Source: securityboulevard.com – Author: Jeffrey Burt A sprawling phishing-as-a-service (PhaaS) campaign that has been running since at least last summer is using more than 20,000 fake...
Author: CISO2CISO Editor 2
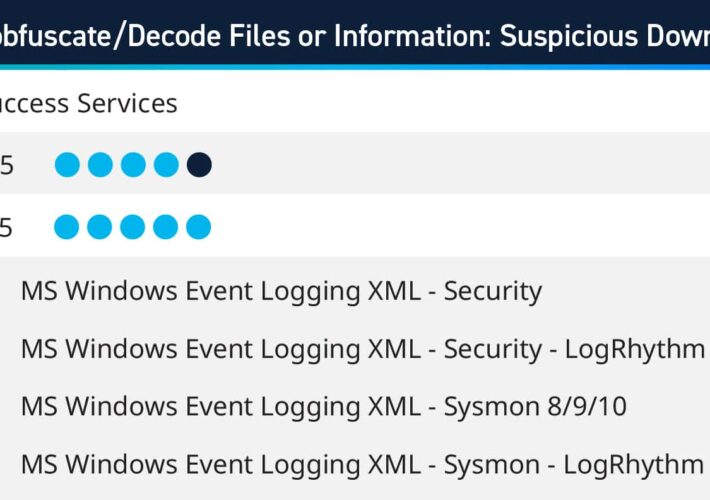
Q1 2024 Success Services Use Cases – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kelsey Gast As part of the Subscription Services team, LogRhythm consultants work with customers to help bolster their defenses against cyberthreats and...
Strengthening Security in Distributed Payment Systems: Exploring Innovative Solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nak Koh Building on our previous discussion about the pivotal role of Trusted Platform Modules (TPMs) in securing distributed ID and payment...
Market Forces vs. Regulation: How to Drive IT Product Safety – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland Over the past 50 years, traveling in automobiles has become much safer. Part of this is due to government regulations...
Implications of AI for Corporate Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ontic Contributor Article By: Ontic Contributor | March 29, 2024 On February 29, I was honored to serve as the moderator for...
Guarding Education: The Impact of Compromised Credentials – Source: securityboulevard.com
Source: securityboulevard.com – Author: Enzoic In recent years, the education sector has increasingly become a target for cybercriminals seeking to exploit vulnerabilities and gain unauthorized access...
PyPI Goes Quiet After Huge Malware Attack: 500+ Typosquat Fakes Found – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings The Python Package Index was drowning in malicious code again, so they had to shut down registration for cleanup. More software supply-chain...
A(nother) Ransomware Saga with a Twist – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joao Correia The healthcare sector has once again found itself at the center of a storm. On February 21, Change Healthcare, a...
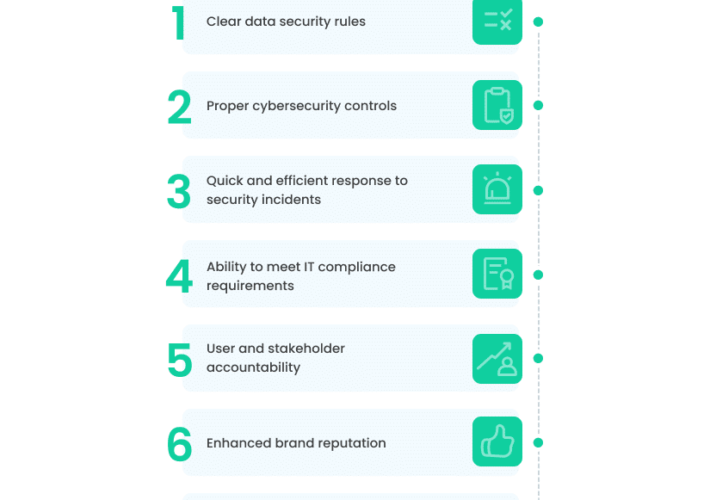
10 Must-Have Elements for an Air-Tight IT Security Policy – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rom Carmel In 2023, data security faced an uphill battle against cyberattacks, and the risks of becoming a victim grew stronger. There...
DHS Calls Political Campaigns ‘Ripe Target’ for Cyberattacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government Foreign Adversaries Increasingly See Campaigns as Prime for Hacking, Official...
Is It Generative AI’s Fault, or Do We Blame Human Beings? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 AI is on the way to embedding itself in our daily lives. If you feel threatened by artificial intelligence, Sam Curry...
ShadowRay Attack Strikes AI Workloads – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Thousands of AI Workloads Compromised Amid CVE Vulnerability Dispute Prajeet...
Feds Warn of Credential Harvesting Threats in Healthcare – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Anti-Phishing, DMARC , Fraud Management & Cybercrime , Social Engineering HHS Says Tried-and-True Hacker Methods Can Compromise Patient Data, Safety Marianne...
Malware Flood Causes PyPI to Temporarily Halt New Accounts – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Security Operations Hackers Are Now Using Code Repositories as Malware Vectors Mihir Bagwe (MihirBagwe) • March 29, 2024 Python...
On Point: The New Impersonation-Social Engineering Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development How AI and Deepfakes Make...
Manufacturing on the Cyber Frontlines: Enhancing Cybersecurity on the Factory Floor – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Berardino Baratta, CEO, MxD Manufacturing in the United States is changing. Today’s factory floors are a far cry from...
Making Our Infrastructure Resilient: 5 Priorities for Security R&D – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Saurabh Amin, Professor of Civil and Environmental Engineering PI, Laboratory for Information and Decision Systems Massachusetts Institute of Technology...
Key Differences in Securing OT & IT Environments – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Critical cybersecurity components every security leader must know amid the convergence of IT & OT By Joe O’Donnell, EVP of...
Institutionalizing Awareness to Stop Cyberattacks – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Aimei Wei, Founder and CTO, Stellar Cyber Large and mid-sized organizations are always hoping for a ‘silver bullet’ technology...
Friday Squid Blogging: The Geopolitics of Eating Squid – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier New York Times op-ed on the Chinese dominance of the squid industry: China’s domination in seafood has raised deep concerns...
Lessons from a Ransomware Attack against the British Library – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Carl Engelbrecht • March 29, 2024 7:53 AM Why do technologists who know better continue to propagate the...
AI and Trust – Source: www.schneier.com
Source: www.schneier.com – Author: B. Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
An educational robot security research – Source: securelist.com
Source: securelist.com – Author: Nikolay Frolov In the modern world, we are surrounded by a multitude of smart devices that simplify our daily lives: smart speakers,...
Power grab: the hidden costs of Ireland’s datacentre boom – podcast – Source: www.theguardian.com
Source: www.theguardian.com – Author: Written by Jessica Traynor and read by Simone Kirby. Produced by Nicola Alexandrou. The executive producer was Ellie Bury Datacentres are part...
A shadowy hacker group brought the British Library to its knees. Is there any way to stop them? | Lamorna Ash – Source: www.theguardian.com
Source: www.theguardian.com – Author: Lamorna Ash It is not quite accurate to say that the cyber-attack against the British Library took place on 28 October 2023....
Dozens in Jordan targeted by authorities using NSO spyware, report finds – Source: www.theguardian.com
Source: www.theguardian.com – Author: Stephanie Kirchgaessner in Washington About three dozen journalists, lawyers and human rights workers in Jordan have been targeted by authorities using powerful...
Football Australia data leak exposes players’ contracts, fans’ personal details – Source: www.theguardian.com
Source: www.theguardian.com – Author: Jack Snape Passports, player contracts and more have been available online for almost two years due to a Football Australia (FA) data...
Digital afterlife – how to deal with social media accounts when someone dies – Source: www.theguardian.com
Source: www.theguardian.com – Author: Josh Taylor Gavin Blomeley was lucky his mother was incredibly organised before she died. She left a note that included the passcode...
Slash your overdraft costs and get ‘free’ cash: how to get your bank and savings into shape – Source: www.theguardian.com
Source: www.theguardian.com – Author: Miles Brignall Samuel Gibbs, Sandra Haurant, Rupert Jones, Sarah Marsh and Hilary Osborne Don’t get stung on overdraft costs Authorised overdraft costs...
‘Unsettling’: hackers break into Victorian court recordings database – Source: www.theguardian.com
Source: www.theguardian.com – Author: Australian Associated Press Victoria’s court system has been hit by a cyber-attack, with hackers accessing several weeks of recorded hearings. Court Services...