Source: securityboulevard.com – Author: NSFOCUS
Overview
Recently, NSFOCUS CERT detected that Adobe issued a security announcement and fixed any file read vulnerability in Adobe ColdFusion (CVE-2024-53961). Due to improper restrictions on pathnames in Adobe ColdFusion, unauthenticated attackers can bypass the application’s restrictions to read files or directories outside of the restricted directory. As a result, sensitive information may be disclosed or system data may be manipulated. CVSS score is 7.4, and PoC exists at present. Relevant users are requested to take measures for protection as soon as possible.
Reference link: https://helpx.adobe.com/security/products/coldfusion/apsb24-107.html
Scope of Impact
Affected version
- Adobe ColdFusion 2021 <= Update 17
- Adobe ColdFusion 2023 <= Update 11
Unaffected version
- Adobe ColdFusion 2021 >= Update 18
- Adobe ColdFusion 2023 >= Update 12
Detection
Manual detection
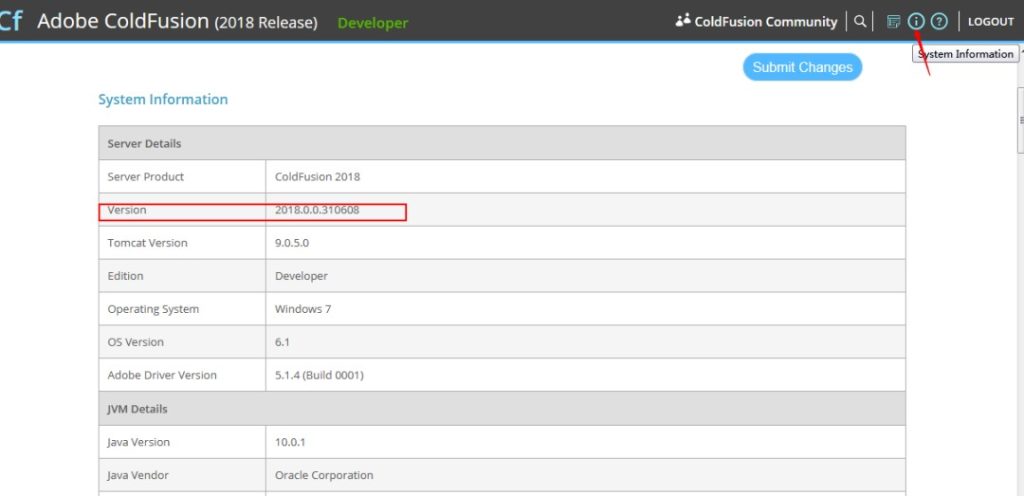
Relevant users can determine whether the current application is risky through version detection. Method I: After logging in to the system, visit /CFIDE/administrator/index.cfm and check the version in the system information.
Method II: In the bin directory of Adobe ColdFusion, run the cfinfo -version(info) command to view the version. If the current version is affected, there may be a security risk.
Mitigation
At present, a new version has been officially released to fix this vulnerability. Please upgrade the affected version as soon as possible for protection. Download link:
https://helpx.adobe.com/coldfusion/kb/coldfusion-2021-update-18.html
https://helpx.adobe.com/coldfusion/kb/coldfusion-2023-update-12.html
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, a pioneering leader in cybersecurity, is dedicated to safeguarding telecommunications, Internet service providers, hosting providers, and enterprises from sophisticated cyberattacks.
Founded in 2000, NSFOCUS operates globally with over 4000 employees at two headquarters in Beijing, China, and Santa Clara, CA, USA, and over 50 offices worldwide. It has a proven track record of protecting over 25% of the Fortune Global 500 companies, including four of the five largest banks and six of the world’s top ten telecommunications companies.
Leveraging technical prowess and innovation, NSFOCUS delivers a comprehensive suite of security solutions, including the Intelligent Security Operations Platform (ISOP) for modern SOC, DDoS Protection, Continuous Threat Exposure Management (CTEM) Service and Web Application and API Protection (WAAP). All the solutions and services are augmented by the Security Large Language Model (SecLLM), ML, patented algorithms and other cutting-edge research achievements developed by NSFOCUS.
The post Adobe ColdFusion Any File Read Vulnerability (CVE-2024-53961) appeared first on NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks..
*** This is a Security Bloggers Network syndicated blog from NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. authored by NSFOCUS. Read the original post at: https://nsfocusglobal.com/adobe-coldfusion-any-file-read-vulnerability-cve-2024-53961/
Original Post URL: https://securityboulevard.com/2024/12/adobe-coldfusion-any-file-read-vulnerability-cve-2024-53961/
Category & Tags: Security Bloggers Network,adobe,Adobe ColdFusion,Blog,CVE-2024-53961,Emergency Response – Security Bloggers Network,adobe,Adobe ColdFusion,Blog,CVE-2024-53961,Emergency Response
Views: 13




















































