What is Big Data Security? Large organizations and enterprises are embracing big data like never before. In fact, New Vantage Partners revealed in 2019 that around...
Author: admin
Russia-linked cyberattacks on Ukraine: A timeline
Russia-linked cyberattacks on Ukraine: A timelineToday is Ukraine Independence day. It's also the six-month anniversary of the official launch of Russia's invasion into Ukraine, with no...
Is your personal data all over the internet? 7 steps to cleaning up your online presence
Is your personal data all over the internet? 7 steps to cleaning up your online presenceYou may not be able to disappear completely from the internet, but...
Researchers warn of darkverse emerging from the metaverse
Researchers warn of darkverse emerging from the metaverseThe metaverse is seen by many companies as a great business opportunity and for new ways of working. Security provider Trend Micro,...
How 2023 cybersecurity budget allocations are shaping up
How 2023 cybersecurity budget allocations are shaping upCybersecurity spending in the coming year may not be recession-proof, but it's likely to be recession-resistant. Still, pressure remains...
WannaCry explained: A perfect ransomware storm
WannaCry explained: A perfect ransomware stormWhat is WannaCry? WannaCry is a ransomware worm that spread rapidly through across a number of computer networks in May of...
Defending in a hostile environment: Key findings from the BlackHat NOC
Defending in a hostile environment: Key findings from the BlackHat NOC Key points The Black Hat network is more unique and complex than a standard enterprise...
FinOps “Crawl, Walk, Run” Maturity Model Applied to Kubernetes
FinOps “Crawl, Walk, Run” Maturity Model Applied to Kubernetes FinOps has become an increasingly popular goal of many organizations. It helps to unite financial teams and...
2022 Cequence Roadshow — Learn the ABCs of API Protection
2022 Cequence Roadshow — Learn the ABCs of API ProtectionSummer’s almost over, and it’s time to head back to class and brush up on the ABCs...
Case Study: DTEX InTERCEPT Helps Multinational Retailer Gain Visibility into Risk in Retail Stores
Case Study: DTEX InTERCEPT Helps Multinational Retailer Gain Visibility into Risk in Retail StoresAs insider risks and threats become more prevalent with the rise of e-commerce...
BSidesTLV 2022 – Ayelet HaShachar Penrod’s ‘Hack LinkedIn Networking (The People Skill, Not The Tech Skill)’
BSidesTLV 2022 – Ayelet HaShachar Penrod’s ‘Hack LinkedIn Networking (The People Skill, Not The Tech Skill)’Our thanks to BSidesTLV for publishing their outstanding conference videos on...
Elastic Security Advances SOAR Integration
Elastic Security Advances SOAR Integration Elastic Security today updated its security orchestration, automation and response (SOAR) platform to provide integrations with similar platforms as part of...
Security Awareness Games in Slack
Security Awareness Games in SlackUsers love ❤️ learning in Slack. We hear this consistently from our users. The interactions are fast and the content is digestible.Games...
Meet Borat RAT, a New Unique Triple Threat
Meet Borat RAT, a New Unique Triple ThreatAtlanta-based cyber risk intelligence company, Cyble discovered a new Remote Access Trojan (RAT) malware. What makes this particular RAT...
CISA Warns of Active Exploitation of Palo Alto Networks’ PAN-OS Vulnerability
CISA Warns of Active Exploitation of Palo Alto Networks' PAN-OS VulnerabilityThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a security flaw impacting Palo Alto Networks...
Researchers Find Counterfeit Phones with Backdoor to Hack WhatsApp Accounts
Researchers Find Counterfeit Phones with Backdoor to Hack WhatsApp AccountsBudget Android device models that are counterfeit versions associated with popular smartphone brands are harboring multiple trojans...
“As Nasty as Dirty Pipe” — 8 Year Old Linux Kernel Vulnerability Uncovered
"As Nasty as Dirty Pipe" — 8 Year Old Linux Kernel Vulnerability UncoveredDetails of an eight-year-old security vulnerability in the Linux kernel have emerged that the...
The Rise of Data Exfiltration and Why It Is a Greater Risk Than Ransomware
The Rise of Data Exfiltration and Why It Is a Greater Risk Than RansomwareRansomware is the de facto threat organizations have faced over the past few...
Suspected Iranian Hackers Targeted Several Israeli Organizations for Espionage
Suspected Iranian Hackers Targeted Several Israeli Organizations for EspionageA suspected Iranian threat activity cluster has been linked to attacks aimed at Israeli shipping, government, energy, and...
New Air-Gap Attack Uses MEMS Gyroscope Ultrasonic Covert Channel to Leak Data
New Air-Gap Attack Uses MEMS Gyroscope Ultrasonic Covert Channel to Leak DataA novel data exfiltration technique has been found to leverage a covert ultrasonic channel to...
XCSSET Malware Updates with Python 3 to Target macOS Monterey Users
XCSSET Malware Updates with Python 3 to Target macOS Monterey UsersThe operators of the XCSSET macOS malware have upped the stakes by making iterative improvements that...
Researchers Warn of AiTM Attack Targeting Google G-Suite Enterprise Users
Researchers Warn of AiTM Attack Targeting Google G-Suite Enterprise UsersThe threat actors behind a large-scale adversary-in-the-middle (AiTM) phishing campaign targeting enterprise users of Microsoft email services have also...
GitLab Issues Patch for Critical Flaw in its Community and Enterprise Software
GitLab Issues Patch for Critical Flaw in its Community and Enterprise SoftwareDevOps platform GitLab this week issued patches to address a critical security flaw in its...
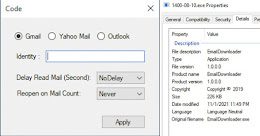
Google Uncovers Tool Used by Iranian Hackers to Steal Data from Email Accounts
Google Uncovers Tool Used by Iranian Hackers to Steal Data from Email AccountsThe Iranian government-backed actor known as Charming Kitten has added a new tool to...
Guide: How Service Providers can Deliver vCISO Services at Scale
Guide: How Service Providers can Deliver vCISO Services at ScaleFrom ransomware to breaches, from noncompliance penalties to reputational damage – cyberthreats pose an existential risk to...
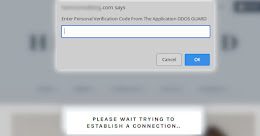
Hackers Using Fake DDoS Protection Pages to Distribute Malware
Hackers Using Fake DDoS Protection Pages to Distribute MalwareWordPress sites are being hacked to display fraudulent Cloudflare DDoS protection pages that lead to the delivery of...
Air-Gapped Devices Can Send Covert Morse Signals via Network Card LEDs
Air-Gapped Devices Can Send Covert Morse Signals via Network Card LEDsA security researcher who has a long line of work demonstrating novel data exfiltration methods from...
Bitcoin ATMs leeched by attackers who created fake admin accounts
Bitcoin ATMs leeched by attackers who created fake admin accountsThe criminals didn't implant any malware. The attack was orchestrated via malevolent configuration changes.Leer másNaked SecurityThe criminals...
Laptop denial-of-service via music: the 1980s R&B song with a CVE!
Laptop denial-of-service via music: the 1980s R&B song with a CVE!We haven't validated this vuln ourselves... but the source of the story is impeccable. (Impeccably dressed,...
Crypto Miners Using Tox P2P Messenger as Command and Control Server
Crypto Miners Using Tox P2P Messenger as Command and Control ServerThreat actors have begun to use the Tox peer-to-peer instant messaging service as a command-and-control method,...