Source: thehackernews.com – Author: . Sep 12, 2023THNBrowser Security / Zero Day Google on Monday rolled out out-of-band security patches to address a critical security flaw...
Author: admin
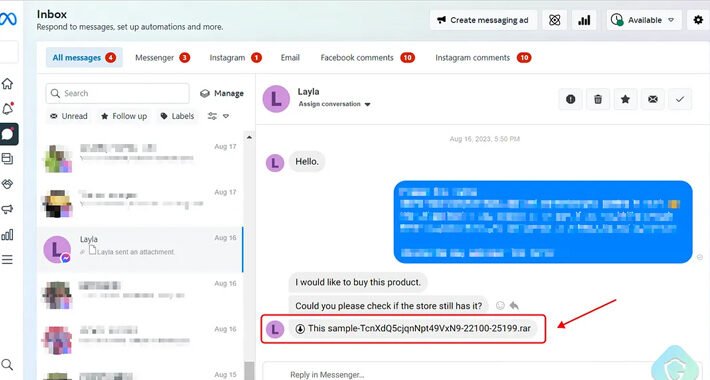
Vietnamese Hackers Deploy Python-Based Stealer via Facebook Messenger – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 11, 2023THNMalware / Social Media A new phishing attack is leveraging Facebook Messenger to propagate messages with malicious attachments from...
Charming Kitten’s New Backdoor ‘Sponsor’ Targets Brazil, Israel, and U.A.E. – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 11, 2023THNCyber Espionage / Malware The Iranian threat actor known as Charming Kitten has been linked to a new wave...
How to Prevent API Breaches: A Guide to Robust Security – Source:thehackernews.com
Source: thehackernews.com – Author: . With the growing reliance on web applications and digital platforms, the use of application programming interfaces (APIs) has become increasingly popular....
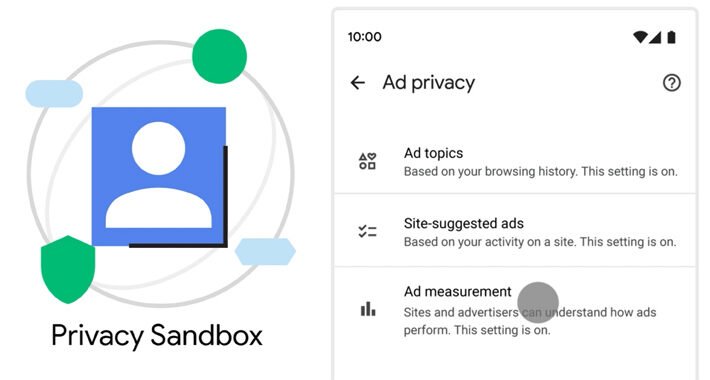
Google Chrome Rolls Out Support for ‘Privacy Sandbox’ to Bid Farewell to Tracking Cookies – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 11, 2023THNPrivacy / Online Security Google has officially begun its rollout of Privacy Sandbox in the Chrome web browser to...
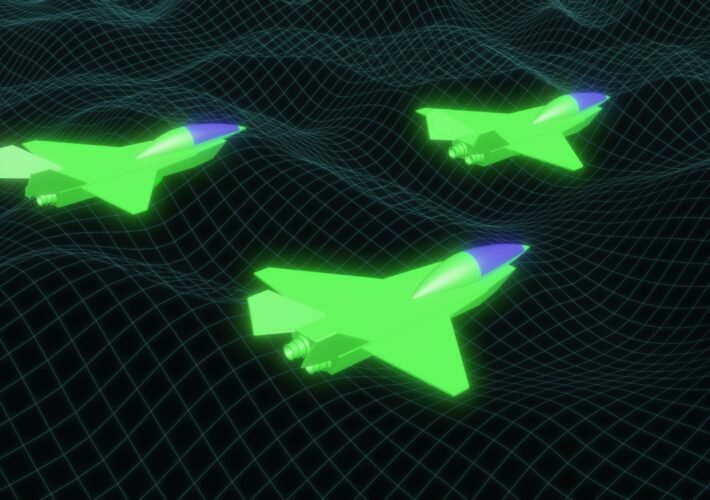
Iranian APT Hits US Aviation Org via ManageEngine, Fortinet Bugs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading State-sponsored threat actors have exploited a US aeronautical organization, using known vulnerabilities in Zoho ManageEngine software...
Attackers Abuse Google Looker Studio to Evade DMARC, Email Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Cyberthreat actors are abusing Google’s Looker Studio data-visualization tool to deliver phishing-lure pages that ultimately steal both money and...
Overcoming the Rising Threat of Session Hijacking – Source: www.darkreading.com
Source: www.darkreading.com – Author: Trevor Hilligoss, Senior Director of Security Research, SpyCloud From passkeys to multifactor authentication (MFA), most businesses are embracing solutions that protect sensitive information to...
Cybercriminals Using PowerShell to Steal NTLMv2 Hashes from Compromised Windows – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 11, 2023THNEndpoint Security / Malware A new cyber attack campaign is leveraging the PowerShell script associated with a legitimate red...
New HijackLoader Modular Malware Loader Making Waves in the Cybercrime World – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 11, 2023THNCyber Crime / Malware A new malware loader called HijackLoader is gaining traction among the cybercriminal community to deliver...
3 Ways to Expand the Cyber Talent Pool From Splash Pad to Watering Hole – Source: www.darkreading.com
Source: www.darkreading.com – Author: Erin Weiss Kaya, Senior Cyber Talent and Organizational Strategist, Booz Allen Hamilton Every so often, a new statistic makes headlines about the...
Critical Security Bug Opens Cisco BroadWorks to Complete Takeover – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading A critical security vulnerability in Cisco’s BroadWorks unified collaboration and messaging platform could pave the...
Microsoft, Google Take on Obsolete TLS Protocols – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Microsoft plans to disable older versions of the Transport Layer Security (TLS) protocol, the ubiquitous communications...
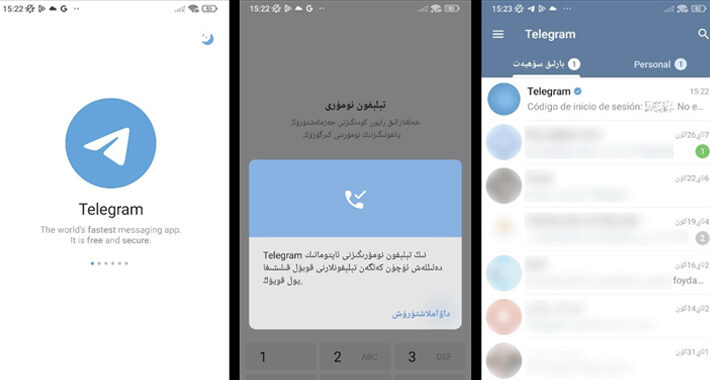
Millions Infected by Spyware Hidden in Fake Telegram Apps on Google Play – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 09, 2023THNMobile Security / Spyware Spyware masquerading as modified versions of Telegram have been spotted in the Google Play Store...
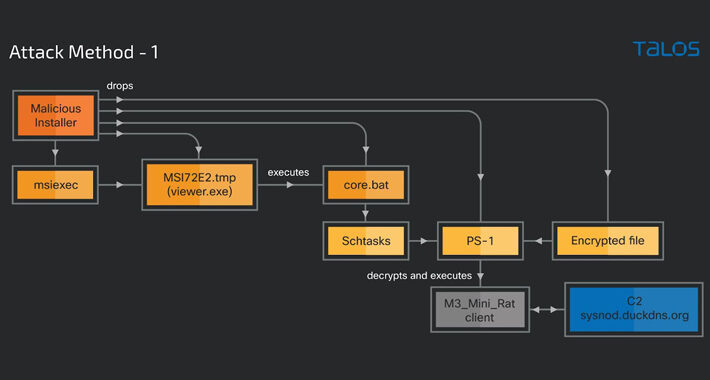
Cybercriminals Weaponizing Legitimate Advanced Installer Tool in Crypto-Mining Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 09, 2023THNMalware / Hacking A legitimate Windows tool used for creating software packages called Advanced Installer is being abused by...
Cybersecurity Insights with Contrast CISO David Lindner | 9/8 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 Prompt injection is becoming a serious concern for those using current AI technologies. When using...
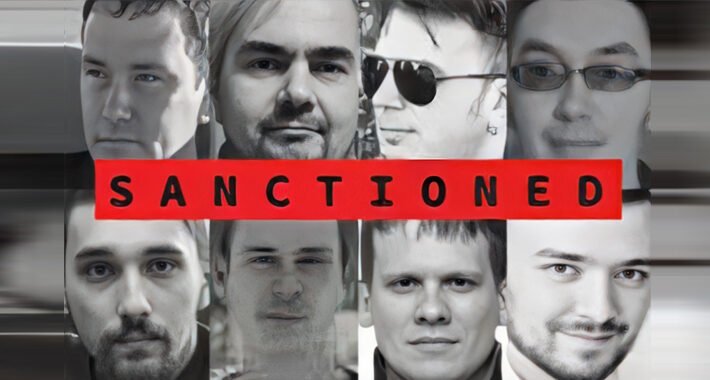
U.K. and U.S. Sanction 11 Russia-based Trickbot Cybercrime Gang Members – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 08, 2023THNCybercrime / Malware The U.K. and U.S. governments on Thursday sanctioned 11 individuals who are alleged to be part...
Cisco Issues Urgent Fix for Authentication Bypass Bug Affecting BroadWorks Platform – Source:thehackernews.com
Source: thehackernews.com – Author: . Cisco has released security fixes to address multiple security flaws, including a critical bug, that could be exploited by a threat...
Protecting Your Microsoft IIS Servers Against Malware Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Microsoft Internet Information Services (IIS) is a web server software package designed for Windows Server. Organizations commonly use Microsoft IIS servers...
‘Evil Telegram’ Spyware Campaign Infects 60K+ Mobile Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Dangerous spyware masquerading as a set of legitimate Telegram “mods” inside the official Google Play...
Kenya Initiates Public Sector Digital Skills Training, No Mention of Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Kenya plans to open a center of excellence to better train public sector staff in digital...
Trickbot, Conti Sanctions Affect Top Cybercrime Brass – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The Russia-based Trickbot and Conti cybercrime syndicates are facing increased pressure from the United States and the...
Securing Your Legacy: Identities, Data, and Processes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dirk Schrader, Resident CISO (EMEA) & VP of Security Research, Netwrix Legacy systems are the bane of IT pros everywhere. “Legacy” generally...
Overcoming Open Source Vulnerabilities in the Software Supply Chain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft As workforces grow increasingly digital, developers are looking for new ways to streamline their workloads. Currently, 78% of businesses report using...
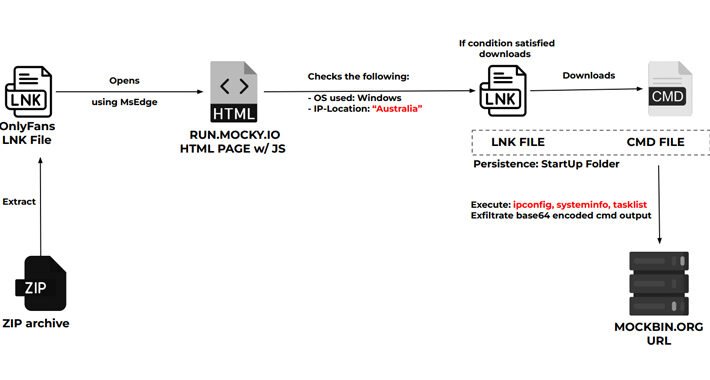
North Korean Hackers Exploit Zero-Day Bug to Target Cybersecurity Researchers – Source:thehackernews.com
Source: thehackernews.com – Author: . Threat actors associated with North Korea are continuing to target the cybersecurity community using a zero-day bug in unspecified software over...
CISA Warning: Nation-State Hackers Exploit Fortinet and Zoho Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 08, 2023THNEndpoint Security / Exploit The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday warned that multiple nation-state actors...
Apple Rushes to Patch Zero-Day Flaws Exploited for Pegasus Spyware on iPhones – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 08, 2023THNSpyware / Vulnerability Apple on Thursday released emergency security updates for iOS, iPadOS, macOS, and watchOS to address two...
Vendor Comparison: DIY Home Security Systems – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: When it comes to DIY home security, there are many systems and components to consider and many decisions to make. This vendor...
Microsoft ID Security Gaps That Let Threat Actor Steal Signing Key – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Several security missteps on Microsoft’s part allowed a China-based threat actor to forge authentication tokens and...
North Korean Hackers Target Security Researchers — Again – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading North Korean state-supported threat actors are targeting security researchers — the second such campaign in the...