Source: www.databreachtoday.com – Author: Cybercrime , Fraud Management & Cybercrime Nordic Authorities Take Down Sipulitie, Dutch Police Arrest Alleged Bohemia Admins David Perera (@daveperera) • October...
Month: October 2024
Breach of Italian Prime Minister’s Bank Info Under Scrutiny – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Finance & Banking , Governance & Risk Management , Industry Specific Data Regulator Likely Reviewing Insider Threat Case at Intesa Sanpaolo Bank...
Netskope Purchases Dasera to Strengthen Cloud Data Security – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Cloud Security , Data Loss Prevention (DLP) , Endpoint Security Integration of DSPM Firm Dasera Enhances Data Protection Across Cloud Environments Michael...
Sri Lankan Police Arrest Over 200 Chinese Scammers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Fraud Management & Cybercrime , Fraud Risk Management , Geo Focus: Asia Chinese Cybercrime Groups Ran Operations in Rented Hotels and Guest...
Identity Security: How to Reduce Cyber Risk in Manufacturing – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Manufacturing enterprises have more identities than ever to manage – human and non – and face more attacks upon these identities. Manual...
Calling on CISOs and Security Leaders to Elevate IoT Security – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: CISO Trainings , Endpoint Security , Internet of Things Security Transforming Technical Expertise Into Strategic Leadership Sam Junkin • October 15, 2024...
Nation-State Cyber Threats: The Hidden War on Infrastructure – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Communication giants AT&T, Verizon, and Lumen were recently targeted by the hacking group Salt Typhoon in a sophisticated cyber attack against...
Simplifying NIS2 Compliance with Eclypsium – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland NIS2 is an EU cybersecurity directive that covers an incredibly broad set of services including but not limited to Energy,...
USENIX NSDI ’24 – Sprinter: Speeding Up High-Fidelity Crawling of the Modern Web – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Ayush Goel and Jingyuan Zhu, University of Michigan; Ravi Netravali, Harsha V. Madhyastha Our sincere thanks to USENIX, and the...
How CyberWinter Studios Empowers Warfighters with Automation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maycie Belmore How CyberWinter Studios Empowers the Warfighter with Automated Readiness Time is the Ultimate Currency, Automation Saves It For the military,...
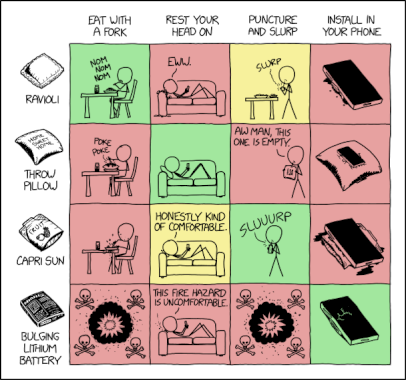
Randall Munroe’s XKCD ‘Ravioli-Shaped Objects’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
Vital Signs of Software Dependencies: Understanding Package Health – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lisa Haas As the vast majority of modern applications rely heavily on open-source software, dealing with updates for dependencies can become a...
Closing Security Gaps with AppOmni and Okta’s Integrated SaaS and Identity Protection – Source: securityboulevard.com
Source: securityboulevard.com – Author: Vivek Kumar, Sr. Director of Partner Alliances, AppOmni SaaS applications like Salesforce, Okta, and Microsoft 365 all generate security events in different...
Enhance Your Insider Risk Program with These 6 Systems Integrations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ontic Article Learn how the right integrations close critical data gaps, helping you gain a more complete view of your organization’s insider...
Navigating the Cybersecurity Risks of Shadow & Open-Source GenAI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire Generative AI is no doubt the leading frontier in AI. Models have captured attention and driven exciting use cases across...
SWE Diverse Podcast Ep 283: Latinas and Allies Working Together to Advance STEM Representation
Learn how to become a stronger ally to the Latina community in STEM in this conversation with the SWE Latinos Affinity Group on Diverse: a SWE...
Now Available — “The Heart of Science: Engineering Blueprint,” a New Book by Jayshree Seth, Ph.D.
The Society of Women Engineers (SWE) and nationally known author and scientist Jayshree Seth, Ph.D., have teamed up on a new book that provides an immersive...
Cybercriminals Are Increasingly Helping Russia and China Target the US and Allies, Microsoft Says – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Russia, China and Iran are increasingly relying on criminal networks to lead cyberespionage and hacking operations against adversaries like the...
Election Day is Close, the Threat of Cyber Disruption is Real – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Cybercriminals, hacktivists and nation-state actors have all been active in 2024 either threatening to disrupt or simply taking advantage of...
GitHub Patches Critical Vulnerability in Enterprise Server – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Code hosting platform GitHub has released patches for a critical-severity vulnerability in GitHub Enterprise Server that could lead to unauthorized...
Volkswagen Says IT Infrastructure Not Affected After Ransomware Gang Claims Data Theft – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The Volkswagen Group has issued a statement after a known ransomware group claimed to have stolen valuable information from the...
CISO Conversations: Julien Soriano (Box) and Chris Peake (Smartsheet) – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Julien Soriano and Chris Peake are CISOs for primary collaboration tools: Box and Smartsheet. As always in this series, we...
Splunk Enterprise Update Patches Remote Code Execution Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Splunk on Monday announced fixes for 11 vulnerabilities in Splunk Enterprise, two of which are high-severity bugs leading to remote...
Organizations Slow to Protect Doors Against Hackers: Researcher – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A significant percentage of organizations whose door access controllers have been analyzed by a cybersecurity researcher have failed to take...
Critical Vulnerability Patched in 101 Releases of WordPress Plugin Jetpack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Automattic on Monday announced patches for 101 versions of the popular WordPress security plugin Jetpack, to resolve a critical-severity vulnerability...
Open Source Package Entry Points May Lead to Supply Chain Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Entry points in open source packages across multiple programming languages can be abused for code execution, leading to supply chain...
New CounterSEVeillance and TDXDown Attacks Target AMD and Intel TEEs – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Security researchers continue to find ways to attack Intel and AMD processors, and the chip giants over the past week...
CSO – neuer Web-Auftritt, noch bessere Information – Source: www.csoonline.com
Source: www.csoonline.com – Author: Wir haben unser Security-Portal modernisiert. Die CSO wird Sie künftig noch besser über alle relevanten Sicherheitsaspekte informieren können. Probieren Sie die neue...
Why are we still confused about cloud security? – Source: www.infoworld.com
Source: www.infoworld.com – Author: analysis Oct 15, 20245 mins Cloud ComputingCloud SecurityIdentity and Access Management We’re building too much complexity and are ill-trained to secure it....
Alleged Cisco data breach could affect Microsoft, Barclays, and SAP developer data – Source: www.csoonline.com
Source: www.csoonline.com – Author: A BreachForum post made by IntelBroker claims source code was taken from these Cisco customers in the breach. Notorious hacker “IntelBroker” is...