Source: thehackernews.com – Author: . Dec 22, 2023NewsroomThreat Intelligence / Supply Chain Attack Organizations in the Defense Industrial Base (DIB) sector are in the crosshairs of...
Author: admin
Ransomware Attacks in November Rise 67% From 2022 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Total ransomware cases up 30% from October Industrials (33%), Consumer Cyclicals (18%), Healthcare (11%), remain most targeted sectors North America (50%), Europe...
New DMARC Data Shows 75% Increase in Suspicious Emails Hitting Inboxes – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE 20 December 2023 – New data from EasyDMARC has revealed the increasing threat of phishing as emails intercepted by the...
‘BattleRoyal’ Hackers Deliver DarkGate RAT Using Every Trick – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Karel Tupy via Alamy Stock Photo This fall, an unidentified threat actor executed dozens of varied social...
Russian Water Utility Hacked in Retaliation for Kyivstar Hit – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 1 Min Read Source: Andrii Dragan via Alamy Stock Photo According to reports, operations at Moscow-based water...
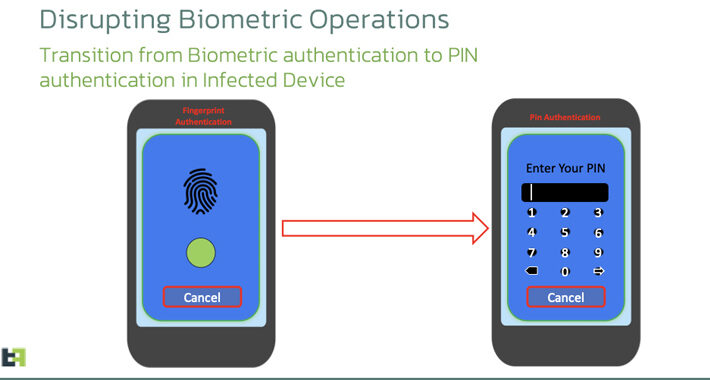
Chameleon Android Trojan Offers Biometric Bypass – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer A new variant of an Android banking Trojan has appeared that can bypass biometric security to break into...
As Namibians Rush to Register SIMs, Major Telco Hoards Biometric Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Universal Images Group North America LLC via Alamy Stock Photo This December, citizens of Namibia are faced...
Experts Detail Multi-Million Dollar Licensing Model of Predator Spyware – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 21, 2023NewsroomZero-Day / Mobile Security A new analysis of the sophisticated commercial spyware called Predator has revealed that its ability...
Chameleon Android Banking Trojan Variant Bypasses Biometric Authentication – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity researchers have discovered an updated version of an Android banking malware called Chameleon that has expanded its targeting to include...
New JavaScript Malware Targeted 50,000+ Users at Dozens of Banks Worldwide – Source:thehackernews.com
Source: thehackernews.com – Author: . A new piece of JavaScript malware has been observed attempting to steal users’ online banking account credentials as part of a...
Cost of a Data Breach Report 2023: Insights, Mitigators and Best Practices – Source:thehackernews.com
Source: thehackernews.com – Author: . John Hanley of IBM Security shares 4 key findings from the highly acclaimed annual Cost of a Data Breach Report 2023...
German Authorities Dismantle Dark Web Hub ‘Kingdom Market’ in Global Operation – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 21, 2023NewsroomDark Web / Cybercrime German law enforcement has announced the disruption of a dark web platform called Kingdom Market...
Hackers Exploiting Old MS Excel Vulnerability to Spread Agent Tesla Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 21, 2023NewsroomVulnerability / Phishing Attack Attackers are weaponizing an old Microsoft Office vulnerability as part of phishing campaigns to distribute...
Urgent: New Chrome Zero-Day Vulnerability Exploited in the Wild – Update ASAP – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 21, 2023NewsroomVulnerability / Zero-Day Google has rolled out security updates for the Chrome web browser to address a high-severity zero-day...
Console & Associates, P.C.: ESO Solutions Notifies 2.7M People of Data Breach That Leaked Their SSNs – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE MARLTON, N.J., Dec. 20, 2023 /PRNewswire/ — Approximately 2.7 million patients are being notified that their Social Security numbers and other confidential information were compromised...
Black Hat Europe 2023 Closes on Record-Breaking Event in London – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE LONDON, Dec. 20, 2023 — Black Hat, the cybersecurity industry’s most established and in-depth security event series, today announced the...
Defiant BlackCat Gang Stands Up New Site, Calls for Revenge Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 2 Min Read Source: Sari O’Neal via Alamy Stock Photo BlackCat/ALPHV ransomware leaders claim they have restarted...
Physical Access Systems Open Cyber Door to IT Networks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading 2 Min Read Source: Stephen Barnes Technology via Alamy Stock Photo Cyberattackers can exploit access...
Attackers Exploit 6-Year-Old Microsoft Office Bug to Spread Spyware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Robert Brown via Alamy Stock Photo Attackers are exploiting a 6-year-old Microsoft Office remote code execution (RCE)...
Remote Encryption Attacks Surge: How One Vulnerable Device Can Spell Disaster – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 20, 2023NewsroomNetwork Security / Data Breach Ransomware groups are increasingly switching to remote encryption in their attacks, marking a new...
Feds Snarl ALPHV/BlackCat Ransomware Operation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Source: Imagebroker via Alamy Stock Photo After nearly two weeks of speculation, the US Department of Justice...
Fresh Qakbot Sightings Confirm Recent Takedown Was a Temporary Setback – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Irina Anosova via Shutterstock Qakbot malware is back less than four months after US and international law...
SANS Institute Research Shows What Frameworks, Benchmarks, and Techniques Organizations Use on their Path to Security Maturity – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Respondents overwhelmingly prefer the NIST CSF framework Results show that companies lag in training and cyber-readiness exercises Herndon, Va., December...
Comcast Xfinity Breached via CitrixBleed; 35M Customers Affected – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Sunrise Photos via Alamy Stock Photo The now-infamous CitrixBleed vulnerability has claimed possibly its biggest kill yet:...
Console & Associates, P.C.: Comcast Xfinity Reports Data Breach Exposing Confidential Information of 35M Customers – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE MARLTON, N.J., Dec. 19, 2023 /PRNewswire/ –– Approximately 35 million consumers are being notified that their confidential information was compromised due to a...
Salvador Technologies Raises $6M to Empower Cyber Resilience in Operational Technologies and Critical Infrastructures – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE REHOVOT, Israel Salvador has built its market-leading cyber-attack recovery platform with its patented security failover technology to prevent downtime damage and ensure...
Microsoft Outlook Zero-Click Security Flaws Triggered by Sound File – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer 3 Min Read Source: monticello via Shutterstock Researchers this week disclosed details on two security vulnerabilities in Microsoft...
Microsoft: Multiple Perforce Server Flaws Allow for Network Takeover – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Igor Stevanovic via Alamy Stock Photo Microsoft has identified four vulnerabilities in the Perforce source-code management platform,...
Product Explained: Memcyco’s Real-Time Defense Against Website Spoofing – Source:thehackernews.com
Source: thehackernews.com – Author: . Hands-On Review: Memcyco’s Threat Intelligence Solution Website impersonation, also known as brandjacking or website spoofing, has emerged as a significant threat...
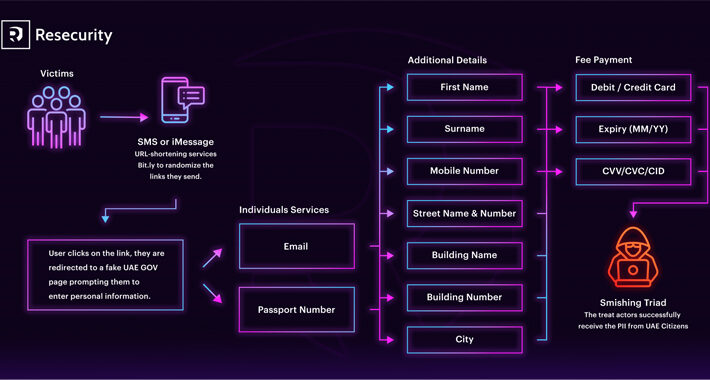
Alert: Chinese-Speaking Hackers Pose as UAE Authority in Latest Smishing Wave – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 20, 2023NewsroomIdentity Theft / SMS Phishing The Chinese-speaking threat actors behind Smishing Triad have been observed masquerading as the United...