Source: www.bleepingcomputer.com – Author: Bill Toulas Museum software solutions provider Gallery Systems has disclosed that its ongoing IT outages were caused by a ransomware attack last...
Year: 2024
Xerox says subsidiary XBS U.S. breached after ransomware gang leaks data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The U.S. division of Xerox Business Solutions (XBS) has been compromised by hackers with a limited amount of personal information...
Google Groups is ending support for Usenet to combat spam – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Google has officially announced it’s ceasing support for Usenet groups on its Google Groups platform, a move partly attributed to...
Victoria court recordings exposed in reported ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Australia’s Court Services Victoria (CSV) is warning that video recordings of court hearings were exposed after suffering a reported Qilin...
The law enforcement operations targeting cybercrime in 2023 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams In 2023, we saw numerous law enforcement operations targeting cybercrime operations, including cryptocurrency scams, phishing attacks, credential theft, malware development,...
The biggest cybersecurity and cyberattack stories of 2023 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams 2023 was a big year for cybersecurity, with significant cyberattacks, data breaches, new threat groups emerging, and, of course, zero-day...
TikTok Editorial Analysis – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier TikTok seems to be skewing things in the interests of the Chinese Communist Party. (This is a serious analysis, and...
New SEC Cybersecurity Reporting Rules Take Effect – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tova Osofsky In July 2023 the US Security and Exchange Commission (SEC) issued new rules on “Cybersecurity Risk Management, Strategy, Governance, and...
USENIX Security ’23 – Cong Zhang, Yu Chen, Weiran Liu, Min Zhang, Dongdai Lin – ‘Linear Private Set Union From Multi-Query Reverse Private Membership Test’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
GKE Case Highlights Risks of Attackers Chaining Vulnerabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Palo Alto Network’s cybersecurity recently outlined two vulnerabilities it found in Google Kubernetes Engine (GKE) that, individually, don’t represent much...
Google Cloud Report Spotlights 2024 Cybersecurity Challenges – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard As the New Year dawns, a cybersecurity report from Google Cloud suggests that while there are many challenges ahead, it...
GUEST ESSAY: Leveraging DevSecOps to quell cyber risks in a teeming threat landscape – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Yuga Nugraha In today’s digital landscape, organizations face numerous challenges when it comes to mitigating cyber risks. The constant evolution...
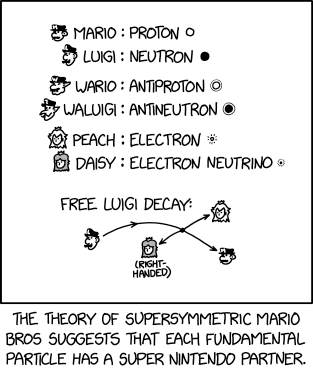
Randall Munroe’s XKCD ‘Supersymmetry’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
What is Security Posture? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire Security posture is a term often mentioned in cybersecurity, with businesses often told to improve or maintain a robust security...
Exploiting an API with Structured Format Injection – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dana Epp Never trust user input. It’s been the mantra for years in popular secure coding books. Yet, even today, we continue...
Google Whistles While OAuth Burns — ‘MultiLogin’ 0-Day is 70+ Days Old – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Infostealer scrotes having a field day with unpatched vulnerability. A zero-day vulnerability, publicly revealed in October, is still unpatched. Google’s...
Top 5 Cyber Predictions for 2024: A CISO Perspective – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepen Desai Amidst the ever-evolving realm of enterprise security, a new year unfolds, introducing a dynamic array of emerging threats. While the...
State AG Hits Hospital With $300K Fine for Web Tracker Use – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Healthcare , HIPAA/HITECH NewYork-Presbyterian Disabled Website, Patient Portal Trackers in 2022 Marianne Kolbasuk McGee (HealthInfoSec) •...
European Central Bank to Put Banks Through Cyber Stress Test – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Finance & Banking , Governance & Risk Management , Industry Specific 109 Banks to Participate in Simulated Cyberattacks to Assess Cyber...
Merry ‘Leaksmas’! Hackers Give Away 50 Million Pieces of PII – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Governance & Risk Management Holiday Leaks Could Result in More Digital Identity Theft and...
LockBit 3.0 Claims Attack on Australian Auto Dealer Eagers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Fraud Management & Cybercrime , Ransomware Eagers Says It Doesn’t Know Full Extent of Hack But Has Started...
Cybercriminals Share Millions of Stolen Records During Holiday Break – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Anucha Cheechang via Shutterstock Cybercriminals collectively leaked some 50 million records containing sensitive personal information in the...
Google Settles Lawsuit Over Tracking ‘Incognito Mode’ Chrome Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Tim Walton via Alamy Stock Photo Google is settling a class-action lawsuit over how it tracks data...
Cyberattackers Target Nuclear Waste Company via LinkedIn – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Alekesey Zotov via Alamy Stock Photo Last week, a group of hackers targeted Radioactive Waste Management (RWM), a...
Israel Battles Spike in Wartime Hacktivist, OT Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Source: Birgit Korber via Alamy Stock Photo For Israel, 2023 will be remembered as the beginning...
CISO Planning for 2024 May Struggle When It Comes to AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joan Goodchild, Contributing Writer Source: Robert Hyrons via Alamy Stock Photo Just about every CISO knows how this scenario goes: Called in...
Attackers Abuse Google OAuth Endpoint to Hijack User Sessions – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: imageBROKER via Alamy Stock Photo Attackers have been exploiting an undocumented Google OAuth endpoint to hijack user...
Startups Scramble to Build Immediate AI Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Paul Shomo Source: Andrii Yalanskyi via Alamy Stock Photo COMMENTARY At the start of 2003, nobody knew the industry would be handed...
10 Years After Yahoo Breach, What’s Changed? (Not Much) – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: PhotoEdit via Alamy Stock Photo In September 2016, Yahoo copped to a breach of 500 million user...
Over $80m in Crypto Stolen in Cyber-Attack on Orbit Chain – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Over $80m worth of cryptocurrency has been stolen following a cyber-attack on cross-chain bridge project Orbit Chain. The blockchain revealed the...