Source: grahamcluley.com – Author: Graham Cluley Skip to content In episode 24 of The AI Fix, Mark makes an unforgivable error about the Terminator franchise, our...
Day: November 12, 2024
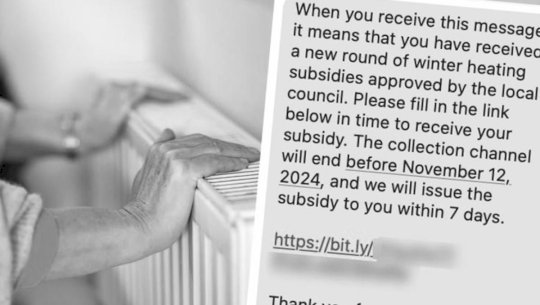
Winter Fuel Payment scam targets UK citizens via SMS – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley Scammers have leapt at the opportunity to exploit vulnerable UK residents by sending bogus messages telling them they need to...
Pentagon Secrets Leaker Jack Teixeira Sentenced to 15 Years in Prison by a Federal Judge – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press A federal judge on Tuesday sentenced a Massachusetts Air National Guard member to 15 years in prison after he pleaded...
Microsoft Confirms Zero-Day Exploitation of Task Scheduler Flaw – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Microsoft’s security response team on Tuesday pushed out fixes for at least 90 vulnerabilities across the Windows ecosystem and called...
Patch Tuesday: Critical Flaws in Adobe Commerce, Photoshop, InDesign, Illustrator – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Enterprise software maker Adobe on Tuesday rolled out fixes for a wide swathe of critical security flaws across product lines,...
GitLoker Strikes Again: New “Goissue” Tool Targets GitHub Developers and Corporate Supply Chains – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend An actor claiming membership in the Gitloker hacking group is offering a new GitHub phishing tool for sale or rent. ...
Ahold Delhaize Cybersecurity Incident Impacts Giant Food, Hannaford – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Several US pharmacies and supermarket chains owned by Dutch food giant Ahold Delhaize have been affected by a cybersecurity incident...
SAP Patches High-Severity Vulnerability in Web Dispatcher – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Enterprise software maker SAP on Tuesday announced the release of eight new and two updated security notes as part of...
Form I-9 Compliance Data Breach Impacts Over 190,000 People – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Employee eligibility verification solutions provider Form I-9 Compliance has suffered a data breach and its impact is far bigger than...
Millions of Hot Topic Customers Impacted by Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Roughly 57 million unique email addresses allegedly stolen from fashion retailer Hot Topic have been posted online, data breach notification...
Criminals Exploiting FBI Emergency Data Requests – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier I’ve been writing about the problem with lawful-access backdoors in encryption for decades now: that as soon as you create...
Malicious Python Package Exfiltrates AWS Credentials – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Security Operations Developers’ Credentials Stolen via Typosquatted ‘Fabric’ Library Prajeet Nair (@prajeetspeaks) • November 11, 2024 Image: Shutterstock A malicious...
How Global Threat Actors May Respond to a Second Trump Term – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Cybercrime , Fraud Management & Cybercrime , Government Experts Warn of Intensifying Global Cyber Threats During a Second Trump Presidency Chris Riotta...
Snyk Acquires Probely to Strengthen API Security for AI Apps – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Application Security , Application Security & Online Fraud , Fraud Management & Cybercrime Snyk Boosts API Security with Enhanced Dynamic App Security...
CHERI Alliance Adds to Memory Safety Hardware Coalition – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Endpoint Security , Hardware / Chip-level Security UK Government Agencies, Google Join Group that Promotes Akshaya Asokan (asokan_akshaya) • November 12, 2024...
The Power of the Purse: How to Ensure Security by Design – Source: www.darkreading.com
Source: www.darkreading.com – Author: Gary Barlet Gary Barlet, Public Sector Chief Technology Officer, Illumio November 12, 2024 5 Min Read Source: Zoonar GmbH via Alamy Stock...
Incident Response, Anomaly Detection Rank High on Planned ICS Security Spending – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jennifer Lawinski, Contributing Writer Source: SANS State of ICS/OT Cybersecurity 2024, Figure 18 In the “SANS 2024 State of ICS/OT Cybersecurity” report,...
Halliburton Remains Optimistic Amid $35M Data Breach Losses – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Todd Strand via Alamy Stock Photo Halliburton Company, a multinational corporation known for its oil and gas products...
Revamped Remcos RAT Deployed Against Microsoft Windows Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: imageBROKER.com GmbH & Co. KG via Alamy Stock Photo Threat actors have given the commercially...
What Listening to My Father Taught Me About Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joshua Goldfarb Source: Westend61 GmbH via Alamy Stock Photo COMMENTARYAs a teenager, I commented to my father that not everyone gives good...
The PANCCD™ Model: Strengthening Cyber Resiliency and Compliance – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Gary by Gary S. Miliefsky, CISSP, fmDHS I came up with this model to simplify cybersecurity, resiliency and regulatory compliance for executives...
SOC Prime Threat Bounty Digest — October 2024 Results – Source: socprime.com
Source: socprime.com – Author: Alla Yurchenko Threat Bounty Rules Releases Welcome to the October results edition of our traditional Threat Bounty Monlty digest. Last month, our...
Malicious Python Package Exfiltrates AWS Credentials – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Security Operations Developers’ Credentials Stolen via Typosquatted ‘Fabric’ Library Prajeet Nair (@prajeetspeaks) • November 11, 2024 Image: Shutterstock A malicious...
How Global Threat Actors May Respond to a Second Trump Term – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Cybercrime , Fraud Management & Cybercrime , Government Experts Warn of Intensifying Global Cyber Threats During a Second Trump Presidency Chris Riotta...
Snyk Acquires Probely to Strengthen API Security for AI Apps – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Application Security , Application Security & Online Fraud , Fraud Management & Cybercrime Snyk Boosts API Security with Enhanced Dynamic App Security...
Embargo Ransomware Gang Sets Deadline to Leak Hospital Data – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Fraud Management & Cybercrime , Governance & Risk Management , Healthcare Georgia-Based Memorial Hospital and Manor Among Embargo Group’s Latest Victims Marianne...
CISA’s VDP is going gangbusters but could still be improved – Source: www.csoonline.com
Source: www.csoonline.com – Author: Introduced in 2021, the US government’s vulnerability disclosure policy platform has racked up 12,000 bug reports and saved the government millions in...
BlackBerry Cylance customers should ‘explore options’ now that its immediate future is vague: Expert – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 11 Nov 20246 mins Endpoint ProtectionSecurity Software After the company said ‘all options are on the table,’ two experts say CISOs...
Schadenersatz nach Datendiebstahl bei Facebook? – Source: www.csoonline.com
Source: www.csoonline.com – Author: Begründet der Verlust der Kontrolle über Daten einen immateriellen Schaden und wie dieser zu bemessen? TY Lim – Shutterstock.com Nach einem Datendiebstahl...
Energy Giant Halliburton Reveals $35m Ransomware Loss – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Energy services supplier Halliburton has revealed that an August ransomware breach cost the firm $35m, highlighting the major financial impact of cyber-threats....