The Chasm Between Cybersecurity Confidence and Actual Ability A survey of 316 cybersecurity training strategy decision-makers in the UK, U.S, Canada, Germany and Sweden published today...
Author:
USENIX Security ’22 – Zenong Zhang, Zach Patterson, Michael Hicks, Shiyi Wei – ‘FIXREVERTER: A Realistic Bug Injection Methodology for Benchmarking Fuzz Testing’
USENIX Security ’22 – Zenong Zhang, Zach Patterson, Michael Hicks, Shiyi Wei – ‘FIXREVERTER: A Realistic Bug Injection Methodology for Benchmarking Fuzz Testing’Our thanks to USENIX...
How the Dark Web is Embracing ChatGPT and Generative AI
How the Dark Web is Embracing ChatGPT and Generative AIChatGPT and GPT-4 have been dazzling their users with their linguistic prowess. But, have you ever wondered...
Episode 8
Episode 8Cyborg Security is launching a podcast with a twist! Join us for the first fully interactive threat hunting podcast where you can hang out with...
LogRhythm Expands Partnership with Truvisor to Make Security Easy in Singapore
LogRhythm Expands Partnership with Truvisor to Make Security Easy in SingaporeSINGAPORE – March 29, 2023 — LogRhythm, the company empowering security teams to navigate the ever-changing...
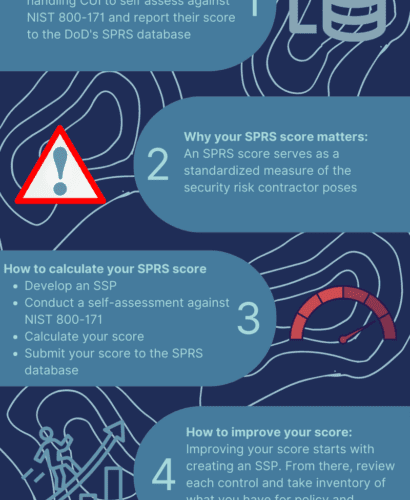
Five Things You Have to Know About Your SPRS Score
Five Things You Have to Know About Your SPRS ScoreIf you’re a defense contractor handling Controlled Unclassified Information (CUI) then you need to know your SPRS...
Hackers changed tactics, went cross-platform in 2022, says Trend Micro
Hackers changed tactics, went cross-platform in 2022, says Trend MicroPayouts from ransomware victims declined by 38% in 2022, prompting hackers to adopt more professional and corporate...
Microsoft announces generative AI Security Copilot
Microsoft announces generative AI Security CopilotMicrosoft today announced its AI Security Copilot, a GPT-4 implementation that brings generative AI capabilities to its in-house security suite, and...
Legacy, password-based authentication systems are failing enterprise security, says study
Legacy, password-based authentication systems are failing enterprise security, says studyAuthentication-related attacks grew in 2022, taking advantage of outdated, password-based authentication systems, according to a study commissioned...
Latitude Data breach is worse than initially estimated. 14 million individuals impacted
Latitude Data breach is worse than initially estimated. 14 million individuals impactedAustralian loan giant Latitude Financial Services (Latitude) revealed that a data breach its has suffered...
Bitter APT group targets China’s nuclear energy sector
Bitter APT group targets China’s nuclear energy sector Intezer researchers reported that a South Asian espionage group, tracked as Bitter, is targeting the Chinese nuclear energy industry....
Toyota Italy accidentally leaked sensitive data
Toyota Italy accidentally leaked sensitive dataToyota Italy accidentally leaked sensitive data for more than one-and-a-half years, until this March, CyberNews reported. A Japanese multinational accidentally leaked...
Eight Tips for CISOs Trying Get Their Board on Board
Eight Tips for CISOs Trying Get Their Board on BoardBy Ori Arbel, CTO, CYREBRO Nobody likes to be misunderstood, least of all C-level executives who play...
Next Generation Cybersecurity for Small to Midsize Businesses
Next Generation Cybersecurity for Small to Midsize BusinessesHow Cynet is giving lean security teams the tools they need to protect their business as budget crunches and...
Protecting Your Parents from Scams with Our New Family Plans
Protecting Your Parents from Scams with Our New Family Plans As people get into their 70s, they stand to lose more to fraud than any other...
ICS/OT Cybersecurity 2022 TXOne Annual Report Insights
ICS/OT Cybersecurity 2022 TXOne Annual Report InsightsThis article gives an in-depth overview of TXOne’s insight report on ICS/OT cyber incidents.Read MoreTrend Micro Research, News, PerspectivesThis article...
Improve your technical knowledge with 13 CompTIA courses for $54.97
Improve your technical knowledge with 13 CompTIA courses for $54.97This deal takes 98% off the total price of this course bundle until 4/3. The post Improve...
With political ‘hacktivism’ on the rise, Google launches Project Shield to fight DDoS attacks
With political ‘hacktivism’ on the rise, Google launches Project Shield to fight DDoS attacksIn 2022, DDoS exploits included high-profile attacks against websites offering information on elections...
Windows 11 KB5023778 update adds promotions to the Start menu
Windows 11 KB5023778 update adds promotions to the Start menuMicrosoft has released the optional March 2023 non-security preview update for Windows 11 that comes with a...
WiFi protocol flaw allows attackers to hijack network traffic
WiFi protocol flaw allows attackers to hijack network trafficCybersecurity researchers have discovered a fundamental security flaw in the design of the IEEE 802.11 WiFi protocol standard,...
Windows 11 KB5023774 update causes Red Dead Redemption 2 launch issues
Windows 11 KB5023774 update causes Red Dead Redemption 2 launch issuesMicrosoft is investigating a known issue triggered by the KB5023774 March 2023 preview update and causing...
Trojanized Tor browsers target Russians with crypto-stealing malware
Trojanized Tor browsers target Russians with crypto-stealing malwareA surge of trojanized Tor Browser installers targets Russians and Eastern Europeans with clipboard-hijacking malware that steals infected users'...
ChatGPT-4 and cyber crime, insights from a Nasdaq TradeTalk
ChatGPT-4 and cyber crime, insights from a Nasdaq TradeTalkIn this edited excerpt from a recent Nasdaq TradeTalk, Check Point’s Head of Engineering, U.S East, Mark Ostrowski,...
How AI is changing the job market: Who’s most and least at-risk
How AI is changing the job market: Who’s most and least at-riskEXECUTIVE SUMMARY: Artificial intelligence is rapidly altering how we live and how we work. Its...
TechScape: How the world is turning against social media
TechScape: How the world is turning against social mediaFrance has banned not only TikTok from government phones, but Facebook and Twitter, too. Could this be a...
Framing Frames: Bypassing Wi-Fi Encryption by Manipulating Transmit Queues Affecting Multiple Cisco Products
Framing Frames: Bypassing Wi-Fi Encryption by Manipulating Transmit Queues Affecting Multiple Cisco ProductsOn March 27, 2023, the research paper Framing Frames: Bypassing Wi-Fi Encryption by Manipulating...
Framing Frames: Bypassing Wi-Fi Encryption by Manipulating Transmit Queues Affecting Multiple Cisco Products
Framing Frames: Bypassing Wi-Fi Encryption by Manipulating Transmit Queues Affecting Multiple Cisco ProductsOn March 27, 2023, the research paper Framing Frames: Bypassing Wi-Fi Encryption by Manipulating...
Cisco SD-WAN vManage Software Cluster Mode Cross-Site Request Forgery Vulnerability
Cisco SD-WAN vManage Software Cluster Mode Cross-Site Request Forgery VulnerabilityA vulnerability in the web-based management interface of Cisco SD-WAN vManage Software when it is operating in...
Panel Discussion | FTC Safeguards Rule: Get Compliant and Get on with Business
Panel Discussion | FTC Safeguards Rule: Get Compliant and Get on with BusinessPost ContentRead MoreDataBreachToday.com RSS Syndication
Live Webinar | Creating Trust in an Insecure World: Strategies for CISOs in the Age of Increasing Vulnerabilities
Live Webinar | Creating Trust in an Insecure World: Strategies for CISOs in the Age of Increasing VulnerabilitiesPost ContentRead MoreDataBreachToday.com RSS Syndication