Ransomware Hits US Marshals ServiceAgency Confirms Sensitive Law Enforcement Information CompromisedHackers maliciously encrypted a system belonging to the U.S. Marshals Service, compromising and exfiltrating sensitive data...
Author:
Attackers Hacked into LastPass Via Employee’s Home Computer
Attackers Hacked into LastPass Via Employee's Home ComputerAttackers Exploited Vulnerability in Third-Party Software for AccessThe situation at LastPass keeps getting worse: the company says hackers implanted...
Roban código fuente del proveedor y registrador de dominios GoDaddy
Roban código fuente del proveedor y registrador de dominios GoDaddyGoDaddy, una de las principales compañías de alojamiento web, ha informado de una brecha de seguridad en...
SlashNext Employs Generative AI to Combat Cybersecurity Threats
SlashNext Employs Generative AI to Combat Cybersecurity Threats SlashNext today launched a platform that makes use of generative artificial intelligence (AI) to thwart business email compromise...
CrowdStrike Report Maps Changes to Cybersecurity Landscape
CrowdStrike Report Maps Changes to Cybersecurity Landscape A report published by CrowdStrike today highlighted how the cybersecurity threat landscape has shifted in the last year, with...
Orca Security Adds Data Security Capabilities to Cloud Platform
Orca Security Adds Data Security Capabilities to Cloud Platform Orca Security today added a data security posture management (DSPM) capability to its cloud security platform as...
CSMA: What is Cybersecurity Mesh Architecture?
CSMA: What is Cybersecurity Mesh Architecture?Learn about the key components & benefits of Cybersecurity Mesh Architecture (CSMA). Enhance security and stay ahead of the game with...
System Hardening Best Practices
System Hardening Best Practices In a recent podcast interview with Hillarie McClure, Multimedia Director of Cybercrime Magazine, Robert E. Johnson III, Cimcor CEO/President, discusses system hardening...
Despite Cybersecurity Investments, Breaches Increasing
Despite Cybersecurity Investments, Breaches Increasing A survey of 300 CIOs, CISOs and security executives from enterprises in Europe and the U.S. that have more than 1,000...
Hackers Claim They Breached T-Mobile More Than 100 Times in 2022
Hackers Claim They Breached T-Mobile More Than 100 Times in 2022Three different cybercriminal groups claimed access to internal networks at communications giant T-Mobile in more than...
How one trillion events power the Sift global data network
How one trillion events power the Sift global data networkThe Sift global data network now processes more than one trillion events per year, providing customers with...
If it’s AI, it’s probably written in PowerPoint…
If it’s AI, it’s probably written in PowerPoint…At MixMode, we will look you in the eye when we explain that we know the marketplace is crowded...
An API Security Testing Checklist… with a twist
An API Security Testing Checklist… with a twistLearn how to look more offensively at API security testing and apply the concept of common attack pattern enumeration...
Evolving cyberattacks, alert fatigue creating DFIR burnout, regulatory risk
Evolving cyberattacks, alert fatigue creating DFIR burnout, regulatory riskThe evolution of cybercrime is weighing heavily on digital forensics and incident response (DFIR) teams, leading to significant...
London Honeypots Attacked 2000 Times Per Minute
London Honeypots Attacked 2000 Times Per MinuteInsurer records 91 million attacks in total in JanuaryRead MoreInsurer records 91 million attacks in total in January
Experts Spot Half a Million Novel Malware Variants in 2022
Experts Spot Half a Million Novel Malware Variants in 2022Overall malware detections also rise after three years of declineRead MoreOverall malware detections also rise after three...
Ransomware Attack Hits US Marshals Service
Ransomware Attack Hits US Marshals ServiceDrew Wade, chief of the Marshals Service public affairs office, made the announcement on MondayRead MoreDrew Wade, chief of the Marshals...
Phone Attacks and MFA Bypass Drive Phishing in 2022
Phone Attacks and MFA Bypass Drive Phishing in 2022Proofpoint reveals surge in direct financial losses from attacksRead MoreProofpoint reveals surge in direct financial losses from attacks
LastPass Data Stolen in August 2022 Breach Used For December Attack
LastPass Data Stolen in August 2022 Breach Used For December AttackThreat actors obtained credentials and keys later used to access and decrypt some storage volumesRead MoreThreat...
US Gov. Agencies Have 30 Days to Remove TikTok, Canada Follows Suit
US Gov. Agencies Have 30 Days to Remove TikTok, Canada Follows SuitWithin 90 days, agencies must also cancel existing contracts that necessitate the app's useRead MoreWithin...
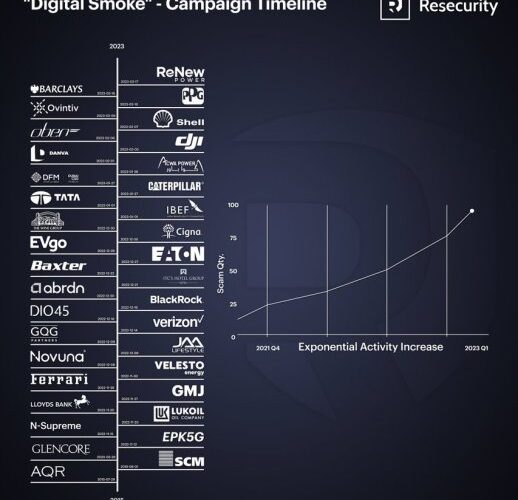
Resecurity identified the investment scam network ‘Digital Smoke’
Resecurity identified the investment scam network ‘Digital Smoke’Resecurity identified one of the largest investment fraud networks, tracked as Digital Smoke, by size and volume of operations....
CISA adds ZK Java Web Framework bug to Known Exploited Vulnerabilities Catalog
CISA adds ZK Java Web Framework bug to Known Exploited Vulnerabilities CatalogUS CISA added an actively exploited vulnerability in the ZK Java Web Framework to its...
U.S. Marshals Service suffers a ransomware attack
U.S. Marshals Service suffers a ransomware attackThe U.S. Marshals Service (USMS) was the victim of a ransomware attack, it is investigating the theft of sensitive information....
Exfiltrator-22, a New Post-exploitation Kit for Sale
Exfiltrator-22, a New Post-exploitation Kit for SaleExfiltrator-22 is a new post-exploitation kit that can spread ransomware undetected. Researchers speculate that the creators of this kit are...
What Is a Port Scan Attack? Definition and Prevention Measures for Enterprises
What Is a Port Scan Attack? Definition and Prevention Measures for EnterprisesA port scan attack is a technique that enables threat actors to find server vulnerabilities....
Major Ransomware Attack on U.S. Marshals Service Compromises Sensitive Information
Major Ransomware Attack on U.S. Marshals Service Compromises Sensitive InformationAccording to multiple senior U.S. law enforcement officials, the U.S. Marshals Service suffered a security breach more...
15M Allegedly Peruvian Tax Authority Records Leaked on Forum
15M Allegedly Peruvian Tax Authority Records Leaked on ForumPeruvian citizens are at risk of identity theft and financial fraud following the exposure of a database allegedly...
Busting Myths Around Cybersecurity Team Training
Busting Myths Around Cybersecurity Team TrainingNew Research Results from Omdia and Cybrary Point to Substantial ROI From Continuous Upskilling of Cybersecurity Teams. By Kevin Hanes, CEO,...
CredPump, HoaxPen, and HoaxApe Backdoor Detection: UAC-0056 Hackers Launch Disruptive Attacks Against Ukrainian Government Websites Planned Over One Year Earlier
CredPump, HoaxPen, and HoaxApe Backdoor Detection: UAC-0056 Hackers Launch Disruptive Attacks Against Ukrainian Government Websites Planned Over One Year Earlier Approaching the date of one-year anniversary...
Side-Channel Attack against CRYSTALS-Kyber
Side-Channel Attack against CRYSTALS-KyberCRYSTALS-Kyber is one of the public-key algorithms currently recommended by NIST as part of its post-quantum cryptography standardization process. Researchers have just published...