Source: www.darkreading.com – Author: PRESS RELEASE October 17, 2024: OpenAI is projected to generate over $10 billion in revenue next year, a clear sign that the adoption...
Day: October 17, 2024
Illinois Joins CoSN’s Trusted Learning Environment (TLE) State Partnership Program for Student Data Privacy – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WASHINGTON, DC (October 15, 2024) – The Consortium for School Networking (CoSN) today announced that the Illinois Learning Technology Center (LTC),...
Swift to Launch AI-Powered Fraud Defence to Enhance Cross-Border Payments – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Brussels, 16 October 2024 – Swift today announced that it is rolling out new AI-enhanced fraud detection to help the...
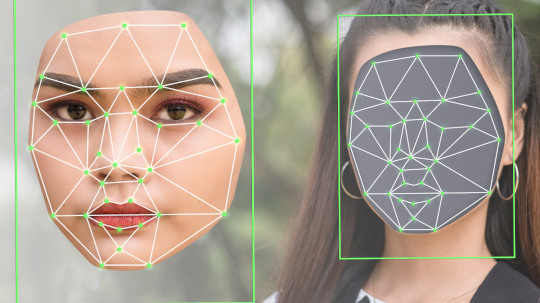
Hong Kong Crime Ring Swindles Victims Out of $46M – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Mike via Adobe Stock Hong Kong police arrested 27 people Monday for their involvement in a deepfake scam...
Internet Archive Slowly Revives After DDoS Barrage – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: Postmodern Studio via Alamy Stock Photo The Internet Archive, a nonprofit digital library website, is...
4 Ways to Address Zero-Days in AI/ML Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan McInerney Dan McInerney, Lead AI Threat Researcher, Protect AI October 17, 2024 3 Min Read Source: Blackboard via Alamy Stock Photo...
Anonymous Sudan Unmasked as Leaders Face Life in Prison – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Firoze Edassery via Alamy Stock Photo A federal grand jury has indicted two Sudanese nationals for their...
Is a CPO Still a CPO? The Evolving Role of Privacy Leadership – Source: www.darkreading.com
Source: www.darkreading.com – Author: Arlo Gilbert Source: imageBROKER.com GmbH & Co. KG via Alamy Stock Photo COMMENTARY The role of the CPO — chief privacy officer...
What You Need to Know for WE24
Learn more about how to prepare for WE24, SWE’s annual conference. Views: 3
Lockheed Martin: A Supportive Workplace for Women
Discover the stories of three women who re-entered the workforce after a career break through Lockheed Martin’s returnship program, Chapter Next. Views: 2
Sudanese Brothers Arrested in ‘AnonSudan’ Takedown – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs The U.S. government on Wednesday announced the arrest and charging of two Sudanese brothers accused of running Anonymous Sudan (a.k.a. AnonSudan),...
A glimmer of good news on the ransomware front, as encryption rates plummet – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley No-one would be bold enough to say that the ransomware problem is receding, but a newly-published report by Microsoft does...
Smashing Security podcast #389: WordPress vs WP Engine, and the Internet Archive is down – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Skip to content WordPress’s emperor, Matt Mullenweg, demands a hefty tribute from WP Engine, and a battle erupts, leaving millions...
Hackers breach Pokémon game developer, source code and personal information leaks online – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley In what appears to be one of the biggest leaks in Pokémon history, troves of information related to multiple incarnations...
Be Aware of These Eight Underrated Phishing Techniques – Source: www.securityweek.com
Source: www.securityweek.com – Author: Stu Sjouwerman Email phishing is by far one of the most prevalent forms of phishing. However, there are a number of lesser-known...
CISA, FBI Seek Public Comment on Software Security Bad Practices Guidance – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US cybersecurity agency CISA and the FBI have released new guidance on security bad practices for software manufacturers and...
F5 BIG-IP Updates Patch High-Severity Elevation of Privilege Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire F5 on Wednesday published its October 2024 quarterly security notification, describing two vulnerabilities addressed in BIG-IP and BIG-IQ enterprise products....
Cisco Patches High-Severity Vulnerabilities in Analog Telephone Adapters – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Cisco on Wednesday announced patches for eight vulnerabilities in the firmware of ATA 190 series analog telephone adapters, including two...
Iranian Hackers Use Brute Force in Critical Infrastructure Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Iranian state-sponsored threat actors have been using brute force and other techniques in attacks targeting critical infrastructure organizations, government agencies...
Brazilian Police Arrest Notorious Hacker USDoD – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Brazil’s Federal Police on Wednesday announced the arrest of a hacker whose description matches that of the notorious leaker known...
Anonymous Sudan DDoS Service Disrupted, Members Charged by US – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US Justice Department on Wednesday announced charges against two Sudanese nationals over their alleged roles in the DDoS attacks...
SAS CTF and the many ways to persist a kernel shellcode on Windows 7 – Source: securelist.com
Source: securelist.com – Author: Igor Kuznetsov, Boris Larin SAS SAS 17 Oct 2024 minute read On May 18, 2024, Kaspersky’s Global Research & Analysis Team (GReAT),...
Die 6 größten Cyberbedrohungen im Gesundheitswesen – Source: www.csoonline.com
Source: www.csoonline.com – Author: Gesundheitsorganisationen geraten immer häufiger in den Fokus von Cyberkriminellen. Das sind die größten Risiken. Organisationen im Gesundheitswesen müssen damit rechnen, dass Ransomware,...
Critical SolarWinds flaw finds exploitations in the wild despite available fixes – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 17 Oct 20243 mins SecurityVulnerabilities CISA has added the hardcoded credentials vulnerability to its known exploited vulnerabilities (KEV) catalog. A security...
Chinese cybersecurity association urges review of Intel products – Source: www.computerworld.com
Source: www.computerworld.com – Author: This could lead to further scrutiny by the Cyberspace Administration of China (CAC), the country’s cyber regulatory body. The Cybersecurity Association of...
How AI is becoming a powerful tool for offensive cybersecurity practitioners – Source: www.csoonline.com
Source: www.csoonline.com – Author: From vulnerability assessments to penetration testing, AI and large language models are profoundly changing the fundamentals of offsec. Artificial intelligence, especially large...
Attackers repurpose EDRSilencer to evade detection – Source: www.csoonline.com
Source: www.csoonline.com – Author: News Analysis 16 Oct 20244 mins Endpoint ProtectionMalwareNetwork Security Red team tool EDRSilencer has been used by hackers to make the Windows...
Fortinet Edge Devices Under Attack – Again – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Governance & Risk Management , Patch Management , Vulnerability Assessment & Penetration Testing (VA/PT) Hackers May Have Reverse-Engineered February Patch David Perera...
UK Reports 50% Spike in ‘Nationally Significant’ Incidents – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Cybercrime , Fraud Management & Cybercrime , Geo Focus: The United Kingdom New NCSC Chief Also Warns of Threefold Increase in Severe...
AI Powers Cyera’s $162M Buy of Data Security Startup Trail – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Data Loss Prevention (DLP) , Endpoint Security Trail Acquisition Brings Enhanced DLP, DSPM Integration, Safeguards Data in Motion Michael Novinson (MichaelNovinson) •...