Source: socprime.com – Author: Oleh P. When a log record has keys like test.test, you can use two methods record_transformer and explode plugin, to process these...
Year: 2024
How to Increase index.max_regex_length in OpenSearch – Source: socprime.com
Source: socprime.com – Author: Oleksii K. WRITTEN BY Oleksii K. DevOps Engineer [post-views] December 16, 2024 · 2 min read The error index.max.regex_length in OpenSearch is related to...
Why AI Adoption Stalls: Data, Talent and Strategy Gaps – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Artificial Intelligence & Machine Learning , Recruitment & Reskilling Strategy , Training & Security Leadership Brett Barton of Unisys on Bridging the...
Short-Lived Certificates Coming to Let’s Encrypt – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Starting next year: Our longstanding offering won’t fundamentally change next year, but we are going to introduce a new offering...
Five years of the GitHub Bug Bounty program – Source:www.hackerone.com
Source: www.hackerone.com – Author: Katrina Dene. This blog was written by GitHub’s Engineering Team and originally published here. GitHub launched our Security Bug Bounty program in 2014,...
Dark web threats and dark market predictions for 2025 – Source: securelist.com
Source: securelist.com – Author: Alexander Zabrovsky, Sergey Lozhkin Review of last year’s predictions The number of services providing AV evasion for malware (cryptors) will increase We...
Future of proposed US cybersecurity healthcare bills in doubt – Source: www.csoonline.com
Source: www.csoonline.com – Author: News Analysis 16 Dec 20248 mins GovernmentHealthcare IndustrySecurity In the wake of ransomware attacks on healthcare providers, US legislators have introduced three...
Security leaders top 10 takeaways for 2024 – Source: www.csoonline.com
Source: www.csoonline.com – Author: CISOs share insights on lessons they have learned in 2024 about AI coding assistants, transparency with customers, deepfakes, third-party threats and more....
BlackBerry’s Critical Communications: The Triple Shield Available to Safeguard Organizations and Governments – Source: www.csoonline.com
Source: www.csoonline.com – Author: From major IT outages and cyberattacks crippling critical infrastructure, to extreme weather testing global resilience, organizations face a relentless barrage of security...
The Hidden Risks of Mobile Calls and Messages: Why End-to-End Encryption is Just the Starting Line – Source: www.csoonline.com
Source: www.csoonline.com – Author: The recent breaches of sovereign telecom networks in the United States, underscores how highly connected but fragmented public networks are increasingly vulnerable...
Cloud Access Security Broker – ein Kaufratgeber – Source: www.csoonline.com
Source: www.csoonline.com – Author: Bevor Sie in einen Cloud Access Security Broker investieren, sollten Sie diesen Artikel lesen. Lesen Sie, worauf es bei der Wahl eines...
Xiaomi Security Center Welcomes Security Research with HackerOne Partnership – Source:www.hackerone.com
Source: www.hackerone.com – Author: johnk. Please welcome the Xiaomi Security Center (MiSRC) to HackerOne! Xiaomi, one of the world’s largest consumer electronics manufacturers, is launching a...
Navigating HIPAA Compliance When Using Tracking Technologies on Websites – Source: securityboulevard.com
Source: securityboulevard.com – Author: mykola myroniuk Websites have become indispensable tools for healthcare organizations to connect with patients, streamline operations, and enhance service delivery. Modern websites...
Empower Your SOC Teams with Cloud-Native Security Solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Can Cloud-Native Security Be a Game-Changer for Your SOC Teams? In today’s complex digital landscape, organizations are increasingly challenged to...
Proactively Securing Machine Identities to Prevent Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why Should Proactive Security Management of Machine Identities Be a Priority? With the rise of digitalization across various sectors, organizations...
Empower Your Security with Cloud Compliance Innovations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn As we continue to leverage cloud services for our businesses, one cannot ignore the escalating complexity of cybersecurity. Non-Human Identities...
Build Your Confidence in Secrets Sprawl Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Can You Truly Be Confident in Your Approach to Secrets Management? Cybersecurity is a crucial element in today’s digital landscape,...
DEF CON 32 – Fireside Chat – The Dark Tangent and National Cyber Director Harry Coker, Jr – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » DEF CON 32 – Fireside Chat – The Dark Tangent and...
Product Updates and Enhancements – Source:www.hackerone.com
Source: www.hackerone.com – Author: johnk. Please find below a list of Feature updates/releases that happened in our first quarter! You can find more details about each...
Beyond Encryption: Advancing Data-in-Use Protection – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team In the ever-evolving landscape of cryptography, traditional encryption methods safeguarding data at rest and in transit remain foundational to cybersecurity...
Hacking Dropbox Live in the Heart of Singapore at h1-65 – Source:www.hackerone.com
Source: www.hackerone.com – Author: johnk. HackerOne’s first live hacking event in Southeast Asia, h1-65, kicked off during Black Hat Asia in Singapore! As one of the...
Upcoming Speaking Events – Source: www.schneier.com
Source: www.schneier.com – Author: B. Schneier HomeBlog Upcoming Speaking Events This is a current list of where and when I am scheduled to speak: I’m speaking...
Innovating with Secure Secrets Rotation Techniques – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn With the rapid expansion of digitized environments, the demand for effective and secure identity management has surged. Organizations are increasingly...
Proactive Approaches to Identity and Access Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is Proactive Security Crucial in IAM? Have you ever weighed the impact of security breaches and data leaks on...
Navigating Cloud Security for Future Proofing Your Assets – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is Cloud Security Imperative for Asset Protection? As businesses increasingly migrate their operations to the cloud, the demand for...
Gaining Confidence Through Effective Secrets Vaulting – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is Secrets Vaulting Crucial in Today’s Cybersecurity Landscape? In a world increasingly dependent on cloud-based services, how do organizations...
DEF CON 32 – MobileMesh RF Network Exploitation Getting the Tea from goTenna – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Saturday, December 14, 2024 Home » Security Bloggers Network » DEF CON 32 – MobileMesh RF Network Exploitation Getting the...
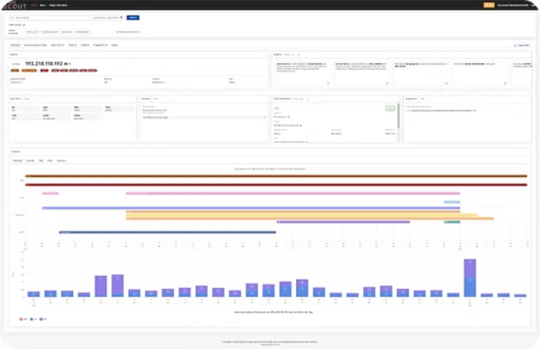
2024 Year in Review: Features and Improvements in Pure Signal™ Scout – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Monnier Team Cymru is excited to share our accomplishments in delivering new features and improvements in Pure Signal™ Scout. Thank you...
Feeling Reassured with Top-Tier API Security Measures – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are You Maximizing Your API Security Measures? If you’re a CISO or a cybersecurity professional, you understand the importance of...
How Can Strong Secrets Management Prevent Data Breaches – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Is Your Secrets Management Strong Enough to Prevent Data Breaches? In an increasingly connected digital world, secrets management has emerged...