Source: thehackernews.com – Author: . Jan 31, 2024NewsroomVulnerability / Zero Day Ivanti is alerting of two new high-severity flaws in its Connect Secure and Policy Secure...
Author: admin
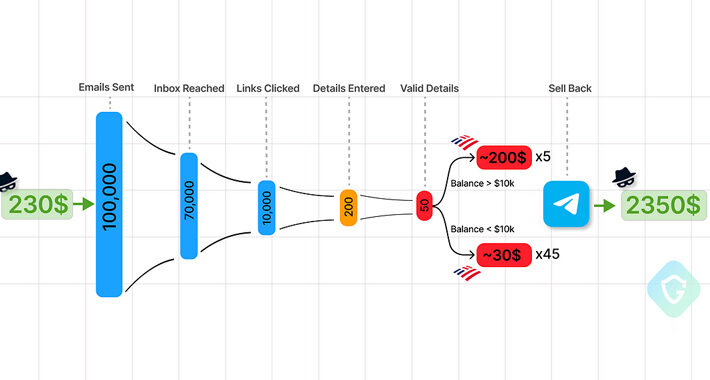
Telegram Marketplaces Fuel Phishing Attacks with Easy-to-Use Kits and Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 31, 2024NewsroomCyber Crime / Hacking News Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to...
Ivanti Zero-Day Patches Delayed as ‘KrustyLoader’ Attacks Mount – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading 2 Min Read Source: Peter Etchells via Alamy Stock Photo Attackers are using a pair...
‘Cactus’ Ransomware Strikes Schneider Electric – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Nate Hovee via Shutterstock Schneider Electric has fallen victim to a cyberattack affecting its Sustainability Business division,...
Forcepoint Federal Rebrands As Everfox to Reflect New Era of Defense-Grade Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE HERNDON, Va.–(BUSINESS WIRE)– Forcepoint Federal announced today that it has rebranded as Everfox to reflect its next chapter as a...
Cohesity Research Reveals Most Companies Pay Millions in Ransoms – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SAN JOSE, Calif. – January 30, 2024 – Research commissioned by Cohesity, a leader in AI-powered data security and management, reveals today’s...
Feds Reportedly Try to Disrupt ‘Volt Typhoon’ Attack Infrastructure – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer 3 Min Read Source: Weitwinkel via Shutterstock The US government, in collaboration with private sector stakeholders, has been...
Italian Businesses Hit by Weaponized USBs Spreading Cryptojacking Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 31, 2024NewsroomCryptocurrency / Cybersecurity A financially motivated threat actor known as UNC4990 is leveraging weaponized USB devices as an initial...
The SEC Won’t Let CISOs Be: Understanding New SaaS Cybersecurity Rules – Source:thehackernews.com
Source: thehackernews.com – Author: . The SEC isn’t giving SaaS a free pass. Applicable public companies, known as “registrants,” are now subject to cyber incident disclosure...
Hackers Exploiting Ivanti VPN Flaws to Deploy KrustyLoader Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 31, 2024NewsroomCyber Attack / Network Security A pair of recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) virtual private...
New Glibc Flaw Grants Attackers Root Access on Major Linux Distros – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 31, 2024NewsroomVulnerability / Endpoint Security Malicious local attackers can obtain full root access on Linux machines by taking advantage of...
Brazilian Feds Dismantle Grandoreiro Banking Trojan, Arresting Top Operatives – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 30, 2024NewsroomCyber Crime / Malware A Brazilian law enforcement operation has led to the arrest of several Brazilian operators in...
URGENT: Upgrade GitLab – Critical Workspace Creation Flaw Allows File Overwrite – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 30, 2024NewsroomDevSecOps / Vulnerability GitLab once again released fixes to address a critical security flaw in its Community Edition (CE)...
China-Linked Hackers Target Myanmar’s Top Ministries with Backdoor Blitz – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 30, 2024NewsroomMalware / Cyber Espionage The China-based threat actor known as Mustang Panda is suspected to have targeted Myanmar’s Ministry...
Q&A: How Israeli Cybersecurity Companies Endure Through the Conflict – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Source: Panther Media GmbH via Alamy Stock Photo Military forces in Israel have increased their numbers...
Top Security Posture Vulnerabilities Revealed – Source:thehackernews.com
Source: thehackernews.com – Author: . Each New Year introduces a new set of challenges and opportunities for strengthening our cybersecurity posture. It’s the nature of the...
Italian Data Protection Watchdog Accuses ChatGPT of Privacy Violations – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 30, 2024NewsroomGenerative AI / Data Privacy Italy’s data protection authority (DPA) has notified ChatGPT-maker OpenAI of supposedly violating privacy laws...
New ZLoader Malware Variant Surfaces with 64-bit Windows Compatibility – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 30, 2024NewsroomMalware / Cyber Threat Threat hunters have identified a new campaign that delivers the ZLoader malware, resurfacing nearly two...
Juniper Networks Releases Urgent Junos OS Updates for High-Severity Flaws – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 30, 2024NewsroomVulnerability / Network Security Juniper Networks has released out-of-band updates to address high-severity flaws in SRX Series and EX...
Protecting Business from the Inside Out: A Layered Approach to Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author In the ever-evolving world of cyber threats, protecting a business is akin to fortifying a...
Keenan & Associates Reports Data Breach Exposing Social Security Numbers of More Than 1.5M – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE MARLTON, N.J., Jan. 29, 2024 /PRNewswire/ — Approximately 1.5 million consumers are being notified that their Social Security numbers and other confidential information were compromised...
PoC Exploits Heighten Risks Around Critical New Jenkins Vuln – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: TippaPatt via Shutterstock Some 45,000 Internet-exposed Jenkins servers remain unpatched against a critical, recently disclosed arbitrary file-read...
SolarWinds Files Motion to Dismiss SEC Lawsuit – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 2 Min Read Source: Maurice Norbert via Alamy Stock Photo In a new filing with the US...
Iran’s ‘Cyber Centers’ Dodge Sanctions to Sell Cyber Operations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Gago Design via Shutterstock Public records combined with documents leaked by Iranian anti-government groups suggest that several...
New Jersey School District Shut Down by Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Sean Pavone via Alamy Stock Photo On Jan. 28, the Freehold Township...
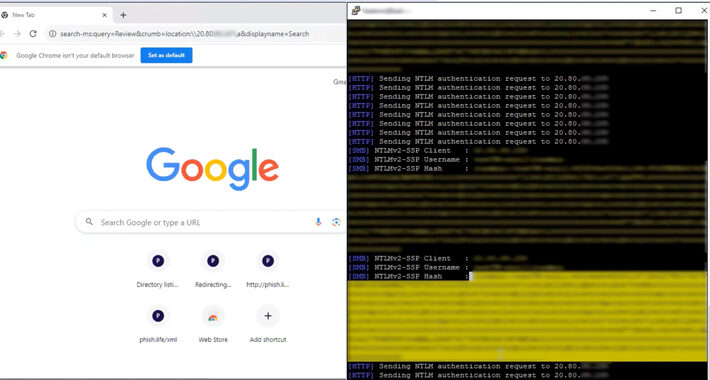
Researchers Uncover How Outlook Vulnerability Could Leak Your NTLM Passwords – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024NewsroomVulnerability / NTML Security A now-patched security flaw in Microsoft Outlook could be exploited by threat actors to access...
493 Companies Share Their SaaS Security Battles – Get Insights in this Webinar – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024The Hacker NewsSaaS Security / Webinar In today’s digital world, security risks are more prevalent than ever, especially when...
Albabat, Kasseika, Kuiper: New Ransomware Gangs Rise with Rust and Golang – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024NewsroomRansomware / Malware Cybersecurity researchers have detected in the wild yet another variant of the Phobos ransomware family known...
NSA Admits Secretly Buying Your Internet Browsing Data without Warrants – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024NewsroomSurveillance / Data Privacy The U.S. National Security Agency (NSA) has admitted to buying internet browsing records from data...
Malicious PyPI Packages Slip WhiteSnake InfoStealer Malware onto Windows Machines – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024NewsroomPyPI Repository / Malware Cybersecurity researchers have identified malicious packages on the open-source Python Package Index (PyPI) repository that...