Source: securityboulevard.com – Author: Assura Team Overview: Akamai researchers have identified a significant privilege escalation vulnerability in Windows Server 2025, termed “BadSuccessor.” This flaw exploits the...
Month: May 2025
Ensuring Stability with Robust NHI Strategies – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alison Mack Are Your Non-human Identities and Secrets Secure? The security of Non-Human Identities (NHIs) and their secretive credentials has proven to...
Feel Protected: Advances in NHI Security Techniques – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alison Mack How Relevant is NHI Security in Today’s Cloud-Dependent Society? It is becoming increasingly clear that the safe management of Non-Human...
Crypto Drainers are Targeting Cryptocurrency Users – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matthew Rosenquist As cryptocurrency becomes more popular and the adoption rises, we see a related increase in the number of cybercrimes, fraud,...
Emulating the Blazing DragonForce Ransomware – Source: securityboulevard.com
Source: securityboulevard.com – Author: Francis Guibernau DragonForce is a ransomware strain operated under the Ransomware-as-a-Service (RaaS) business model that emerged in August 2023. Originally identified as...
U.S. Authorities Seize DanaBot Malware Operation, Indict 16 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Law enforcement in the United States and Europe this week disrupted the infrastructure of the long-running DanaBot malware-as-a-service (MaaS) operation...
ColorTokens OT-in-a-Box: From Concept to Completion – Source: securityboulevard.com
Source: securityboulevard.com – Author: Venky Raju This year, we had a fantastic time meeting attendees, partners, friends, and customers at the RSA Conference Expo floor. You...
Malicious attack method on hosted ML models now targets PyPI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Karlo Zanki Artificial intelligence (AI) and machine learning (ML) are now inextricably linked to the software supply chain. ML models, which are...
BSidesLV24 – PasswordsCon – Passwords 101 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » BSidesLV24 – PasswordsCon – Passwords 101 by Marc Handelman on May...
From Alert to Action: Escape’s Jira Integration Explained – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alexandra Charikova Ticketing systems are an essential part of modern DevSecOps. They orchestrate cross-functional collaboration, ensure accountability, and drive issues to resolution....
IOC Query Generation for Microsoft Sentinel in Uncoder AI – Source: socprime.com
Source: socprime.com – Author: Steven Edwards How It Works 1. IOC Parsing from Threat Report Uncoder AI automatically identifies and extracts key observables from the threat...
IOC-to-Query Generation for Google SecOps (Chronicle) in Uncoder AI – Source: socprime.com
Source: socprime.com – Author: Steven Edwards How It Works 1. IOC Extraction from Threat Reports Uncoder AI automatically parses structured threat reports to extract: Domains and...
AI-Driven IOC Conversion for Palo Alto Cortex XSIAM Queries – Source: socprime.com
Source: socprime.com – Author: Steven Edwards How It Works Uncoder AI translates threat intelligence into Cortex XSIAM detection logic by ingesting structured IOCs and extracting relevant...
Signal Adds Screenshot-Blocker to Thwart ‘Windows Recall’ – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Signal on Friday shipped a new feature that automatically blocks all screenshots of its chat window, positioning it as a...
Akamai, Microsoft Disagree on Severity of Unpatched ‘BadSuccessor’ Flaw – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Akamai’s security team kicked off a new spat in the vulnerability disclosure world by publishing full exploitation details for “BadSuccessor,”...
Over 91% of companies sacrifice hybrid cloud security in the AI adoption rush – Source: www.csoonline.com
Source: www.csoonline.com – Author: New data shows that a surge in AI and hybrid cloud architectures is creating dangerous gaps, and security teams can’t keep up....
Beijing may have breached US government systems before Cityworks plugged a critical flaw – Source: www.csoonline.com
Source: www.csoonline.com – Author: Talos’ research revealed that Chinese hackers are actively exploiting the flaw to execute code and attempt persistence on vulnerable systems. A now-patched...
Cyberattacke auf Dienstgeräte des Landratsamt Bodenseekreis – Source: www.csoonline.com
Source: www.csoonline.com – Author: Derzeit sind 600 Handys und Tablets des Landratsamt Bodenseekreis lahmgelegt. Ursache ist ein Cyberangriff. Aufgrund einer Cyberattacke sind aktuell alle Diensthandys und...
Critical infrastructure under attack: Flaws becoming weapon of choice – Source: www.csoonline.com
Source: www.csoonline.com – Author: While phishing and stolen credentials remain frequent points of entry, overexposure and poor patch management of critical systems are increasingly fueling attackers’...
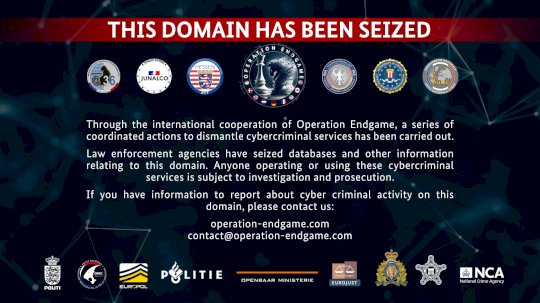
BKA gelingt Schlag gegen Cyberkriminelle – Source: www.csoonline.com
Source: www.csoonline.com – Author: Ermittler haben zahlreiche kriminellen Seiten abgeschaltet und Hintermänner identifiziert. Die Beschuldigten kommen überwiegend aus Russland. Im Rahen der “Operation Endgame” wurden die...
Heute startet der CIO Charity Run&Bike 2025 – Source: www.csoonline.com
Source: www.csoonline.com – Author: Ab heute bis zum 9. Juni 2025 läuft, radelt und rollt die CIO-Community für den guten Zweck. Der Erlös kommt Save the...
Russian APT28 compromised Western logistics and IT firms to track aid to Ukraine – Source: www.csoonline.com
Source: www.csoonline.com – Author: The Russian GRU-linked cyberespionage group APT28 has been targeting government agencies and companies from Western countries that were involved in the shipment...
Feds and Microsoft crush Lumma Stealer that stole millions of passwords – Source: www.csoonline.com
Source: www.csoonline.com – Author: Lumma Stealer operation hit 400,000 computers worldwide before coordinated takedown shut down Russian cybercrime kingpin. Microsoft and the US Department of Justice...
Samlify bug lets attackers bypass single sign-on – Source: www.csoonline.com
Source: www.csoonline.com – Author: The critical flaw can let an attacker authenticate as an admin with maximum system privileges. A critical vulnerability in the popular samlify...
Prompt injection flaws in GitLab Duo highlights risks in AI assistants – Source: www.csoonline.com
Source: www.csoonline.com – Author: Researchers managed to trick GitLab’s AI-powered coding assistant to display malicious content to users and leak private source code by injecting hidden...
Top 12 US cities for cybersecurity job and salary growth – Source: www.csoonline.com
Source: www.csoonline.com – Author: These dozen cities stand out as the most promising destinations for cybersecurity professionals due to their strong job growth, rising salaries, and...
Russische Cyber-Kampagne in Nato-Staaten aufgedeckt – Source: www.csoonline.com
Source: www.csoonline.com – Author: Eine Einheit des russischen GRU soll auch Ziele in Deutschland ins Visier genommen haben. Betroffen waren Technologie- und Logistikakteure, die an der...
3AM ransomware attack poses as a call from IT support to compromise networks – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley Cybercriminals are getting smarter. Not by developing new types of malware or exploiting zero-day vulnerabilities, but by simply pretending to...
3 Critical Pillars of Cyber-Resilience – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tiago Henriques Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been blocked? This...
How AI Is Transforming SASE, Zero Trust for Modern Enterprises – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Please enable cookies. Sorry, you have been blocked You are unable to access darkreading.com Why have I been...