Luckymouse Uses Compromised MiMi Chat App to Target Windows and Linux SystemsThe news comes from two different security reports published by SEKOIA and Trend MicroLeer másThe...
Author: admin
Software Patches Flaw on macOS Could Let Hackers Bypass All Security Levels
Software Patches Flaw on macOS Could Let Hackers Bypass All Security LevelsAfter deploying the initial attack, the researcher was able to escape the macOS sandboxLeer másAfter...
Black Hat USA 2022: Burnout, a significant issue
Black Hat USA 2022: Burnout, a significant issueThe digital skills gap, especially in cybersecurity, is not a new phenomenon. This problematic is now exacerbate by the...
Comparing Twilio and Slack breach responses
Comparing Twilio and Slack breach responses We recently learned about major security breaches at two tech companies, Twilio and Slack. The manner in which these two...
Top 5 security risks of Open RAN
Top 5 security risks of Open RANWhen a cell phone or other mobile device connects to the nearest cell tower, the communication takes place over something...
Back to School Means More Cyber Concerns
Back to School Means More Cyber ConcernsCyberattacks continue to rise, threatening the educational sector As the 2022-2023 school year looms, so do ongoing cyber threats directly...
Black Hat and DEF CON Roundup
Black Hat and DEF CON Roundup‘Summer Camp’ for hackers features a compromised satellite, a homecoming for hackers and cyberwarfare warnings.Leer másThreatpost‘Summer Camp’ for hackers features a...
The Power of Provenance: From Reactive to Proactive Cybersecurity
The Power of Provenance: From Reactive to Proactive Cybersecurity While next-gen firewalls (NGFW), extended detection and response (XDR) and other security solutions do a great job...
3 ways China’s access to TikTok data is a security risk
3 ways China's access to TikTok data is a security riskThe short-video platform TikTok has come under fire in recent months. Both lawmakers and citizens in...
$23 Million YouTube Royalties Scam
$23 Million YouTube Royalties ScamScammers were able to convince YouTube that other peoples’ music was their own. They successfully stole $23 million before they were caught....
The Week in Cybersecurity: MFA shortcomings paved the way for Cisco breach
The Week in Cybersecurity: MFA shortcomings paved the way for Cisco breach MFA’s shortcomings paved the way for Cisco’s data breach Security Week reports that Cisco released a security...
CVE-2022-2560: CompleteFTP Directory Traversal Arbitrary File Deletion Flaw
CVE-2022-2560: CompleteFTP Directory Traversal Arbitrary File Deletion FlawA high EnterpriseDT CompleteFTP vulnerability (CVE-2022-2560), which was discovered by rgod on Jun 7, 2022, just goes public today...
The Week in Ransomware – August 12th 2022 – Attacking the defenders
The Week in Ransomware - August 12th 2022 - Attacking the defendersIt was a very busy week for ransomware news and attacks, especially with the disclosure...
Why robotexts are scammers’ favorite new tool
Why robotexts are scammers' favorite new toolContenido de la entradaLeer másProofpoint News Feed
The evolution in and importance of securing the cloud 2022
The evolution in and importance of securing the cloud 2022EXECUTIVE SUMMARY: The adoption of cloud services can catalyze business innovation and growth. More than 90% of...
NHS ransomware attack: what happened and how bad is it?
NHS ransomware attack: what happened and how bad is it?Cyber-attacks on health bodies appear to be on the rise again after a hiatus early in the...
Spyware is huge threat to global human rights and democracy, expert warns
Spyware is huge threat to global human rights and democracy, expert warnsCybersecurity expert Ron Deibert to testify to Canadian MPs about troubling spread of invasive surveillance...
Graeme Biggar appointed director general of National Crime Agency
Graeme Biggar appointed director general of National Crime AgencyNew head to focus on ‘hunting ruthless cybercriminals and dismantling organised crime groups’ Graeme Biggar has been appointed...
Fears for patient data after ransomware attack on NHS software supplier
Fears for patient data after ransomware attack on NHS software supplierAttack being investigated for potential data theft as experts warn criminals could use stolen details as...
Patch Madness: Vendor Bug Advisories Are Broken, So Broken
Patch Madness: Vendor Bug Advisories Are Broken, So BrokenDuston Childs and Brian Gorenc of ZDI take the opportunity at Black Hat USA to break down the...
Protect Your Executives’ Personal Digital Lives to Protect Your Company
Protect Your Executives’ Personal Digital Lives to Protect Your CompanyBy Dr Chris Pierson, BlackCloak Founder & CEO Earlier this year, news broke that Chinese hackers had...
The Need for Automated Remediation in Saas Security
The Need for Automated Remediation in Saas SecurityBy Noam Shaar, Co-Founder & CEO, Wing Security For years organizations were leveraging more and more Software-as-a-Service applications […]...
CISA, FBI shared a joint advisory to warn of Zeppelin ransomware attacks
CISA, FBI shared a joint advisory to warn of Zeppelin ransomware attacksThe US Cybersecurity and Infrastructure Security Agency (CISA) and the FBI are warning of Zeppelin...
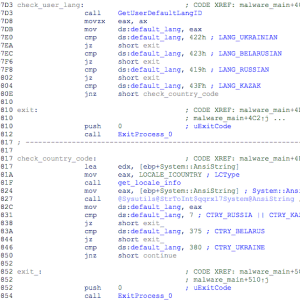
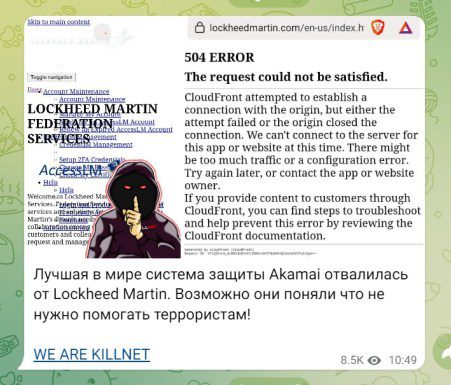
Killnet claims to have breached Lockheed Martin
Killnet claims to have breached Lockheed MartinRussian hacker group Killnet claims to have launched a DDoS attack on the aerospace and defense giant Lockheed Martin. The...
Android Banking Trojan SOVA Comes Back With New Features Including Ransomware
Android Banking Trojan SOVA Comes Back With New Features Including RansomwareSOVA v4 features new capabilities and is reportedly targeting more than 200 mobile applicationsLeer másSOVA v4...
CISA Unveils Cybersecurity Toolkit to Shield US Elections From Hackers
CISA Unveils Cybersecurity Toolkit to Shield US Elections From HackersThe toolkit protects election infrastructure targeted by phishing, ransomware and DDoS attacksLeer másThe toolkit protects election infrastructure...
Recovery From NHS Ransomware Attack May Take a Month
Recovery From NHS Ransomware Attack May Take a MonthManaged service provider Advanced publishes update on recent cyber incidentLeer másManaged service provider Advanced publishes update on recent...
Zeppelin Ransomware Victims May Need Multiple Decryption Keys
Zeppelin Ransomware Victims May Need Multiple Decryption KeysCISA issues new alert about RaaS variantLeer másCISA issues new alert about RaaS variant
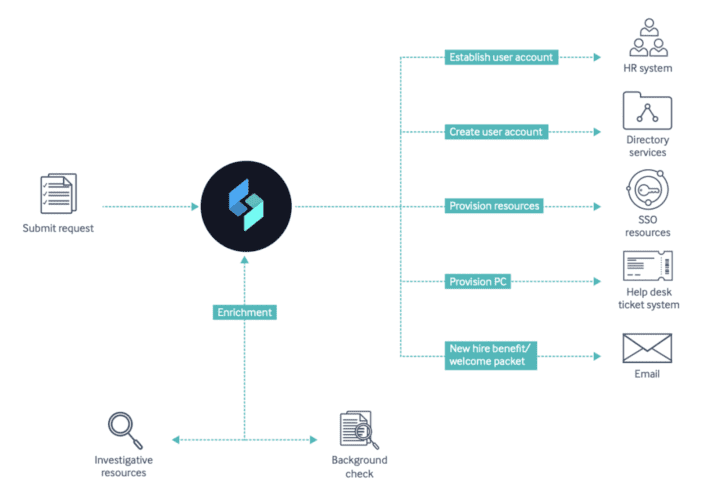
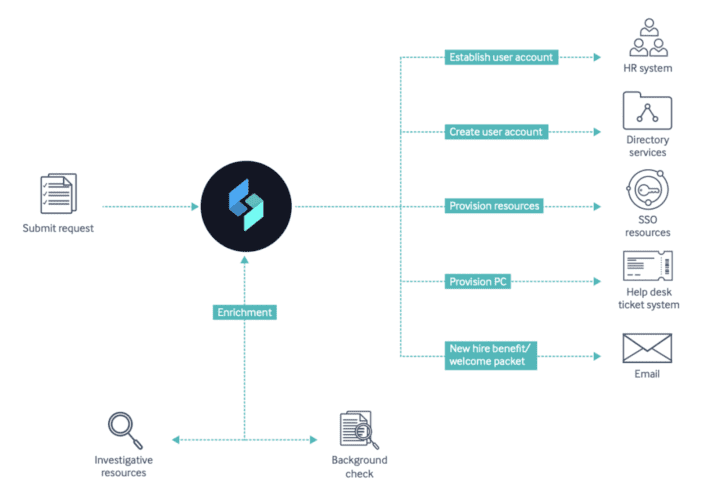
Why You Need to Automate Your Onboarding & Offboarding Process
Why You Need to Automate Your Onboarding & Offboarding ProcessThe growing threat landscape has made organizations rethink the way they handle business processes like onboarding and...
Why You Need to Automate Your Onboarding & Offboarding Process
Why You Need to Automate Your Onboarding & Offboarding ProcessThe growing threat landscape has made organizations rethink the way they handle business processes like onboarding and...