Source: securityboulevard.com – Author: hmeyers December 19, 2024 The holiday season brings out the best in people, with many feeling inspired to support worthy causes. Unfortunately,...
Day: December 20, 2024
What Is Privilege Escalation? Types, Examples, and Prevention – Source: securityboulevard.com
Source: securityboulevard.com – Author: Legit Security Privilege escalation is a critical cybersecurity threat in which a user—usually a malicious actor—gains access to data beyond what their...
Detection as Code: Key Components, Tools, and More – Source: securityboulevard.com
Source: securityboulevard.com – Author: Legit Security As software development accelerates, the need to identify threats and respond in real time is greater than ever. Detection as...
Kubernetes Secrets: How to Create and Use Them – Source: securityboulevard.com
Source: securityboulevard.com – Author: Legit Security Kubernetes, also known as K8s, is a powerful platform for orchestrating containers in complex, distributed environments. Among its many features,...
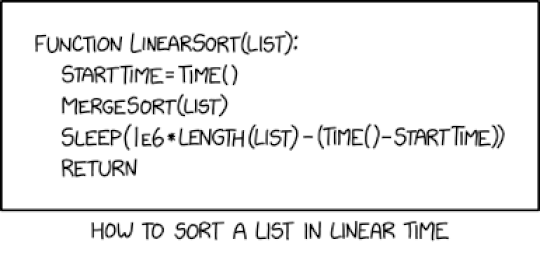
Randall Munroe’s XKCD ‘Linear Sort’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
CVE-2024-50379: A Critical Race Condition in Apache Tomcat – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lisa Haas Recently, an Apache Tomcat web server vulnerability, tracked as CVE-2024-50378, has been published, exposing the platform to remote code execution...
BadRAM-ifications: A Low-Cost Attack on Trusted Execution Environments – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland Recent research has uncovered a concerning vulnerability in modern Trusted Execution Environments (TEEs) that challenges fundamental assumptions about memory security....
Healthcare in the Cross Hairs: Cybercriminals Have Found Another High-Value Target – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bob Palmer Here at ColorTokens, we’ve recently been engaged with a leading cancer center to improve its cybersecurity posture. After phase one...