Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer, Dark Reading The first draft standards for quantum-resistant public key cryptography based on algorithms chosen by the National...
Author: admin
Cybersecurity Insights with Contrast CISO David Lindner | 8/25 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Yes, we have specific objectives for uptime and recovery Yes, we talk about resilience, but don’t have...
Two LAPSUS$ Hackers Convicted in London Court for High-Profile Tech Firm Hacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 25, 2023THNCyber Crime / Data Breach Two U.K. teenagers have been convicted by a jury in London for being part...
Learn How Your Business Data Can Amplify Your AI/ML Threat Detection Capabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 25, 2023The Hacker NewsThreat Detection / Artificial Intelligence In today’s digital landscape, your business data is more than just numbers—it’s...
Navigating Legacy Infrastructure: A CISO’s Actionable Strategy for Success – Source:thehackernews.com
Source: thehackernews.com – Author: . Every company has some level of tech debt. Unless you’re a brand new start-up, you most likely have a patchwork of...
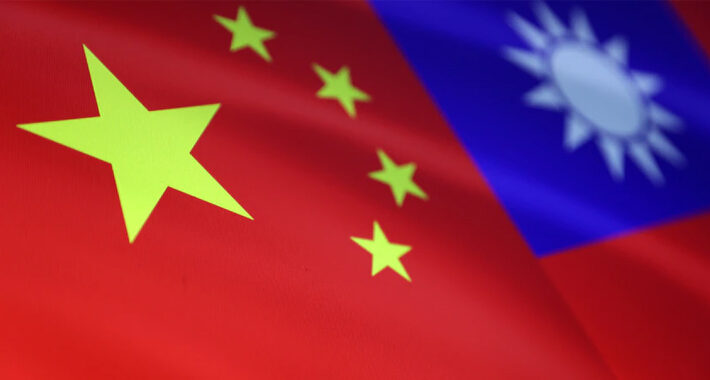
China-Linked Flax Typhoon Cyber Espionage Targets Taiwan’s Key Sectors – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 25, 2023THNCyber Espionage A nation-state activity group originating from China has been linked to cyber attacks on dozens of organizations...
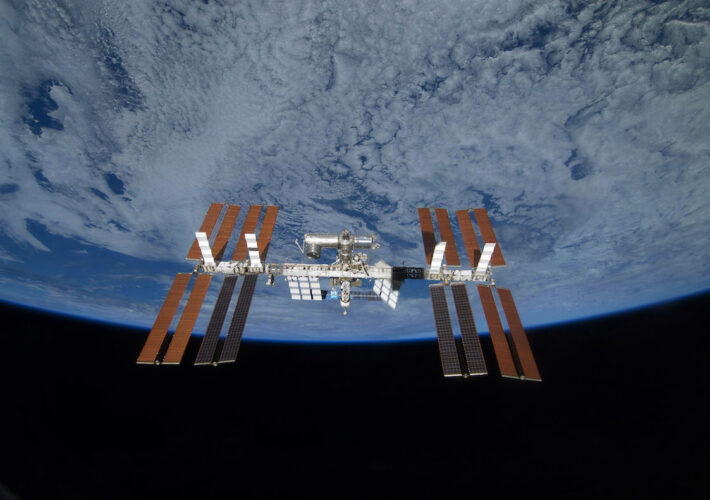
US Space Industry More Prone to Foreign Espionage, US Agencies Warn – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In coordination with the FBI, the National Counterintelligence and Security Center (NCSC), and the Air Force Office...
Urgent FBI Warning: Barracuda Email Gateways Vulnerable Despite Recent Patches – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 25, 2023THNEmail Security / Vulnerability The U.S. Federal Bureau of Investigation (FBI) is warning that Barracuda Networks Email Security Gateway...
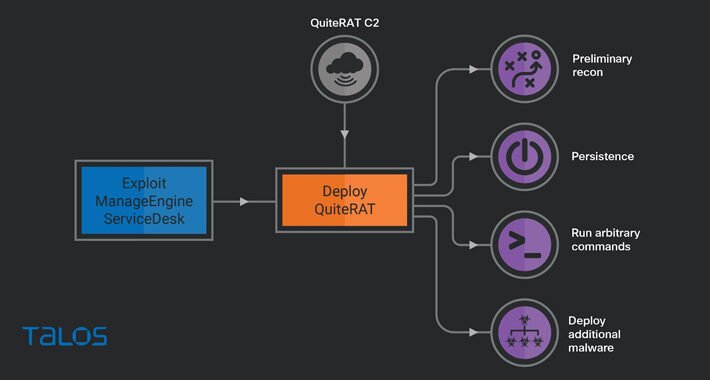
Lazarus Group Exploits Critical Zoho ManageEngine Flaw to Deploy Stealthy QuiteRAT Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 24, 2023THNCyber Attack / Hacking The North Korea-linked threat actor known as Lazarus Group has been observed exploiting a now-patched...
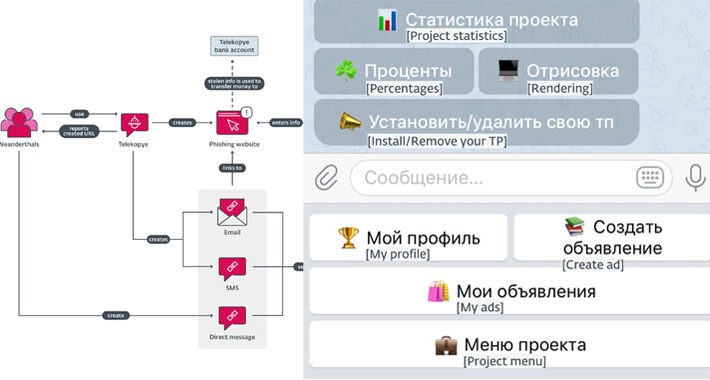
New Telegram Bot “Telekopye” Powering Large-scale Phishing Scams from Russia – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 24, 2023THNCyber Threat / Phishing A new financially motivated operation is leveraging a malicious Telegram bot to help threat actors...
The Hidden Dangers of Public Wi-Fi – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 24, 2023The Hacker NewsNetwork Security / DNS Public Wi-Fi, which has long since become the norm, poses threats to not...
New “Whiffy Recon” Malware Triangulates Infected Device Location via Wi-Fi Every Minute – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 24, 2023THNMalware / Privacy The SmokeLoader malware is being used to deliver a new Wi-Fi scanning malware strain called Whiffy...
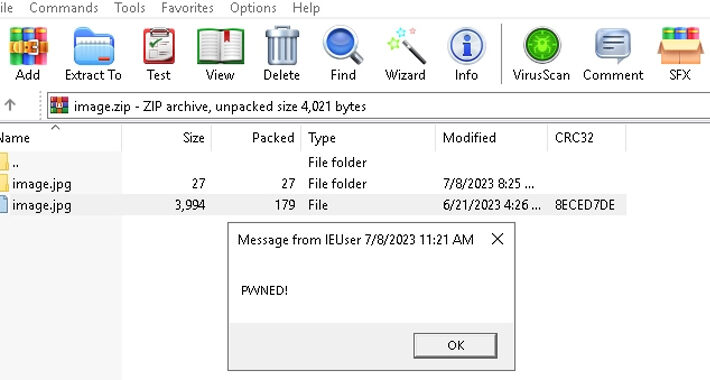
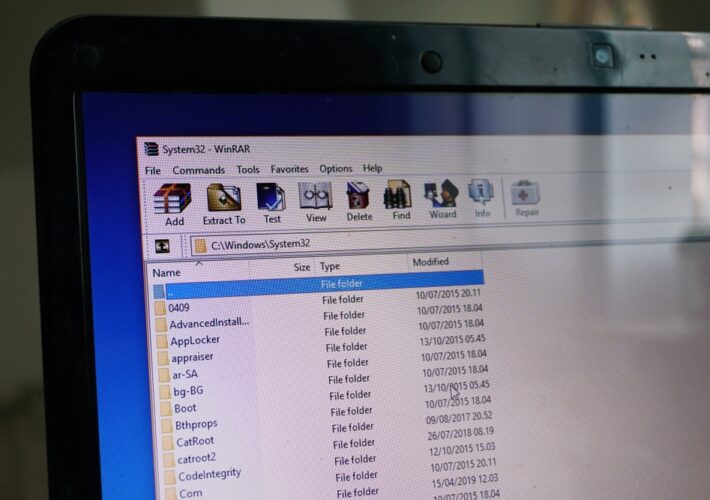
WinRAR Security Flaw Exploited in Zero-Day Attacks to Target Traders – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 24, 2023THNEndpoint Security / Zero-Day A recently patched security flaw in the popular WinRAR archiving software has been exploited as...
Ransomware With an Identity Crisis Targets Small Businesses, Individuals – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Researchers have identified a new strain of ransomware that dates back to 2019 and targets individuals and...
eBay Users Beware Russian ‘Telekopye’ Telegram Phishing Bot – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Russian-language Telegram users are using a bot to automate end-to-end phishing campaigns against users of popular ecommerce...
North Korea’s Lazarus APT Uses GUI Framework to Build Stealthy RAT – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading In recent attacks against healthcare organizations and an Internet infrastructure company, North Korea’s famous Lazarus Group...
eSentire Labs Open Sources Project to Monitor LLMs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading eSentire Labs announced the eSentire LLM Gateway, an open source implementation framework that provides security teams with...
Prelude Security Tackles Continuous Security Testing in Containers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Prelude Security has enhanced its Probes technology to help security teams run continuous security tests on all...
Thousands of Unpatched Openfire XMPP Servers Still Exposed to High-Severity Flaw – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 24, 2023THNCyber Attack / Vulnerability Thousands of Openfire XMPP servers are unpatched against a recently disclosed high-severity flaw and are...
Tornado Cash Founders Charged in Billion-Dollar Crypto Laundering Scandal – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 24, 2023THNCyber Crime / Cryptocurrency The U.S. Justice Department (DoJ) on Wednesday unsealed an indictment against two founders of the...
Ransomware Reaches New Heights – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Ransomware is on track to victimize more organizations in 2023, while attackers rapidly escalate their attacks...
Threat Actor Exploits Zero-Day in WinRAR to Target Crypto Accounts – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A threat actor with possible connections to Russia’s financially motivated Evilnum group is targeting users in...
FBI Warns of Cryptocurrency Heists by North Korea’s Lazarus Group – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The FBI has tracked hundreds of millions of dollars in cryptocurrency stolen by the Democratic People’s Republic...
Name That Toon: Swift as an Arrow – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Sharpen your arrows, Dark Reading friends. It’s time to come up with a clever cybersecurity-related caption for the cartoon,...
Attackers Dangle AI-Based Facebook Ad Lures to Hijack Business Accounts – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A threat actor has been abusing paid Facebook ads to lure victims with the promise of AI...
5 Early Warning Indicators That Are Key to Protecting National Secrets – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kellie Roessler, Insider Risk Advocate & Author, DTEX Insider Intelligence & Investigations (i3) Team The US Department of Defense (DoD) will create...
‘Cuba’ Ransomware Group Uses Every Trick in the Book – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading In June, Russian ransomware group Cuba attacked an organization servicing US critical infrastructure. The cyberattack failed...
New NCUA Rule Requires Credit Unions to Report Cyberattacks Within 3 Days – Source: www.darkreading.com
Source: www.darkreading.com – Author: Edge Editors, Dark Reading All federally insured credit unions must report cyber incidents within 72 hours of discovery, according to the National...
North Korean Affiliates Suspected in $40M Cryptocurrency Heist, FBI Warns – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023THNCryptocurrency / Cyber Attack The U.S. Federal Bureau of Investigation (FBI) on Tuesday warned that threat actors affiliated with...
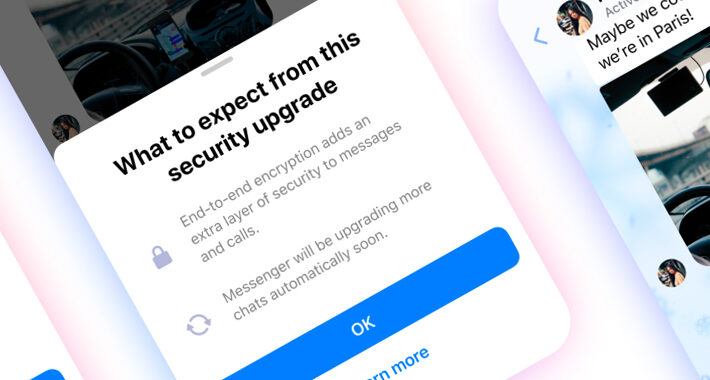
Meta Set to Enable Default End-to-End Encryption on Messenger by Year End – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 23, 2023THNEncryption / Privacy Meta has once again reaffirmed its plans to roll out support for end-to-end encryption (E2EE) by...