerabilityA vulnerability in the TLS handler of Cisco Firepower Threat Defense (FTD) Software could allow an...
Cisco Firepower Threat Defense Software Privilege Escalation Vulnerability
Cisco Firepower Threat Defense Software Privilege Escalation VulnerabilityA vulnerability in the management web server of Cisco Firepower Threat Defense (FTD) Software could allow an authenticated, remote...
Why Healthcare Needs to Beef Up Incident Response Plans
Why Healthcare Needs to Beef Up Incident Response PlansEffective testing of incident response plans continues to be a major weakness for many healthcare sector entities, especially...
Cisco Firepower Threat Defense Software Generic Routing Encapsulation Denial of Service Vulnerability
Cisco Firepower Threat Defense Software Generic Routing Encapsulation Denial of Service VulnerabilityA vulnerability in the generic routing encapsulation (GRE) tunnel decapsulation feature of Cisco Firepower Threat...
Can I tell you a secret? Episode two: the widening circle
Can I tell you a secret? Episode two: the widening circleRevisited: As the cyberstalker spreads his net wider, anyone could be a target. The fast-changing world...
Can I tell you a secret? Episode three: the man upstairs – podcast
Can I tell you a secret? Episode three: the man upstairs – podcastRevisited: who is Matthew Hardy? Journalist Sirin Kale looks for clues about what motivates...
Cybersecurity firm links Piers Morgan Twitter hack to leak of 400m records
Cybersecurity firm links Piers Morgan Twitter hack to leak of 400m recordsFormer Australian prime minister Scott Morrison among politicians and celebrities whose details were in sample...
How to Reduce Clinician Friction in a Zero Trust Approach
How to Reduce Clinician Friction in a Zero Trust ApproachA carefully honed zero trust approach can allow healthcare entities to reduce pushback from clinicians while still...
Linux Critical Kernel-Level Bug Affects SMB Servers
Linux Critical Kernel-Level Bug Affects SMB ServersVulnerability With CVSS Score of 10 Affects KSMBD-Enabled ServersA critical Linux kernel vulnerability exposed the server message block protocol to...
Panel Discussion | The Risky Business of UnInspected Encrypted Traffic, User Privacy, and Compliance
Panel Discussion | The Risky Business of UnInspected Encrypted Traffic, User Privacy, and ComplianceContenido de la entradaLeer másDataBreachToday.com RSS Syndication
Hackers Steal Power Utility Customer Data
Hackers Steal Power Utility Customer DataSargent & Lundy Informs Over 6,900 That Hackers Stole Their Social Security NumbersConstruction and engineering firm Sargent & Lundy is informing...
Ohio Supreme Court Says Ransomware Is Not Physical Damage
Ohio Supreme Court Says Ransomware Is Not Physical DamageJustices Rule Against Software Developer in Bid to Use Insurance to Cover AttackAn Ohio software developer that attempted...
US Department of Justice Reportedly Investigates FTX Hack
US Department of Justice Reportedly Investigates FTX HackUnknown Actors Stole $372M From FTX Hours After It Filed For Bankruptcy in NovemberThe theft of nearly $400 million...
Cybercrime (and Security) Predictions for 2023
Cybercrime (and Security) Predictions for 2023Threat actors continue to adapt to the latest technologies, practices, and even data privacy laws—and it's up to organizations to stay...
Glupteba Botnet Continues to Thrive Despite Google’s Attempts to Disrupt It
Glupteba Botnet Continues to Thrive Despite Google's Attempts to Disrupt ItThe operators of the Glupteba botnet resurfaced in June 2022 as part of a renewed and...
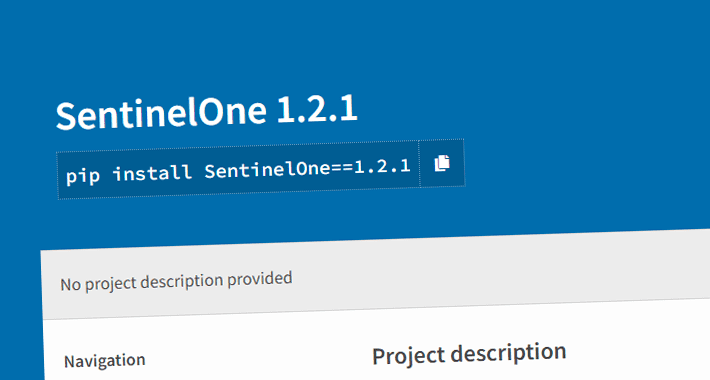
Researchers Discover Malicious PyPI Package Posing as SentinelOne SDK to Steal Data
Researchers Discover Malicious PyPI Package Posing as SentinelOne SDK to Steal DataCybersecurity researchers have discovered a new malicious package on the Python Package Index (PyPI) repository...
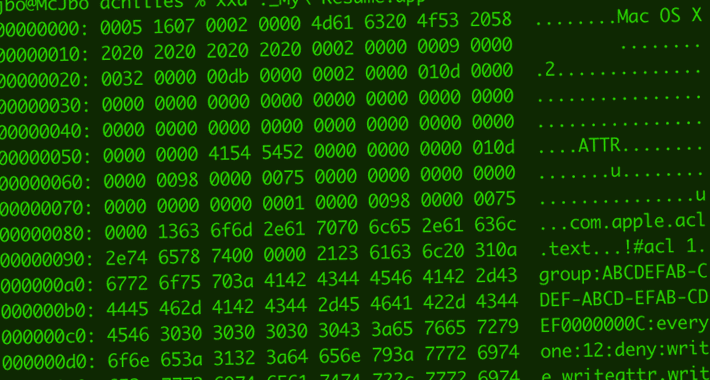
Microsoft Details Gatekeeper Bypass Vulnerability in Apple macOS Systems
Microsoft Details Gatekeeper Bypass Vulnerability in Apple macOS SystemsMicrosoft has disclosed details of a now-patched security flaw in Apple macOS that could be exploited by an...
W4SP Stealer Discovered in Multiple PyPI Packages Under Various Names
W4SP Stealer Discovered in Multiple PyPI Packages Under Various NamesThreat actors have published yet another round of malicious packages to Python Package Index (PyPI) with the...
Joyeux Noël et Bonne Année
Joyeux Noël et Bonne AnnéeThe post Joyeux Noël et Bonne Année appeared first on Security Boulevard. Leer másSecurity BoulevardThe post Joyeux Noël et Bonne Année appeared...