The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Author: admin
How to Build a Security Operation Center in Budget by AT&T Cybersecurity
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Turning a Cybersecurity Strategy Into Reality – A Holistic Performance Management Framework by Boston Consulting Group & Saudi Telecomunication Company
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
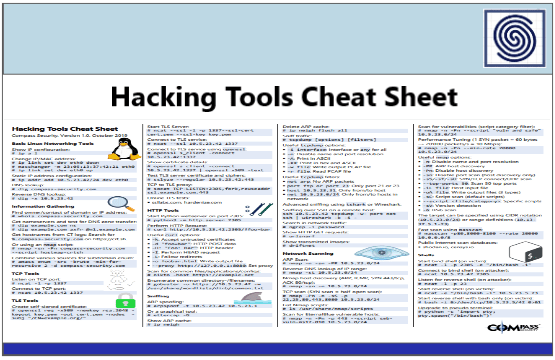
Hacking Tools Cheat Sheet by Compass Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 VEEAM Ransomware Trends Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OSINT – The Most Complete Open Source Intelligence Overview by Joas Antonio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ENISA THREAT LANDSCAPE FOR RANSOMWARE ATTACK REPORT JULY 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SANS Offensive Operations – ChatGPT for Offensive Security – What is ChatGPT and how can it be used in offensive security ?
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
MITRE ATTACK Framework Everything Yoy Need to Know by Hackercombat
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Guidance for Critical Areas of Focus in Cloud Computing v4.0 by CSA Cloud Security Alliance
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A SANS 2021 survey – Security operations center
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Enabling 5G Security with Continuos Monitoring by Booz Allen Hamilton
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Complete Guide to Implementing DevSecOps in AWS by aspire
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Guide to DevSecOps Tools and Continuous Security For an Enterprise by Navdeep Sing gill
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of Kubernetes Security Report 2022 by RedHat
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Effective Purple Teaming by PlexTrac
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Modern Malware for Dummies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
API Security for Dummies Series – Data Theorem Special Edition
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The State of SIEM Detection Risk 2022 Report – Quantifying the gaps in MITRE ATT&CK coverage for productions SIEMs
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Blue Team Strategies – Uncover the secrets of blue teams to combat cyber threats your organization
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Advancing Supply Chain Security in Oil and Gas an Industry Analysis by World Economic Forum
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Introduction to Malware Analysis for Beginners by LetsDefend
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TOR AND THE DARKNET – Remain Anonymous and Evade NSA Spying by James Smith
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
7 Best Reasons to be a CISO by Michaell Hill UK Editor CSO
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TELECOM SECURITY INCIDENTS REPORT 2021 BY ENISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
MAPPING THE RANSOMWARE PAYMENT ECOSYSTEM BY ZOE BRAMMER – IST Institute of Security and Technology
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Nozomi OT IoT Security Report – Cyber War Insights, Threats and Trends, Recommendations
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DevOps Tools and Insfrastructure Under Attack by Wallarm
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NSA’S Top Ten Cybersecurity Mitigation Strategies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The State of Cloud Security Report 2022 – A report on the cloud risks and security challenges organizations are experiencing in 2022 by Snyk
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...