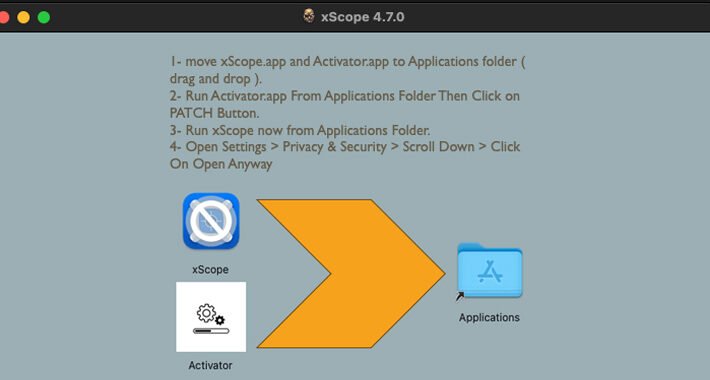
Source: thehackernews.com – Author: . Jan 23, 2024NewsroomMalware / Cryptocurrency Cracked software have been observed infecting Apple macOS users with a previously undocumented stealer malware capable...
Author: admin
From Megabits to Terabits: Gcore Radar Warns of a New Era of DDoS Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . As we enter 2024, Gcore has released its latest Gcore Radar report, a twice-annual publication in which the company releases internal...
BreachForums Founder Sentenced to 20 Years of Supervised Release, No Jail Time – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 23, 2024NewsroomCyber Crime / Dark Web Conor Brian Fitzpatrick has been sentenced to time served and 20 years of supervised...
~40,000 Attacks in 3 Days: Critical Confluence RCE Under Active Exploitation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 23, 2024NewsroomVulnerability / Cyber Attack Malicious actors have begun to actively exploit a recently disclosed critical security flaw impacting Atlassian...
Apple Issues Patch for Critical Zero-Day in iPhones, Macs – Update Now – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 23, 2024NewsroomVulnerability / Device Security Apple on Monday released security updates for iOS, iPadOS, macOS, tvOS, and Safari web browser...
Amy Farrow Joins Infoblox As Chief Information Officer – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SANTA CLARA, Calif., Jan. 22, 2024 /PRNewswire/ — Infoblox Inc., a leader in cloud networking and security services, today announces the appointment of Amy...
F5 Welcomes Samir Sherif As New Chief Information Security Officer – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SEATTLE – F5 (NASDAQ: FFIV), today announced the appointment of Samir Sherif as Senior Vice President and Chief Information Security...
National Cybersecurity Alliance Announces 2024 Data Privacy Week – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WASHINGTON (January 22, 2024) – Today, the National Cybersecurity Alliance (NCA), announced the program for its third annual Data Privacy Week campaign,...
Godzilla Web Shell Attacks Stomp on Critical Apache ActiveMQ Flaw – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Chris Willson via Alamy Stock Photo Threat actors have unleashed a fresh wave of cyberattacks targeting a...
Chinese Spies Exploited Critical VMware Bug for Nearly 2 Years – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: rafapress via Shutterstock One of the most serious VMware vulnerabilities in recent memory was secretly being exploited...
Microsoft Falls Victim to Russia-Backed ‘Midnight Blizzard’ Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 2 Min Read Source: Robert K. Chin – Storefronts via Alamy Stock Photo Microsoft’s corporate systems were...
North Korea’s ScarCruft Attackers Gear Up to Target Cybersecurity Pros – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Cavan Images via Alamy Stock Photo ScarCruft, the North Korea-sponsored advanced persistent threat (APT)...
German IT Consultant Fined Thousands for Reporting Security Failing – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Andriy Popov via Alamy Stock Photo After discovering and reporting a vulnerability...
How to Use Context-Based Authentication to Improve Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shelley Leveson, Director of Content Marketing, HYPR One of the biggest security weak points for organizations involves their authentication processes. According to...
Securing the Frontier: Preventing Account Takeovers with AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author Account takeover – also referred to as credential stuffing or account hijacking – involves cybercriminals...
North Korean Hackers Weaponize Fake Research to Deliver RokRAT Backdoor – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 22, 2024NewsroomCyber Attack / Hacking Media organizations and high-profile experts in North Korean affairs have been at the receiving end...
MavenGate Attack Could Let Hackers Hijack Java and Android via Abandoned Libraries – Source:thehackernews.com
Source: thehackernews.com – Author: . Several public and popular libraries abandoned but still used in Java and Android applications have been found susceptible to a new...
NS-STEALER Uses Discord Bots to Exfiltrate Your Secrets from Popular Browsers – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 22, 2024NewsroomBrowser Security / Cyber Threat Cybersecurity researchers have discovered a new Java-based “sophisticated” information stealer that uses a Discord...
52% of Serious Vulnerabilities We Find are Related to Windows 10 – Source:thehackernews.com
Source: thehackernews.com – Author: . We analyzed 2,5 million vulnerabilities we discovered in our customer’s assets. This is what we found. Digging into the data The...
FTC Bans InMarket for Selling Precise User Location Without Consent – Source:thehackernews.com
Source: thehackernews.com – Author: . The U.S. Federal Trade Commission (FTC) is continuing to clamp down on data brokers by prohibiting InMarket Media from selling or...
Apache ActiveMQ Flaw Exploited in New Godzilla Web Shell Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 22, 2024NewsroomVulnerability / Malware Cybersecurity researchers are warning of a “notable increase” in threat actor activity actively exploiting a now-patched...
AI Gives Defenders the Advantage in Enterprise Defense – Source: www.darkreading.com
Source: www.darkreading.com – Author: Source: Kaspars Grinvalds via Adobe Stock While using artificial intelligence (AI) for enterprise defense and against adversaries, who are also harnessing the...
Chinese Hackers Silently Weaponized VMware Zero-Day Flaw for 2 Years – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 20, 2024NewsroomZero Day / Cyber Espionage An advanced China-nexus cyber espionage group previously linked to the exploitation of security flaws...
CISA Issues Emergency Directive to Federal Agencies on Ivanti Zero-Day Exploits – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 20, 2024NewsroomNetwork Security / Threat Intelligence The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday issued an emergency directive...
Microsoft’s Top Execs’ Emails Breached in Sophisticated Russia-Linked APT Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 20, 2024NewsroomCyber Espionage / Emails Security Microsoft on Friday revealed that it was the target of a nation-state attack on...
Invoice Phishing Alert: TA866 Deploys WasabiSeed & Screenshotter Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . The threat actor tracked as TA866 has resurfaced after a nine-month hiatus with a new large-volume phishing campaign to deliver known...
Top 3 Priorities for CISOs in 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Source: Panther Media GmbH via Alamy Stock Photo As the new year begins, CISOs gather with their security...
Ransomware Actor Uses TeamViewer to Gain Initial Access to Networks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: monticello via Shutterstock TeamViewer is software that organizations have long used to enable remote support, collaboration, and...
Massive Data Breach at VF Hits 35M Vans, Retail Customers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Medicimage Education via Alamy Stock Photo Personal data belonging to 35.5 million customers of popular apparel brands...
Third Ivanti Vulnerability Exploited in the Wild, CISA Reports – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Elena11 via Shutterstock A critical vulnerability affecting Ivanti Endpoint Manager Mobile (EPMM),...