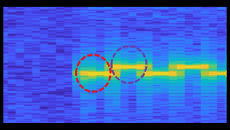
Breaching airgap security: using your phone’s compass as a microphone!One bit per second makes the Voyager probe data rate seem blindingly fast. But it's enough to...
Author: admin
CEO of Israeli Pegasus spyware firm NSO to step down
CEO of Israeli Pegasus spyware firm NSO to step downCEO Shalev Hulio is stepping down as part of NSO reorganisation that will see it focus on...
How Twitter’s whistleblower could boost Elon Musk’s legal battle
How Twitter’s whistleblower could boost Elon Musk’s legal battlePeiter Zatko, former security chief, brought allegations of widespread security threats and spam concerns against the company New...
Mudge Blows Whistle on Alleged Twitter Security Nightmare
Mudge Blows Whistle on Alleged Twitter Security NightmareLawmakers and cybersecurity insiders are reacting to a bombshell report from former Twitter security head Mudge Zatko, alleging reckless...
Black Mail review – Nollywood’s finest head for London with cybercrime thriller
Black Mail review – Nollywood’s finest head for London with cybercrime thrillerA film star faces financial and family ruin as sleazy Russian mobsters blackmail him after...
Thoma Bravo Buying Spree Highlights Hot Investor Interest in IAM Market
Thoma Bravo Buying Spree Highlights Hot Investor Interest in IAM MarketM&A activity in the identity and access management (IAM) space has continued at a steady clip...
Experts question security of online vote to pick Tory leader
Experts question security of online vote to pick Tory leaderTechnology should not be used as it is unproven for such high-stakes elections, one security specialist says...
DevSecOps Gains Traction — but Security Still Lags
DevSecOps Gains Traction — but Security Still LagsAlmost half of teams develop and deploy software using a DevSecOps approach, but security remains the top area of...
Become a Cybersecurity Expert with 18 New Online Courses @ 98% OFF
Become a Cybersecurity Expert with 18 New Online Courses @ 98% OFFWith more data stored in the cloud than ever before, now is a good time...
CISA Adds 7 New Actively Exploited Vulnerabilities to Catalog
CISA Adds 7 New Actively Exploited Vulnerabilities to CatalogThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday moved to add a critical SAP security flaw to its Known...
Hackers Stole Crypto from Bitcoin ATMs by Exploiting Zero-Day Vulnerability
Hackers Stole Crypto from Bitcoin ATMs by Exploiting Zero-Day VulnerabilityBitcoin ATM manufacturer General Bytes confirmed that it was a victim of a cyberattack that exploited a...
New Grandoreiro Banking Malware Campaign Targeting Spanish Manufacturers
New Grandoreiro Banking Malware Campaign Targeting Spanish ManufacturersOrganizations in the Spanish-speaking nations of Mexico and Spain are in the crosshairs of a new campaign designed to...
RTLS Systems Found Vulnerable to MiTM Attacks and Location Tampering
RTLS Systems Found Vulnerable to MiTM Attacks and Location TamperingResearchers have disclosed multiple vulnerabilities impacting Ultra-wideband (UWB) Real-time Locating Systems (RTLS), enabling threat actors to launch...
BSidesTLV 2022 – Gal Bitensky’s ‘SS-Oh No!’
BSidesTLV 2022 – Gal Bitensky’s ‘SS-Oh No!’Our thanks to BSidesTLV for publishing their outstanding conference videos on the organization's YouTube channel. Permalink The post BSidesTLV 2022...
Hacktivism and DDOS Attacks Rise Dramatically in 2022
Hacktivism and DDOS Attacks Rise Dramatically in 20222022 has brought a surge in distributed denial-of-service attacks as well as a dramatic rise in patriotic hacktivism. What’s...
How to Mitigate Insider Threat Using Internal Controls
How to Mitigate Insider Threat Using Internal ControlsAs your company grows, you’ll want to reduce the chances for insider threat. Discover how internal controls can help...
BSidesTLV 2022 – Rotem Reiss’ ‘Code C.A.I.N – Keeping Your Source Code Under Control’
BSidesTLV 2022 – Rotem Reiss’ ‘Code C.A.I.N – Keeping Your Source Code Under Control’Our thanks to BSidesTLV for publishing their outstanding conference videos on the organization's...
Vulnerability management – we’re doing it wrong
Vulnerability management – we’re doing it wrongSecurity professionals (and the people who measure our performance like auditors and regulators) have traditionally taken a stance that “all...
Robert M. Lee’s & Jeff Haas’ Little Bobby Comic – ‘WEEK 235’ (2019 Repost)
Robert M. Lee’s & Jeff Haas’ Little Bobby Comic – ‘WEEK 235’ (2019 Repost) via the respected security expertise of Robert M. Lee and the superlative...
BSidesTLV 2022 – Amichai’s And Stav Shulman’s ‘Now You C(&C), Now You Don’t’
BSidesTLV 2022 – Amichai’s And Stav Shulman’s ‘Now You C(&C), Now You Don’t’Our thanks to BSidesTLV for publishing their outstanding conference videos on the organization's YouTube...
Email and cybersecurity: Fraudsters are knocking
Email and cybersecurity: Fraudsters are knockingCan you remember your first email? Either sending one, or receiving it? I certainly remember explaining to people what email was,...
Multi-Factor Authentication Fatigue Attack, Signal Account Twilio Hack, Facebook and Instagram In-App Browser
Multi-Factor Authentication Fatigue Attack, Signal Account Twilio Hack, Facebook and Instagram In-App BrowserA Cisco employee was compromised by a ransomware gang using a technique called multi-factor...
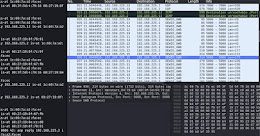
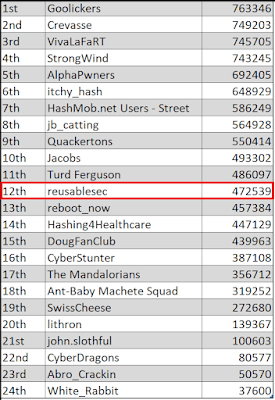
More Password Cracking Tips: A Defcon 2022 Crack Me If You Can Roundup
More Password Cracking Tips: A Defcon 2022 Crack Me If You Can Roundup “We do not learn from experience... we learn from reflecting on experience.” -- John...
7 critical steps for successful security onboarding
7 critical steps for successful security onboardingJerich Beason, CISO, Commercial Bank at Capital One, equates the Great Resignation with the great onboarding. “If you are a...
6 best practices for blue team success
6 best practices for blue team successCybersecurity team conversations these days can feel like a rainbow, with mentions of red, blue and even purple teams. While...
Car Dealership Hit by Major Ransomware Attack
Car Dealership Hit by Major Ransomware AttackHoldcroft Motor Group says most systems back online nowLeer másHoldcroft Motor Group says most systems back online now
Hackers Target ATM Maker for Bitcoins
Hackers Target ATM Maker for BitcoinsGeneral Bytes confirms serious attack last weekLeer másGeneral Bytes confirms serious attack last week
DDoS Protection Weaponized to Deliver RATs
DDoS Protection Weaponized to Deliver RATsNew campaign disguised as fake Cloudflare pop-upLeer másNew campaign disguised as fake Cloudflare pop-up
CISA added 7 new flaws to its Known Exploited Vulnerabilities Catalog
CISA added 7 new flaws to its Known Exploited Vulnerabilities CatalogThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) added 7 new flaws to its Known Exploited Vulnerabilities...
White hat hackers broadcasted talks and hacker movies through a decommissioned satellite
White hat hackers broadcasted talks and hacker movies through a decommissioned satelliteHackers took control of a decommissioned satellite and broadcasted hacking conference talks and hacker movies. ...