Experts warn that over 80,000 Hikvision cameras are vulnerable to a critical command injection vulnerability.
Security researchers from CYFIRMA have discovered over 80,000 Hikvision cameras affected by a critical command injection vulnerability tracked as CVE-2021-36260. The Chinese vendor addressed the issue in September 2021, but tens of thousands of devices are yet to be patched. An attacker can exploit the flaw by sending specially crafted messages to the web server running on vulnerable devices.
The vulnerability is an unauthenticated Remote Code Execution (RCE) vulnerability in Hikvision IP camera/NVR firmware, it was discovered by a security researcher that goes online with the moniker “Watchful IP.”
“The majority of the recent camera product ranges of Hikvision cameras are susceptible to a critical remote unauthenticated code execution vulnerability even with latest firmware (as of 21 June 2021).” wrote the expert. “
“This permits an attacker to gain full control of device with an unrestricted root shell, which is far more access than even the owner of the device has as they are restricted to a limited “protected shell” (psh) which filters input to a predefined set of limited, mostly informational commands.”
Upon compromising the IP camera, an attacker can also use the hacked device to access internal networks posing a risk to the infrastructure that use the devices.
The researcher pointed out that the exploitation of the issue doesn’t require user interaction, the attacker only needs access to the http(s) server port (typically 80/443).
“Given the deployment of these cameras at sensitive sites potentially even critical infrastructure is at risk,” continues the post. “No username or password needed nor any actions need to be initiated by the camera owner. It will not be detectable by any logging on the camera itself.”
The expert confirmed that every firmware developed since 2016 has been tested and found to be vulnerable.
The vulnerability impacts Hikvision cameras and NVRs, a list of affected products was published in the security advisory published by the vendor.
“A command injection vulnerability in the web server of some Hikvision product. Due to the insufficient input validation, attacker can exploit the vulnerability to launch a command injection attack by sending some messages with malicious commands.” reads the vendor’s advisory.
The root cause of the problem is the insufficient input validation. The vulnerability was reported to the vendor in June, and the company fixed it on September 19 with the release of firmware updates.
Since its public disclosure, two exploits for CVE-2021-36260 were publicly released, in October 2021 and in February 2022 respectively.
This means that it is quite easy for threat actors to scan the Internet for vulnerable devices and compromise them. The issue is known to be actively exploited in the wild, in December 2021 Fortinet researchers reported that the Mirai-based botnet Moobot is leveraging the vulnerability in the webserver of some Hikvision products.
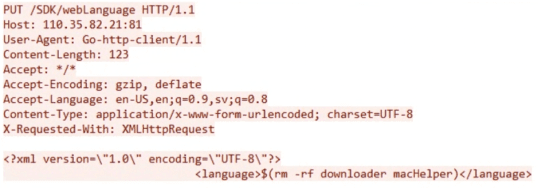
“During our analysis, we observed numerous payloads attempting to leverage this vulnerability to probing the status of devices or extracting sensitive data from victims. One payload in particular caught our attention. It tries to drop a downloader that exhibits infection behavior and that also executes Moobot, which is a DDoS botnet based on Mirai.” reads the analysis published by Fortinet.
Fortinet researchers spotted a downloader for the Moobot malware with the “hikivision” parameter, it saves final payload as “macHelper.”
The malware also modifies basic commands like “reboot” to prevent an administrator from rebooting the infected device.
Researchers from CYFIRMA while observing evolution in the underground forums, noticed multiple hackers looking to collaborate on exploiting Hikvision cameras using the CVE-2021-36260 flaw.
The researchers have analyzed a sample of approximately 285000 Hikvision web servers exposed on the Internet as of July 2022.
Top 10 nations using Hikvision camera products (as per the sample analysed) include China (12690), USA (10611), and Vietnam (7394). ther countries in the list are the UK, Ukraine, Thailand, South Africa, France, the Netherlands, and Romania. According to the experts, over 2300 organizations using Hikvision Cameras are still vulnerable.
“However, we have reasons to believe that – Chinese threat groups such as MISSION2025/APT41, APT10 and its affiliates, as well as unknown Russian threat actor groups could potentially exploit vulnerabilities in these devices to fulfil their motives (which may include specific geo-political considerations).” reads the report published by CYFIRMA.
Experts pointed out that multiple threat actors, including China-linked APT41 and APT10, as well as Russia-linked APT groups could target vulnerable devices.
“Given the current geopolitical driven cyberwarfare brewing across the world, we suspect an uptick in cyberattacks from various nation-state threat actors on critical infrastructure, state entities, defence organizations, and many more. Open vulnerabilities and ports in such devices will only compound the impact on targeted organizations and their countries economic and state prowess.” concludes the report. “It is paramount to patch the vulnerable software of the Hikvision camera products to the latest version. Organizations need to adopt a ETLM powered risk-based approach to cybersecurity decision making to minimize possible exposures and threats coming their way.”
Follow me on Twitter: @securityaffairs and Facebook
(SecurityAffairs – hacking, Hikvision)
The post Over 80,000 Hikvision cameras can be easily hacked appeared first on Security Affairs.
Leer másSecurity Affairs
Views: 2