Source: www.darkreading.com – Author: Dr. Sean Costigan, Director of Cyber Policy, Red Sift Amid relentless cyberattacks and mounting regulatory pressures, security culture has been thrust into...
Author: admin
Do CISOs Have to Report Security Flaws to the SEC? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Evan Schuman, Contributing Writer, Dark Reading Now that the SEC wants to know about any material security incidents within four days of...
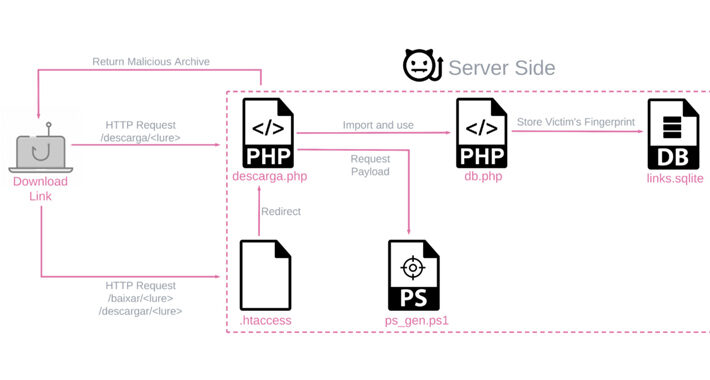
BBTok Banking Trojan Impersonates 40+ Banks to Hijack Victim Accounts – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Threat actors are targeting hundreds of banking customers in Latin America with a new variant of an...
Hikvision Intercoms Allow Snooping on Neighbors – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading A concerning Internet of Things cyberattack vector has been uncovered — one that can turn the neighboring...
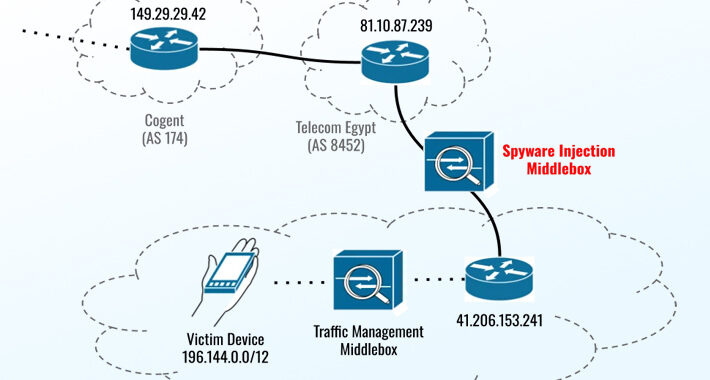
New Apple Zero-Days Exploited to Target Egyptian ex-MP with Predator Spyware – Source:thehackernews.com
Source: thehackernews.com – Author: . The three zero-day flaws addressed by Apple on September 21, 2023, were leveraged as part of an iPhone exploit chain in...
Cybersecurity Insights with Contrast CISO David Lindner | 9/22 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 There will always be a balance in the psychological acceptability of any security controls put...
TikTok API Rules Stymie Analysis of US User Data, Academics Say – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading New terms of service for researchers to access TikTok’s API are a deterrent to analysis of the...
Hackers Let Loose on Voting Gear Ahead of US Election Season – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Election machine manufacturers are opening their wares to hackers in an effort to harden voting security ahead...
Akira Ransomware Mutates to Target Linux Systems, Adds TTPs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading Arika ransomware has continued to evolve since emerging as a threat in March, expanding its reach...
NFL, CISA Look to Intercept Cyber Threats to Super Bowl LVIII – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The NFL is workshopping game plays for Super Bowl LVIII — of the cybersecurity sort....
Apple Fixes 3 More Zero-Day Vulnerabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In an emergency security update, Apple has identified three zero-day vulnerabilities affecting iPhones and Mac products that...
New Variant of Banking Trojan BBTok Targets Over 40 Latin American Banks – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 22, 2023THNMalware / Cyber Threat An active malware campaign targeting Latin America is dispensing a new variant of a banking...
How to Interpret the 2023 MITRE ATT&CK Evaluation Results – Source:thehackernews.com
Source: thehackernews.com – Author: . Thorough, independent tests are a vital resource for analyzing provider’s capabilities to guard against increasingly sophisticated threats to their organization. And...
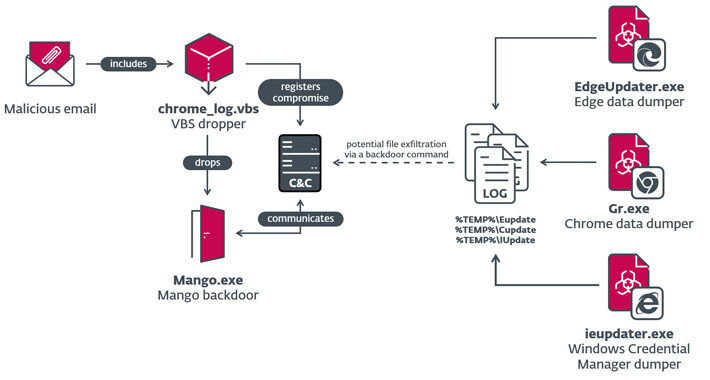
Iranian Nation-State Actor OilRig Targets Israeli Organizations – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 22, 2023THNCyber Attack / Malware Israeli organizations were targeted as part of two different campaigns orchestrated by the Iranian nation-state...
High-Severity Flaws Uncovered in Atlassian Products and ISC BIND Server – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 22, 2023THNServer Security / Vulnerability Atlassian and the Internet Systems Consortium (ISC) have disclosed several security flaws impacting their products...
Apple Rushes to Patch 3 New Zero-Day Flaws: iOS, macOS, Safari, and More Vulnerable – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 22, 2023THNZero Day / Vulnerability Apple has released yet another round of security patches to address three actively exploited zero-day...
Cisco Moves into SIEM with $28B Deal to Acquire Splunk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer, Dark Reading Cisco signaled it intends to reshape secure information and event management (SIEM) by pulling the trigger...
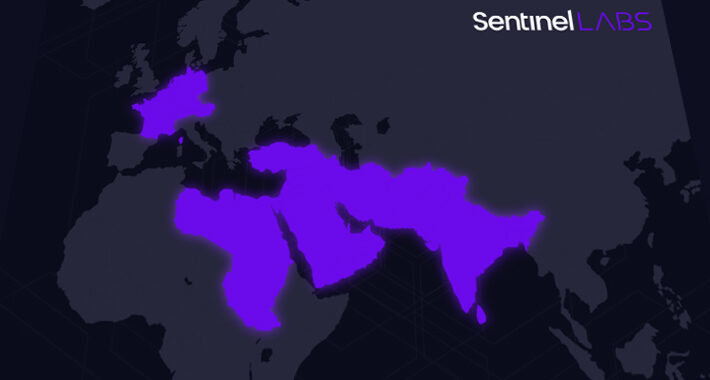
Mysterious ‘Sandman’ APT Targets Telecom Sector With Novel Backdoor – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Telecom companies can add one more sophisticated adversary to the already long list of advanced persistent...
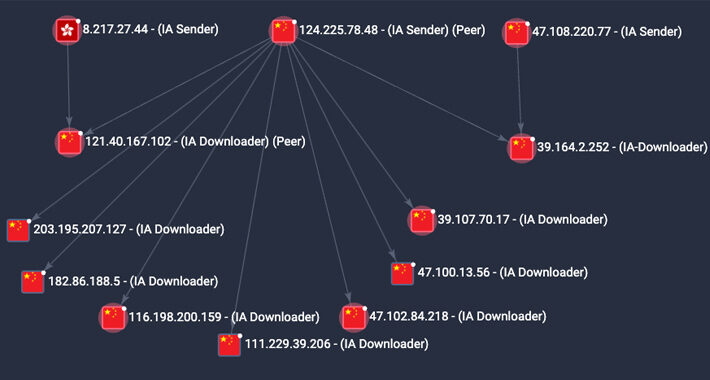
‘Gold Melody’ Access Broker Plays on Unpatched Servers’ Strings – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A initial access broker (IAB) is still running rampant despite being tracked for seven years by...
T-Mobile Racks Up Third Consumer Data Exposure of 2023 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Multiple T-Mobile USA customers have gone to social media to report seeing the sensitive information of other...
Secure Browser Tech Is Having a Moment – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading The rise of cloud applications and infrastructure makes the Web browser the logical place for instituting...
MGM Restores Casino Operations 10 Days After Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Cha-ching! MGM Resorts’ hotel and casino operations are back in business following a devastating ransomware attack. Operations,...
Growing Chinese Tech Influence in Africa Spurs ‘Soft Power’ Concerns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Chinese companies are rapidly deploying technology to enable telecommunications, mobile payments, smart cities and underwater fiber...
SSL Certificate Best Practices Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: SSL certificates are essential for encrypting traffic between systems such as clients, which access servers via web browsers or applications that communicate...
Mysterious ‘Sandman’ Threat Actor Targets Telecom Providers Across Three Continents – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023THNTelecom Security / Cyber Attack A previously undocumented threat actor dubbed Sandman has been attributed to a set of...
Researchers Raise Red Flag on P2PInfect Malware with 600x Activity Surge – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023THNBotnet / Cyber Threat The peer-to-peer (P2) worm known as P2PInfect has witnessed a surge in activity since late...
The Rise of the Malicious App – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023The Hacker NewsSaaS Security / App Security Security teams are familiar with threats emanating from third-party applications that employees...
Overview of IoT threats in 2023 – Source: securelist.com
Source: securelist.com – Author: Vitaly Morgunov, Yaroslav Shmelev, Kaspersky Security Services, Kaspersky ICS CERT IoT devices (routers, cameras, NAS boxes, and smart home components) multiply every...
Will Generative AI Kill the Nigerian Prince Scam? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading It was nearly two decades ago that Weldong Xu, a 38-year-old Harvard professor, was arraigned at...
GitLab Users Advised to Update Against Critical Flaw Immediately – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading GitLab users need to update their servers urgently to protect against a new critical flaw that could...