Source: socprime.com – Author: Daryna Olyniychuk A novel iteration of the RomCom malware family emerges in the cyber threat arena. The new malware, dubbed SnipBot, uses...
Year: 2024
Vendor-Agnostic Cybersecurity: Adapting to the Future of Threat Detection – Source: socprime.com
Source: socprime.com – Author: Eugene Tkachenko In today’s fast-moving technological landscape, organizations face unprecedented challenges in managing their security operations. When both threats and technologies change...
NextGen Identity Management – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Federal agencies face a pivotal cybersecurity challenge: prevent unauthorized entities from accessing systems and facilities, while granting authorized federal employees...
Strengthening Security – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin Integrated Governance, Risk, and Compliance Is Critical Business executives in all sectors place a high premium on security in the quickly...
How AI-Driven Cybersecurity Offers Both Promise and Peril for Enterprises – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Artificial Intelligence (AI) is transforming multiple sectors, driving innovation and enhancing productivity and cybersecurity. The AI market is projected to...
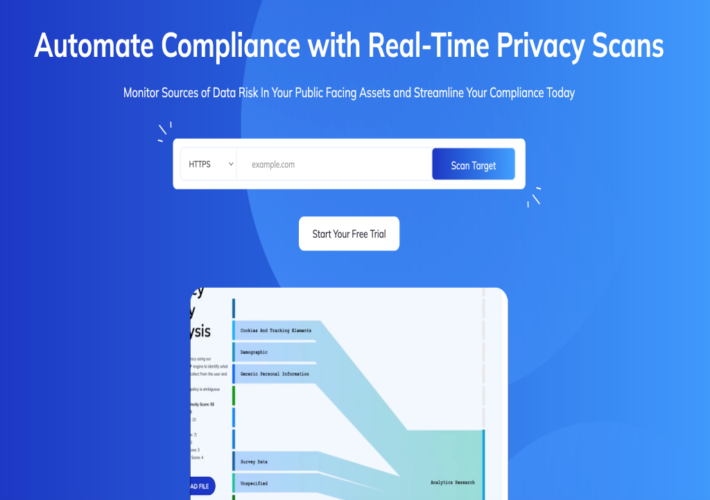
Innovator Spotlight: Zendata – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin In today’s digital landscape, data security and privacy have become top priorities for organizations of all sizes. According to a 2023...
Worried about Insider Risk? Pay More Attention to Offboarding – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Discussions of insider risk inevitably conjure images of disgruntled IT employees stealing sensitive data from the comfort of an air-conditioned...
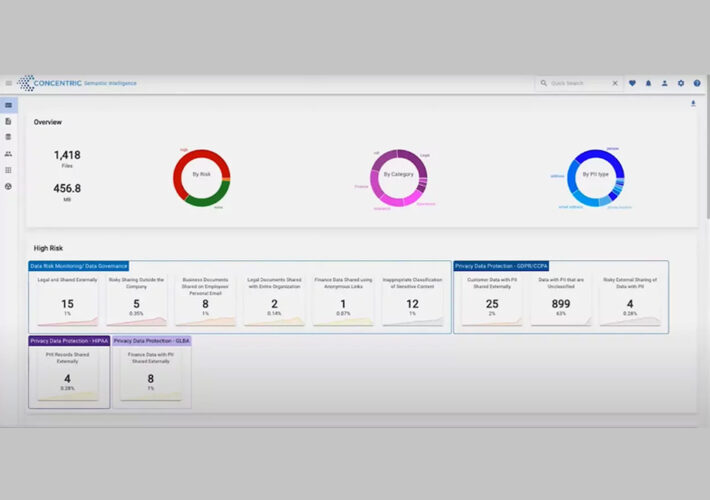
Innovator Spotlight: Concentric AI – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Nick It’s not enough for companies to just discover and monitor sensitive data. They need tools that can proactively fix any security...
Unmasking Shadow Apps to Secure Your SaaS Stack – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team It is a tale almost as old as time: users click download, install, and accept as they adopt new software...
How Automation Can Help Security Policy Optimization – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team One of the recurring questions we hear from network security leaders is “why aren’t our security policies optimized?” The answer,...
USENIX NSDI ’24 – Known Knowns and Unknowns: Near-Realtime Earth Observation Via Query Bifurcation In Serval – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Bill Tao, Om Chabra, Ishani Janveja, Indranil Gupta, Deepak Vasisht Our sincere thanks to USENIX, and the Presenters & Authors...
Transforming Cyber Risk Quantification and Vulnerability Prioritization with KnightVision – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ethan Bresnahan In today’s complex cyber landscape, managing risks effectively isn’t just about identifying threats—it’s about understanding their impact and knowing how...
Cost of Online Brand Impersonation: Customer Acquisition and Loyalty – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mitch Warren Online brand impersonation is an insidious threat compared to more straightforward attacks. Ransomware, for example, is simply extortion. A cybercriminal...
Generational security: The meaning behind this year’s Cyber Security Awareness Month theme – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ryan Healey-Ogden This year’s Cyber Security Awareness Month theme is “Generation Cyber Safe: Because online security knows no age”, but what does...
InCyber Forum Canada 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matthew Rosenquist The InCyber Forum Canada 2024 conference is an outstanding event, packed with multiple stages, many thought-leadership panels, and an expansive...
More on My AI and Democracy Book – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bruce Schneier In July, I wrote about my new book project on AI and democracy, to be published by MIT Press in...
USENIX NSDI ’24 – Democratizing Direct-to-Cell Low Earth Orbit Satellite Networks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Lixin Liu, Yuanjie Li, Hewu Li, Jiabo Yang, Wei Liu, Jingyi Lan, Yufeng Wang, Jiarui Li, Jianping Wu, Qian Wu,...
Identity Under Siege: Responding to the National Public Data Breach – Source: securityboulevard.com
Source: securityboulevard.com – Author: hmeyers Gary Perkins, Chief Information Security Officer, CISO Global October 11, 2024 While the scale of this data breach is alarming –...
Randall Munroe’s XKCD ‘Solar Protons’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
SDLC Methodologies: The 7 Most Common – Source: securityboulevard.com
Source: securityboulevard.com – Author: Legit Security The software development lifecycle (SDLC) looks different for every team, but standard methodologies have emerged and evolved to help teams...
Hackers Prowling For Unencrypted BIG-IP Cookies, Warns CISA – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Attack Surface Management , Network Firewalls, Network Access Control , Network Performance Monitoring & Diagnostics Agency Says Cookies Could Help Attackers...
Rhysida Leaks Nursing Home Data, Demands $1.5M From Axis – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Ransomware Gang Could Have Axis Health’s Mental Health, Drug Abuse Records Marianne...
ISMG Editors: Chinese Hackers Raise Stakes in Cyberespionage – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Video Also: AI Safety Bill Vetoed, Global Ransomware Response Guide Gets...
Regulating AI Catastophic Risk Isn’t Easy – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Legislation & Litigation , Next-Generation Technologies & Secure Development AI, Security Experts Discuss Who Defines...
Live Webinar | Maximizing Security Investments Part 2: Uncovering Hidden Budget and Optimizing Cybersecurity Spend – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Tim Grieveson Senior Vice President – Global Cyber Security Risk Advisor, Bitsight Tim Grieveson is Senior Vice President – Global Cyber...
European Council Adopts Cyber Resilience Act – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Internet of Things Security , Standards, Regulations & Compliance Act Imposes Mandatory Patching for IoT Devices Akshaya Asokan...
Operation Cronos Is Disrupting LockBit, Says UK Official – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Geo Focus: The United Kingdom , Geo-Specific Impact is “What We Would Have Hoped For, Says...
Relyance AI Raises $32M to Take on AI Governance Challenges – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development Thomvest Ventures Leads Series B...
SSA Struggling to Modernize Fraud Prevention Tech, GAO Warns – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Government , Identity Governance & Administration GAO: SSA Fails to Meet Industry and Federal Electronic Verification...
Webinar | Identity Crisis: How to Combat Session Hijacking and Credential Theft with MDR – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Erin Meyers Principal Product Marketing Manager, Huntress As Principal Product Marketing Manager at Huntress, Erin focuses on Managed Detection & Response...