Source: www.databreachtoday.com – Author: Governance & Risk Management , Zero Trust Presented by Netskope 60 minutes Are you making decisions based on...
Day: December 12, 2024
Cybersecurity Gadgets to Hack Your Holiday Gift List – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Leadership & Executive Communication , Professional Certifications & Continuous Training , Training & Security Leadership Tech and Training Ideas to Help Cyber...
News alert: DMD Diamond invites developers to participate in open beta for its v4 blockchain – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cybernewswire Vienna, Austria, Dec. 11, 2024, CyberNewswire — DMD Diamond, one of the oldest blockchain projects in the space, has announced the...
Google Gemini 2.0 Introduced With Advanced AI for Developers – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Application Security , Next-Generation Technologies & Secure Development Multimodal Agentic AI Delivers Speed, Tools and Research Prototypes Michael Novinson (MichaelNovinson) • December...
Ransomware Hackers Exploiting Cleo Software Zero-Day – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Attack Surface Management , Governance & Risk Management , Patch Management Attackers Target Managed File Transfer Software Vulnerabilities Prajeet Nair (@prajeetspeaks) •...
AI Meets Fraud Prevention in LexisNexis-IDVerse Acquisition – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Artificial Intelligence & Machine Learning , Fraud Management & Cybercrime , Fraud Risk Management LexisNexis Combines AI-Driven Document Authentication With Its Fraud...
Clearinghouse Pays $250K Settlement in Web Exposure Breach – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Breach Notification , Governance & Risk Management , Healthcare Inmediata Health Group Has Paid $2.7M in Fines, Civil Claims for 2019 HIPAA...
Live Webinar | Exposing the Truth: How Government Agencies are Being Mislead by SASE Capabilities Disinformation – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Governance & Risk Management , Zero Trust Presented by Netskope 60 minutes Are you making decisions based on...
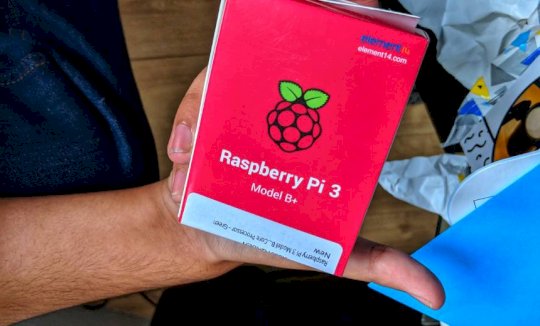
Cybersecurity Gadgets to Hack Your Holiday Gift List – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Leadership & Executive Communication , Professional Certifications & Continuous Training , Training & Security Leadership Tech and Training Ideas to Help Cyber...
Patch Tuesday: Microsoft Patches One Actively Exploited Vulnerability, Among Others – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse December brought a relatively mild Patch Tuesday, with one vulnerability having been actively exploited. Of all 70 vulnerabilities fixed, 16...
US Sanctions Chinese Cybersecurity Firm for 2020 Ransomware Attack – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson The U.S. has sanctioned Sichuan Silence, a Chinese cybersecurity firm involved in ransomware attacks targeting critical infrastructure in 2020. One...
Top Tech Conferences & Events to Add to Your Calendar in 2025 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Esther Shein A great way to stay current with the latest technology trends and innovations is by attending conferences. Read and bookmark...
CrowdStrike vs Wiz: Which Offers Better Cloud Security and Value? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
Best SIEM Tools of 2024: Top Solutions for Enhanced Security – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Drew Robb We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
Keeper Password Manager Review (2024): Features, Pros, & Cons – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares Keeper fast facts Our rating: 4.4 stars out of 5 Pricing: Starts at $2.92 per month Key features Discounts for...
Best CSPM Tools 2024: Top Cloud Security Solutions Compared – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Franklin Okeke We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
CrowdStrike vs Palo Alto 2024: Features, Pricing, and Insights – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
CrowdStrike vs Splunk: Which SIEM Solution Is Right for You? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
How HackerOne Fits into the Dev Tools You Know and Love – Source:www.hackerone.com
Source: www.hackerone.com – Author: johnk. Development teams are already under stress to innovate faster and in more areas, and that’s just to stay ahead of the...
2024 Year in Review: SWE’s Most Popular Content
As we bid 2024 goodbye, we compiled this roundup of our most popular podcast episodes, magazine articles, and blog posts from the year. Source Views: 0
AI: Overhyped or Essential for the Workforce? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maycie Belmore The rapid evolution of artificial intelligence (AI) is sending shockwaves through the cybersecurity landscape, and the workforce is feeling the...
Safe Handling of Data: Why Secrets Sprawl is a Risk – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn As cybersecurity continues to evolve at an unprecedented pace, businesses are increasingly becoming aware of the need to secure their...
Building Confidence with Strategic Secrets Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Can Strategic Secrets Management Boost Your Confidence? In today’s unpredictable cybersecurity landscape, building confidence in your protections may appear like...
DEF CON 32 – Digital Emblems-When Markings Are Required, But You Have No Rattle-Can – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 – Digital Emblems-When Markings Are Required, But You Have No Rattle-Can...
Websites and HIPAA: Navigating Online Tracking Technologies – Source: securityboulevard.com
Source: securityboulevard.com – Author: mykola myroniuk Today, healthcare providers, insurers, and other HIPAA-covered entities are increasingly relying on websites to share information, engage with patients, and...
How Should OT Companies Measure Cyber Risk? | ARIA Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: ARIA Cybersecurity Solutions The ARIA Cybersecurity team had a hugely productive week in Anaheim, California at the recent 2024 Rockwell Automation Fair....
Randall Munroe’s XKCD ‘Seismologists’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Permalink *** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored by Marc Handelman. Read the original post...
Flare Raises $30M Series B Led by Base 10 Partners to Continue Growth in Security Intelligence and Threat Exposure Management Markets – Source: securityboulevard.com
Source: securityboulevard.com – Author: Flare Today, we at Flare announced our USD $30M Series B Round led by Base10 Partners with participation from Inovia Capital, White...
Is crypto safe? What to know before investing in digital currencies – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ryan Healey-Ogden The digital currency market is booming, and as security professionals, we must address the crucial question: Is crypto safe? Following...
The Growing Threat of E-Skimming: Why March 2025’s PCI Deadline Matters – Source: securityboulevard.com
Source: securityboulevard.com – Author: Scott Fiesel by Source Defense The landscape of payment security is at a critical turning point. As we approach the March 31,...