Source: www.csoonline.com – Author: News 19 Nov 20245 mins Network SecurityVulnerabilitiesZero-day vulnerability Attackers are chaining two flaws in the wild to bypass authentication and escalate privileges...
Year: 2024
Twine Snags $12M for AI-Powered ‘Digital Employees’ Tech – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Twine, an Israeli security startup co-founded by Claroty veteran Benny Porat, emerged from stealth Wednesday with $12 million in seed...
Surf Security Adds Deepfake Detection Tool to Enterprise Browser – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs London-based startup Surf Security on Wednesday announced the launch of a deepfake detection tool that is integrated into its enterprise...
D-Link Warns of RCE Vulnerability in Legacy Routers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire D-Link this week issued an alert on a remote code execution (RCE) vulnerability affecting six router models that have been...
CISA Warns of Progress Kemp LoadMaster Vulnerability Exploitation – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs CISA this week warned organizations that it’s aware of attacks exploiting a vulnerability in Progress Software’s Kemp LoadMaster. The product,...
GitHub Launches Fund to Improve Open Source Project Security – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Code-hosting platform GitHub on Tuesday announced a new effort to improve the security and sustainability of open source projects through...
Cyera Raises $300 Million at $3 Billion Valuation – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Data security company Cyera announced on Wednesday that it has raised $300 million in a Series D funding round. The...
Oracle Patches Exploited Agile PLM Zero-Day – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Oracle this week announced patches for a high-severity information disclosure vulnerability in Agile Product Lifecycle Management (PLM) that has been...
Ford Says Blames Third-Party Supplier for Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Ford has completed an investigation launched after hackers claimed to have stolen customer information. Hackers named IntelBroker and EnergyWeaponUser claimed...
The AI Fix #25: Beware of the superintelligence, and a spam-eating AI super gran – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Skip to content In episode 25 of The AI Fix, humanity creates a satellite called Skynet and then loses it,...
US Agencies Urged to Combat Growing Chinese Cyberthreat – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Experts Call on Feds to Step Up Defense Against Escalating Chinese Threats Chris Riotta (@chrisriotta) • November 19, 2024 Image:...
Data Protection Startup Cyera Raises $300M on $3B Valuation – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Cloud Data Security & Resilience , Data Loss Prevention (DLP) , Endpoint Security Cyera’s Valuation Doubles Amid Expansion From DSPM to DLP,...
India Fines WhatsApp $25M, Bans Data Sharing for 5 Years – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Fraud Management & Cybercrime , Geo Focus: Asia , Geo-Specific Competition Regulator Says WhatsApp Users Could Not Opt Out of Data Sharing...
Oklahoma Hospital Says Ransomware Hack Hits 133,000 People – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Breach Notification , Fraud Management & Cybercrime , Healthcare Incident Is Among Growing List of Attacks on Small, Rural Hospitals Marianne Kolbasuk...
Mitigating the Risk of Cybercrime While Traveling Abroad – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Global tourism is reaching pre-pandemic records and many people are eager to embark on a new adventure. Yet at the...
Vishing, Wangiri, and Other VoIP Fraud Tactics On the Rise – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Corry Cummings VoIP fraud is a serious and growing threat to businesses, with attackers increasingly targeting cloud phone systems to exploit vulnerabilities...
Dell Unveils AI and Cybersecurity Solutions at Microsoft Ignite 2024 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Dell pulled the tarp off several new connected services during Microsoft Ignite, an annual conference hosted by Microsoft that is...
The 6 Best Free Antivirus Software Providers for Mac in 2024 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Nicole Rennolds Best overall: Bitdefender Best cleanup utility: Malwarebytes Best for free add-on features: Avira Best for detecting viruses in removable media:...
Microsoft Ignite 2024 Unveils Groundbreaking AI, Security, and Teams Innovations – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Microsoft Ignite 2024, held Nov. 19 – 22 in Chicago, featured nearly 100 announcements and software updates, including an AI...
US Agencies Urged to Combat Growing Chinese Cyberthreat – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Experts Call on Feds to Step Up Defense Against Escalating Chinese Threats Chris Riotta (@chrisriotta) • November 19, 2024 Image:...
India Fines WhatsApp $25M, Bans Data Sharing for 5 Years – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Fraud Management & Cybercrime , Geo Focus: Asia , Geo-Specific Competition Regulator Says WhatsApp Users Could Not Opt Out of Data Sharing...
Oklahoma Hospital Says Ransomware Hack Hits 133,000 People – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Breach Notification , Fraud Management & Cybercrime , Healthcare Incident Is Among Growing List of Attacks on Small, Rural Hospitals Marianne Kolbasuk...
UK CMA Clears Alphabet, Anthropic Partnership – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Google Does Not Have Material Influence Over Antrhtopic, Agency Says Akshaya...
This November, Celebrate National Scholarship Month With SWE’s Scholarship Recipients
Every November, National Scholarship Month applauds the accomplishments of scholarship recipients and the organizations that help them on their journey to turn their dreams to reality....
5-Star Fraud: The FTC’s Ban on Fake Reviews – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jesse Martin What Happened In August 2024, the United States Federal Trade Commission (FTC) took a decisive step in safeguarding consumer trust...
Imperva and the Secure by Design Pledge: A Commitment to Cybersecurity Excellence – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Wright The Cybersecurity and Infrastructure Security Agency (CISA) has introduced a voluntary “Secure by Design Pledge” for enterprise software manufacturers, focusing...
EPA IG Office: ‘High-Risk’ Security Flaws in Hundreds of Water Systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt More than 300 drinking water systems in the United States that serve almost 110 million people have security flaws –...
DEF CON 32 – Breaching AWS Through Shadow Resources – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Tuesday, November 19, 2024 Home » Security Bloggers Network » DEF CON 32 – Breaching AWS Through Shadow Resources Authors/Presenters:...
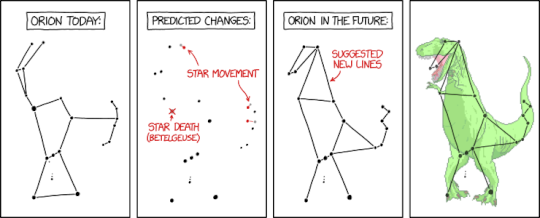
Randall Munroe’s XKCD ‘The Future of Orion’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
Unraveling Raspberry Robin’s Layers: Analyzing Obfuscation Techniques and Core Mechanisms – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nikolaos Pantazopoulos IntroductionDiscovered in 2021, Raspberry Robin (also known as Roshtyak) is a malicious downloader that has circulated in the wild for...