Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A recent supply chain breach at Kroll, the risk and financial advisory firm, affected downstream customers and...
Author: admin
Critical Vulnerability Alert: VMware Aria Operations Networks at Risk from Remote Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 30, 2023THNVulnerability / Network Security VMware has released software updates to correct two security vulnerabilities in Aria Operations for Networks...
FBI Dismantles QakBot Malware, Frees 700,000 Computers, Seizes $8.6 Million – Source:thehackernews.com
Source: thehackernews.com – Author: . A coordinated law enforcement effort codenamed Operation Duck Hunt has felled QakBot, a notorious Windows malware family that’s estimated to have...
Unpatched Citrix NetScaler Devices Targeted by Ransomware Group FIN8 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Citrix NetScaler ADC and NetScaler Gateway are at heightened risk of opportunistic attacks by a ransomware...
Sprawling Qakbot Malware Takedown Spans 700,000 Infected Machines – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The infrastructure behind the infamous Qakbot malware, a favorite tool of cybercriminals far and wide,...
MOVEit Was a SQL Injection Accident Waiting to Happen – Source: www.darkreading.com
Source: www.darkreading.com – Author: Omkhar Arasaratnam, General Manager, Open Source Security Foundation (OpenSSF) In late 1998, when I was just beginning my career in technology, I...
Meta Cripples China’s Signature ‘Spamouflage’ Influence Op – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Meta has taken down thousands of accounts and pages tied to a Chinese state-backed disinformation group...
South African Department of Defence Denies Stolen Data Claims – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading A 1.6TB file containing personnel details of the South African Department of Defence has been found...
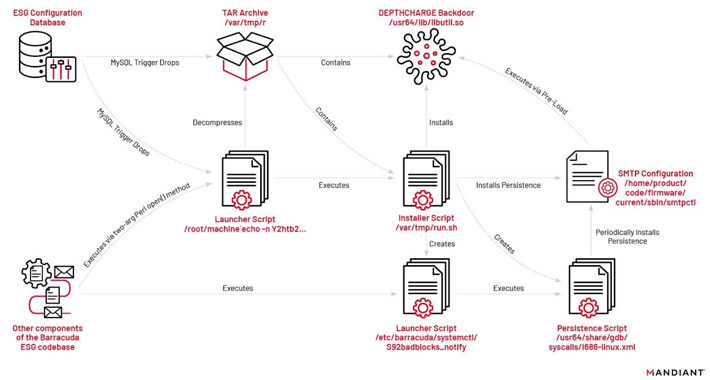
Chinese Hacking Group Exploits Barracuda Zero-Day to Target Government, Military, and Telecom – Source:thehackernews.com
Source: thehackernews.com – Author: . A suspected Chinese-nexus hacking group exploited a recently disclosed zero-day flaw in Barracuda Networks Email Security Gateway (ESG) appliances to breach...
DarkGate Malware Activity Spikes as Developer Rents Out Malware to Affiliates – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 29, 2023The Hacker NewsMalware / Cyber Threat A new malspam campaign has been observed deploying an off-the-shelf malware called DarkGate....
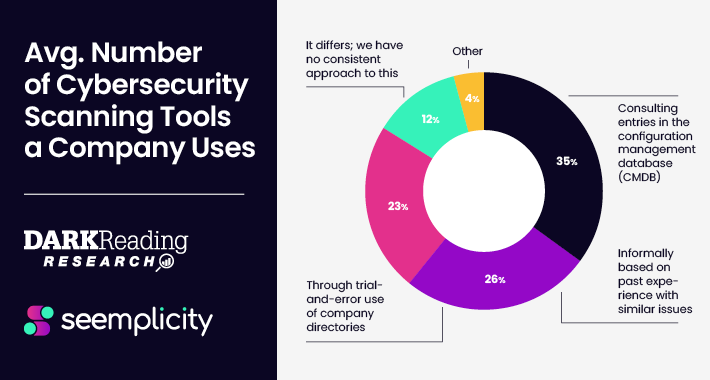
Survey Provides Takeaways for Security Pros to Operationalize their Remediation Life Cycle – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 29, 2023The Hacker NewsRemedial Operations Ask any security professional and they’ll tell you that remediating risks from various siloed security...
Citrix NetScaler Alert: Ransomware Hackers Exploiting Critical Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 29, 2023The Hacker NewsVulnerability / Network Security Unpatched Citrix NetScaler systems exposed to the internet are being targeted by unknown...
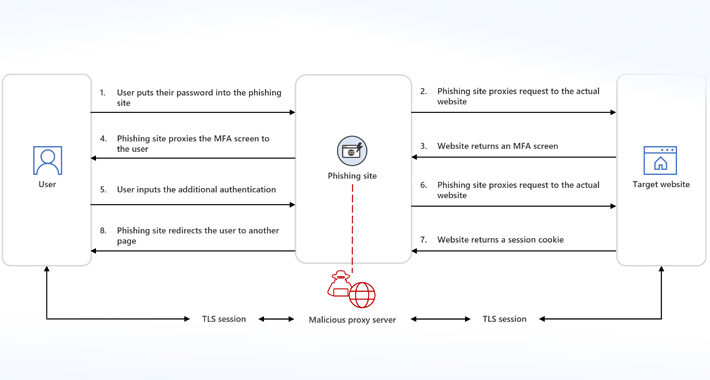
Phishing-as-a-Service Gets Smarter: Microsoft Sounds Alarm on AiTM Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 29, 2023THNOnline Security / Cyber Threat Microsoft is warning of an increase in adversary-in-the-middle (AiTM) phishing techniques, which are being...
Motherboard Mishaps Undermine Trust, Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Microsoft’s latest Windows Preview appears to trigger a bug on some motherboards made by computer hardware...
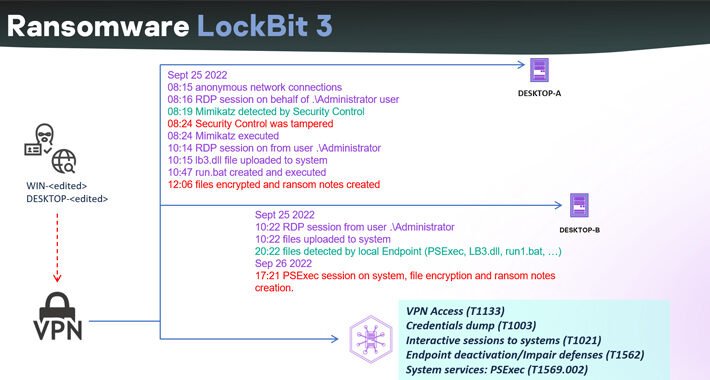
Cybercriminals Harness Leaked LockBit Builder in Wave of New Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Threat actors are using and customizing leaked Lockbit code to carry out their own ransomware attacks....
Considerations for Reducing Risk When Migrating to the Cloud – Source: www.darkreading.com
Source: www.darkreading.com – Author: Rob Sadowski, Director, Trust & Security Product Marketing for Google Cloud at Google The moment your organization begins planning for a cloud...
Financial Firms Breached in MOVEit Cyberattacks Now Face Lawsuits – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Financial services companies breached as a result of MOVEit zero-day vulnerability are facing a flurry of class...
London Police Warned to Stay Vigilant Amid Major Data Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Greater London’s Metropolitan Police have been warned that their information — names, ranks, ID numbers, vetting levels,...
Authentication Outage Underscores Why ‘Fail Safe’ Is Key – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading One week ago today, social media accounts for the information-system services at several universities and colleges...
Back to School Reminder – Keep Your Mac Clean! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Key points from our research: Around early-mid August, we noticed an increase in MacOS malware detections, specifically AdLoad and UpdateAgent in IronDome,...
Experts Uncover How Cybercriminals Could Exploit Microsoft Entra ID for Elevated Privilege – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 28, 2023THNVulnerability / Active Directory Cybersecurity researchers have discovered a case of privilege escalation associated with a Microsoft Entra ID...
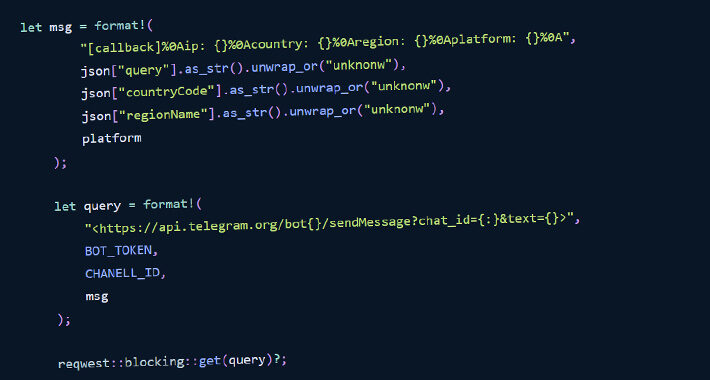
Developers Beware: Malicious Rust Libraries Caught Transmitting OS Info to Telegram Channel – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 28, 2023THNSupply Chain / Software Security In yet another sign that developers continue to be targets of software supply chain...
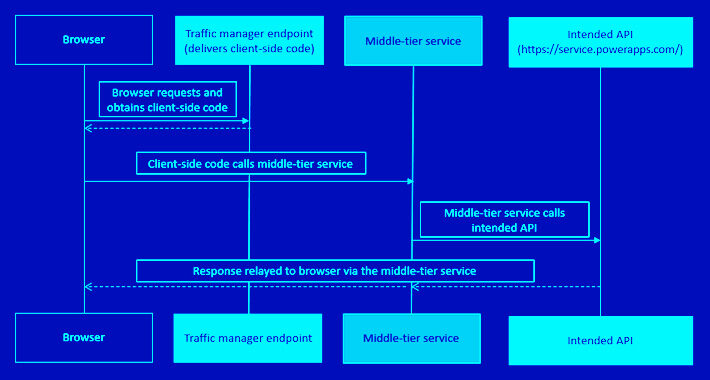
Cyberattacks Targeting E-commerce Applications – Source:thehackernews.com
Source: thehackernews.com – Author: . Cyber attacks on e-commerce applications are a common trend in 2023 as e-commerce businesses become more omnichannel, they build and deploy...
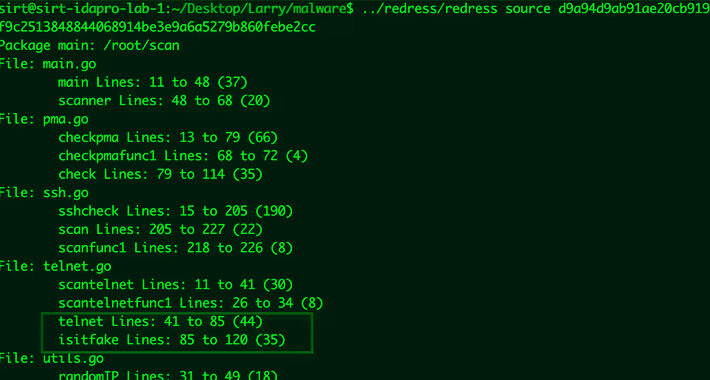
KmsdBot Malware Gets an Upgrade: Now Targets IoT Devices with Enhanced Capabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 28, 2023THNInternet of Things / Malware An updated version of a botnet malware called KmsdBot is now targeting Internet of...
Vendors Training AI With Customer Data is an Enterprise Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Zoom received some flak recently for planning to use customer data to train its machine learning...
LockBit 3.0 Ransomware Builder Leak Gives Rise to Hundreds of New Variants – Source:thehackernews.com
Source: thehackernews.com – Author: . The leak of the LockBit 3.0 ransomware builder last year has led to threat actors abusing the tool to spawn new...
Kroll Suffers Data Breach: Employee Falls Victim to SIM Swapping Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 26, 2023THNData Breach / SIM Swapping Risk and financial advisory solutions provider Kroll on Friday disclosed that one of its...
China Unleashes Flax Typhoon APT to Live Off the Land, Microsoft Warns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading A China-backed advanced persistent threat (APT) group dubbed Flax Typhoon has installed a web of persistent,...
Luna Grabber Malware Targets Roblox Gaming Devs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Since the start of this month, researchers at ReversingLabs have found a host of malicious, multistage packages...
‘Whiffy Recon’ Malware Transmits Device Location Every 60 Seconds – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading Researchers have uncovered the “Whiffy Recon” malware being deployed by the SmokeLoader botnet, which is a...