Source: www.govinfosecurity.com – Author: 1 Breach Notification , HIPAA/HITECH , Security Operations Atlantic General Hospital Now Says Attack Compromised PHI of Nearly 137,000 Marianne Kolbasuk McGee...
Author:
24-Year-Old British Man Sentenced to 5 Years in Twitter Hack – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cryptocurrency Fraud , Fraud Management & Cybercrime , Social Media US Prosecutors Say He Ran SIM Swap Attack to Steal $794,000...
Generative AI, Cybersecurity Friend or Foe? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Shawn Surber Senior Director, Technical Account Management, Tanium Shawn Surber is Senior Director of Technical Account Management at Tanium. Over his...
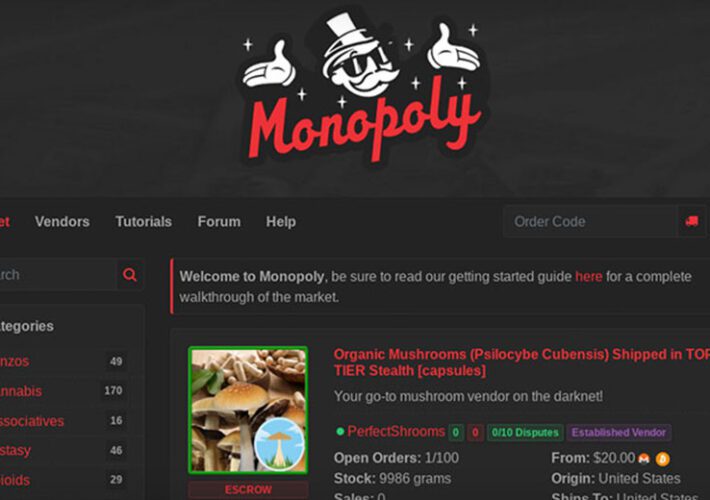
Monopoly Darknet Market: Suspected Operator Extradited to US – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 FBI: Market Facilitated $18 Million in Illegal Drug Transactions via Cryptocurrency Mathew J. Schwartz (euroinfosec) • June 26, 2023 ...
Irish Government Accused of Trying to Muzzle Privacy Critics – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy New Bill Set to Penalize Disclosure of Data Protection...
Monopoly Darknet Market: Suspected Operator Extradited to US – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 FBI: Market Facilitated $18 Million in Illegal Drug Transactions via Cryptocurrency Mathew J. Schwartz (euroinfosec) • June 26, 2023 ...
Companies Call for Changes to UK’s Cyber Essentials Scheme – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK government has responded to several concerns about its Cyber Essentials scheme, noting that just 35,000 organizations have been certified...
US Authorities Seize BreachForums Domain – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US government finally appears to have captured the surface web domains associated with notorious cybercrime marketplace BreachForums, despite the arrest...
Twitter Celeb Hacker Jailed For Five Years – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A Liverpool man has been handed a five-year jail term after a sophisticated hacking campaign in which he and others hijacked...
How Active Directory Bridging Extends Security Automation to Hybrid IT Environments – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 In today’s hybrid IT environments, it’s more important than ever to have a unified security strategy. With users and applications spread...
Millions of GitHub Repositories Vulnerable to Repo Jacking – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Application Security , DevSecOps Google, Lyft Among Vulnerable Repositories, Aqua Researchers Say Akshaya Asokan (asokan_akshaya) •...
Millions of GitHub Repositories Vulnerable to Repo Jacking – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Application Security , DevSecOps Google, Lyft Among Vulnerable Repositories, Aqua Researchers Say Akshaya Asokan (asokan_akshaya) •...
SEC Alleges SolarWinds CFO, CISO Violated US Securities Laws – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Governance & Risk Management , Standards, Regulations & Compliance Bart Kalsu, Tim Brown Could Face Monetary...
SEC Alleges SolarWinds CFO, CISO Violated US Securities Laws – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Governance & Risk Management , Standards, Regulations & Compliance Bart Kalsu, Tim Brown Could Face Monetary...
MDM: Balancing the Need for User Privacy, Corporate Control – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 In today’s hybrid work environment, mobile device management and security are more important than ever before. Apple has a reputation for...
LIVE Webinar | Resilience, Recovery and Contingency: Database Challenge Secrets – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Michael Fal Director, Database Solution Architecture, Rubrik Mike Fal (@mike_fal) is a specialist in data management technologies. As a community advocate,...
Hackers Targeting Linux and IoT Devices for Crytomining – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cryptocurrency Fraud , Cybercrime , Fraud Management & Cybercrime Attackers Deploy Trojanized OpenSSH Version for Device Takeover, Microsoft Says Mihir Bagwe...
SEO Poisoning Attacks on Healthcare Sector Rising, HHS Warns – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Account Takeover Fraud , Fraud Management & Cybercrime , Social Engineering Search Scams Luring Users to Malware-Infected Sites Are Often Tricky...
China Likely Also Sought IP In Barracuda Attacks: Researcher – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Security News Kyle Alspach June 23, 2023, 12:03 PM EDT It appears the hackers working for the Chinese government were ‘not...
US Military Personnel Warned of Malicious Smartwatches – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Service members across the US military have reported receiving smartwatches unsolicited in the mail. These smartwatches have Wi-Fi auto-connect capabilities and can...
OpenSSH Trojan Campaign Targets IoT and Linux Systems – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have discovered a sophisticated attack campaign that exploits custom and open-source tools to target Linux-based systems and Internet of...
USB Drives Used as Trojan Horses By Camaro Dragon – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 New versions of Chinese espionage malware have been observed spreading rapidly through infected USB drives. The malicious software tools were discovered...
MDM: Balancing the Need for User Privacy, Corporate Control – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 In today’s hybrid work environment, mobile device management and security are more important than ever before. Apple has a reputation for...
SEO Poisoning Attacks on Healthcare Sector Rising, HHS Warns – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Account Takeover Fraud , Fraud Management & Cybercrime , Social Engineering Search Scams Luring Users to Malware-Infected Sites Are Often Tricky...
LIVE Webinar | Resilience, Recovery and Contingency: Database Challenge Secrets – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Michael Fal Director, Database Solution Architecture, Rubrik Mike Fal (@mike_fal) is a specialist in data management technologies. As a community advocate,...
EU to Push Ahead With Data Act Despite Criticism – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy EU’s Industry Chief Says Europe’s ‘Assertion Is Not Protectionism’...
Hackers Targeting Linux and IoT Devices for Crytomining – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cryptocurrency Fraud , Cybercrime , Fraud Management & Cybercrime Attackers Deploy Trojanized OpenSSH Version for Device Takeover, Microsoft Says Mihir Bagwe...
#InfosecurityEurope: BlackBerry Cybersecurity President Warns Against Heavy-Handed AI Regulation – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The threats posed by the malicious use of generative AI tools, particularly large language model-based (LLM) chatbots, have pushed various governments...
NCSC Updates Cybersecurity Guidance for the Legal Sector – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK’s National Cyber Security Centre (NCSC) has released updated guidance to help law firms mitigate the latest cyber-threats. Worth an...
Manchester University Breach Victims Hit with Triple Extortion – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Staff and students at Manchester University have been sent threatening emails designed to put pressure on the institution to pay a...