The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Author: admin
ChatGTP – The impact of Large Language Models on Law Enforcement by EUROPOL
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Communicating the value of cybersecurity to boards and leadership – Seven strategies for life sciences and health care organizations.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Allianz 2022 Risk Barometer – The most important business risks for the next 12 months and beyond, based on the insight of 2,650 risk management experts from 89 countries and territories.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Developing Cyber Security as a Profession – A report by the Global Forum on Cyber Security Expertise.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CROWDSTRIKE 2023 GLOBAL THREAT REPORT
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Importance of Risk Appetite in Risk Assessment – by MVP – Minimun Viable Protection
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DevOps Tools and Insfrastructure Under Attack by Wallarm
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NSA’S Top Ten Cybersecurity Mitigation Strategies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Chief Information Security Officers – CISOs – Challenges & Priorities Survey Analysys Report by European Cyber Security Org (ECS)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber-Risk Oversight2020 – Key Principles and Practical Guidance for Corporate Boards by NACD Internet Security Alliance
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
COBIT ISACA 5 – A Business Framework for the Governance and Management of Enterprise IT
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The State of Cloud Security Report 2022 – A report on the cloud risks and security challenges organizations are experiencing in 2022 by Snyk
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Guide to Cyber Risk – Managing the Impact of Increasing Interconnectivity by Allianz
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The CISOs Guide to Post-Quantum Standarization by QUANTINUUM
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
FBI Warns of Rising Trend of Dual Ransomware Attacks Targeting U.S. Companies – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 30, 2023THNRansomware / Cyber Threat The U.S. Federal Bureau of Investigation (FBI) is warning of a new trend of dual...
Securing AI: What You Should Know – Source: www.darkreading.com
Source: www.darkreading.com – Author: Anton Chuvakin, Security Advisor at Office of the CISO, Google Cloud Machine-learning tools have been a part of standard business and IT...
How Can Your Security Team Help Developers Shift Left? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Scott Gerlach, Co-Founder and Chief Security Officer, StackHawk Question: How can I get my organization to shift its security left without slowing...
DHS: Physical Security a Concern in Johnson Controls Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In the latest development around the cyberattack impacting Johnson Controls International (JIC), officials at the Department of Homeland...
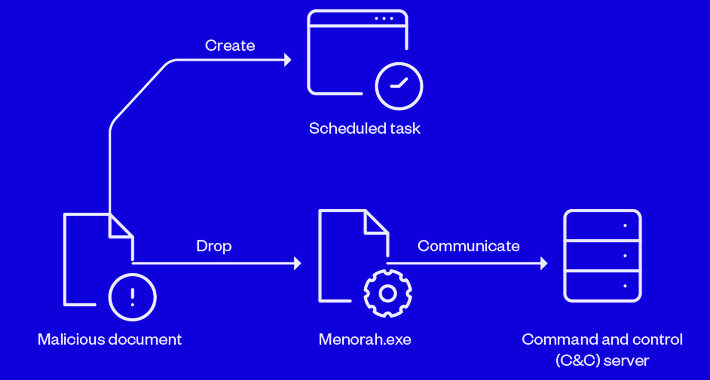
Iranian APT Group OilRig Using New Menorah Malware for Covert Operations – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 30, 2023THNCyber Espionage / Malware Sophisticated cyber actors backed by Iran known as OilRig have been linked to a spear-phishing...
New Critical Security Flaws Expose Exim Mail Servers to Remote Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 30, 2023THNEmail Security / Hacking News Multiple security vulnerabilities have been disclosed in the Exim mail transfer agent that, if...
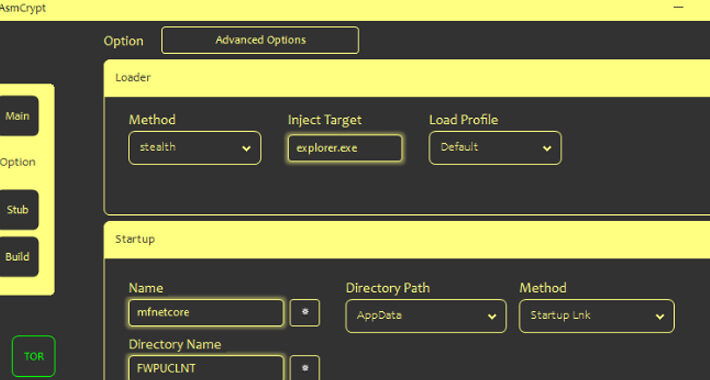
Cybercriminals Using New ASMCrypt Malware Loader Flying Under the Radar – Source:thehackernews.com
Source: thehackernews.com – Author: . Threat actors are selling a new crypter and loader called ASMCrypt, which has been described as an “evolved version” of another...
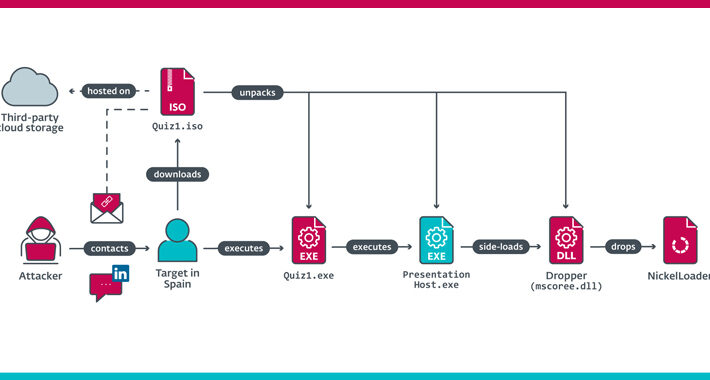
Lazarus Group Impersonates Recruiter from Meta to Target Spanish Aerospace Firm – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 29, 2023THNCyber Espionage / Malware The North Korea-linked Lazarus Group has been linked to a cyber espionage attack targeting an...
Post-Quantum Cryptography: Finally Real in Consumer Apps? – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 29, 2023The Hacker NewsQuantum Computing / Network Security Most people are barely thinking about basic cybersecurity, let alone post-quantum cryptography....
Spyware Vendor Targets Egyptian Orgs With Rare iOS Exploit Chain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading An Israeli surveillanceware company used the three Apple zero-day vulnerabilities disclosed last week to develop an...
DHS Calls Into Question Physical Security in Johnson Controls Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In the latest development of the cyberattack impacting Johnson Controls International (JIC), officials at the Department of...
Cybersecurity Gaps Plague US State Department, GAO Report Warns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading The US Department of State must fully implement its cybersecurity risk program and take additional steps...
Move Over, MOVEit: Critical Progress Bug Infests WS_FTP Software – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading For the second time in recent months, Progress Software is requiring enterprise security teams to drop...
People Still Matter in Cybersecurity Management – Source: www.darkreading.com
Source: www.darkreading.com – Author: Curtis Franklin, Senior Analyst, Omdia In the run-up to the 1992 US presidential election, Bill Clinton’s campaign famously had a large sign...
Attacks on Azerbaijan Businesses Drop Malware via Fake Image Files – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading A spear-phishing email posing as a memo from the president of an Azerbaijan company hid malware...