The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Author: admin
Blockchain Security and AML Analysis Report 2022 Mid-Year by SLOWMIST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Responding to Serious Cyber Security Incidents by Cyber and Infrastructure Security Centre.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 Annual Report on Implementation – CSC 2.0 by Jiwon Ma – Mark Montgomery
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Adopting secure DevOps – An introduction to transforming your organization by KPMG
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Metaverse – Concepts and Issues for Congress by Congressional Research Service
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Web Security Testing Guide by OWASP
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
INTRUSION DETECTION GUIDE – The fields leading experts show exactly how to detect, deter, and respond to security threats by PEERLYST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Complete Guide to Understanding Apple Mac Security for Enterprise by SentinelOne
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Threat Intelligence Handbook – A Practical Guide for Security Teams to Unlocking the Power of Intelligence.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Open Source Tools
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Threat Hunting Playbook – Learn how to embrace a proactive security posture by Rank.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Microsoft Active Directory – Security Self Assesment Guide 2022 by Huy Kha
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A checklist for efective Threath Hunting by SecurityHQ
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Business Case for Security by CISA – Understand Your Security Posture
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Cyber Risk Playbook – What boards of directors and executives should know about Cyber Risk by FireEye.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Complete Guide to Modernizing your Security Operations Centers (SOCs) by Microsoft and CyberProof
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Operations Center Guidebook – A Practical Guide for a Successful SOC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Turning a Cybersecurity Strategy Into Reality – A Holistic Performance Management Framework by Boston Consulting Group & Saudi Telecomunication Company
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
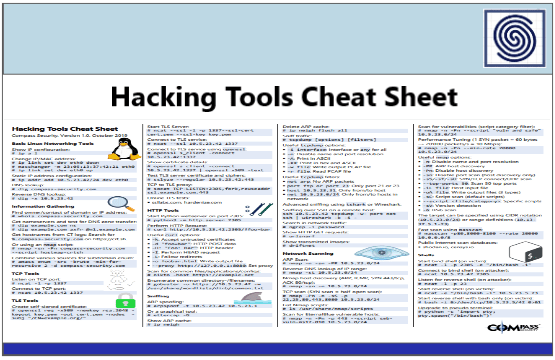
Hacking Tools Cheat Sheet by Compass Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ENISA THREAT LANDSCAPE FOR RANSOMWARE ATTACK REPORT JULY 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Guidance for Critical Areas of Focus in Cloud Computing v4.0 by CSA Cloud Security Alliance
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A SANS 2021 survey – Security operations center
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Enabling 5G Security with Continuos Monitoring by Booz Allen Hamilton
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of Kubernetes Security Report 2022 by RedHat
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Effective Purple Teaming by PlexTrac
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The State of SIEM Detection Risk 2022 Report – Quantifying the gaps in MITRE ATT&CK coverage for productions SIEMs
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Advancing Supply Chain Security in Oil and Gas an Industry Analysis by World Economic Forum
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TELECOM SECURITY INCIDENTS REPORT 2021 BY ENISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NSA’S Top Ten Cybersecurity Mitigation Strategies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...