Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: GagoDesign via Shutterstock The FBI and the US Cybersecurity and Infrastructure Security Agency (CISA) have issued an...
Author: admin
Q&A: How One Company Gauges Its Employees’ Cybersecurity ‘Fluency’ – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Source: Svyatoslav Lypynskyy via Alamy Stock Photo Professional services firm TAG.Global now requires that all of...
SMB Security Pack – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Small and midsize businesses are increasingly being targeted by cybercriminals — but they often lack the resources and expertise to develop comprehensive...
Transmission of Sensitive Data Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Data in transit means data is at risk if the proper precautions aren’t followed. Data stored inside a securely monitored environment is...
PAX PoS Terminal Flaw Could Allow Attackers to Tamper with Transactions – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomFinancial Data / Vulnerability The point-of-sale (PoS) terminals from PAX Technology are impacted by a collection of high-severity vulnerabilities...
Combating IP Leaks into AI Applications with Free Discovery and Risk Reduction Automation – Source:thehackernews.com
Source: thehackernews.com – Author: . Wing Security announced today that it now offers free discovery and a paid tier for automated control over thousands of AI...
Feds Warn of AndroxGh0st Botnet Targeting AWS, Azure, and Office 365 Credentials – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomBotnet / Cloud Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI)...
Webinar: The Art of Privilege Escalation – How Hackers Become Admins – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024The Hacker NewsCyber Threat / Live Webinar In the digital age, the battleground for security professionals is not only...
New iShutdown Method Exposes Hidden Spyware Like Pegasus on Your iPhone – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomSpyware / Forensic Analysis Cybersecurity researchers have identified a “lightweight method” called iShutdown for reliably identifying signs of spyware...
GitHub Rotates Keys After High-Severity Vulnerability Exposes Credentials – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomVulnerability / Software Security GitHub has revealed that it has rotated some keys in response to a security vulnerability...
Citrix, VMware, and Atlassian Hit with Critical Flaws — Patch ASAP! – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomVulnerability / Cyber Threat Citrix is warning of two zero-day security vulnerabilities in NetScaler ADC (formerly Citrix ADC) and...
Zero-Day Alert: Update Chrome Now to Fix New Actively Exploited Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomBrowser Security / Vulnerability Google on Tuesday released updates to fix four security issues in its Chrome browser, including...
Accenture and SandboxAQ Collaborate to Help Organizations Protect Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE NEW YORK; Jan. 16, 2024 – Accenture (NYSE: ACN) and SandboxAQ are partnering to deliver artificial intelligence (AI) and quantum computing solutions...
Snyk Acquires Helios for Runtime Visibility – Source: www.darkreading.com
Source: www.darkreading.com – Author: Source: Aleks P via Adobe Stock Photo Developer-focused security company Snyk said it has acquired Helios, a startup focused on helping developers...
Savvy Launches Identity-First Security Offering to Combat Toxic Combinations Driving SaaS Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE TEL AVIV, Israel, Jan. 16, 2024 (GLOBE NEWSWIRE) — Savvy, a software-as-a-service (SaaS) security platform provider, today announced its Identity-First Security...
Ivanti Zero-Day Exploits Skyrocket Worldwide; No Patches Yet – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: devilmaya via Alamy Stock Photo Thousands of Ivanti VPN instances have been compromised across the globe in...
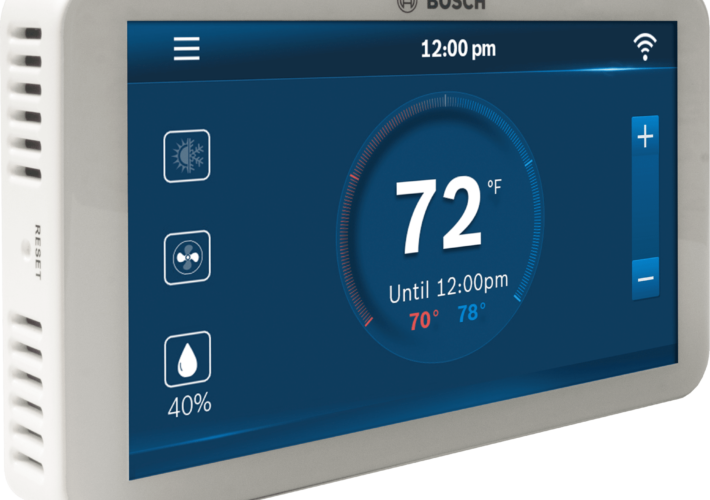
Bosch Smart Thermostat Feels the Heat From Firmware Bug – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer A critical vulnerability has been discovered in the widely used, Web-connected Bosch BCC100 thermostat, which is a popular...
Patch ASAP: Max-Critical Atlassian Bug Allows Unauthenticated RCE – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading 2 Min Read Source: Elena Uve via Alamy Stock Photo A max-critical unauthenticated remote code...
Africa, Middle East Lead Peers in Cybersecurity, but Lag Globally – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: SecurityScorecard Both Africa and the Middle East lead their economic peers in cybersecurity, but the regions fall...
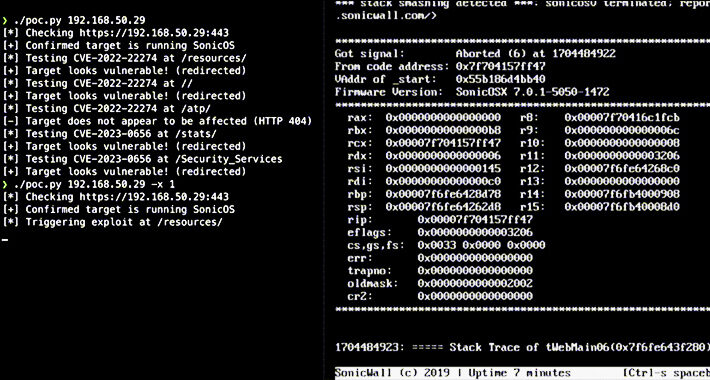
178K+ SonicWall Firewalls Vulnerable to DoS, RCE Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Igor Stevanovic via Alamy Stock Photo Two unauthenticated denial-of-service (DoS) vulnerabilities are threatening the security of SonicWall...
Getting Started: A Beginner’s Guide for Improving Privacy – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avoid The Hack! Welcome to the world of online/digital privacy! Like its sister guide for cybersecurity, this privacy guide was written for...
Alert: Over 178,000 SonicWall Firewalls Potentially Vulnerable to Exploits – Act Now – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 16, 2024NewsroomVulnerability / Network Security Over 178,000 SonicWall firewalls exposed over the internet are exploitable to at least one of...
Remcos RAT Spreading Through Adult Games in New Attack Wave – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 16, 2024NewsroomBotnet / Malware The remote access trojan (RAT) known as Remcos RAT has been found being propagated via webhards...
Case Study: The Cookie Privacy Monster in Big Global Retail – Source:thehackernews.com
Source: thehackernews.com – Author: . Explore how an advanced exposure management solution saved a major retail industry client from ending up on the naughty step due...
Inferno Malware Masqueraded as Coinbase, Drained $87 Million from 137,000 Victims – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 16, 2024NewsroomCryptocurrency / Cyber Threat The operators behind the now-defunct Inferno Drainer created more than 16,000 unique malicious domains over...
Hackers Weaponize Windows Flaw to Deploy Crypto-Siphoning Phemedrone Stealer – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 16, 2024NewsroomCryptocurrency / Windows Security Threat actors have been observed leveraging a now-patched security flaw in Microsoft Windows to deploy...
3 Ransomware Group Newcomers to Watch in 2024 – Source:thehackernews.com
Source: thehackernews.com – Author: . The ransomware industry surged in 2023 as it saw an alarming 55.5% increase in victims worldwide, reaching a staggering 4,368 cases....
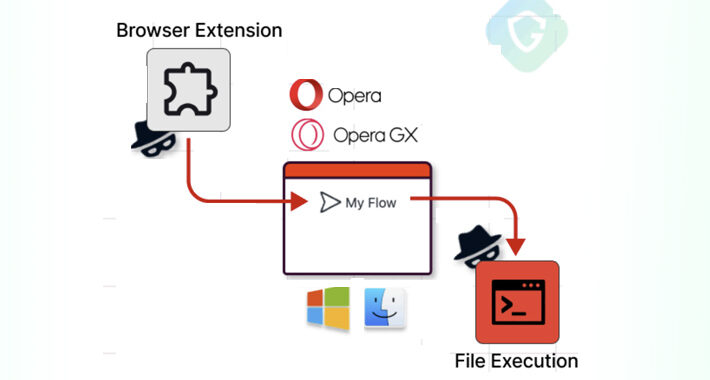
Opera MyFlaw Bug Could Let Hackers Run ANY File on Your Mac or Windows – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 15, 2024NewsroomVulnerability / Browser Security Cybersecurity researchers have disclosed a security flaw in the Opera web browser for Microsoft Windows...
Name That Toon: Cast Adrift – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist 1 Min Read Are these people coming or going? Is the Wi-Fi here any good? And where’s Wilson? Come...
High-Severity Flaws Uncovered in Bosch Thermostats and Smart Nutrunners – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 15, 2024NewsroomOperational Technology / Network Security Multiple security vulnerabilities have been disclosed in Bosch BCC100 thermostats and Rexroth NXA015S-36V-B smart...