Alyssa Frechette, a continuous improvement manager who has achieved several promotions and several lateral moves over the last seven years, shares insights on how she has...
Day: October 14, 2024
SWE Diverse Podcast Ep 280: Engaging Youth STEM Voters With Jennifer McAndrew of Tufts University
Explore how to boost voting turnout and civic participation among STEM students in this episode of Diverse: a SWE podcast! Views: 0
Back-to-School Activities for SWENext Clubs
SWENext Influencer Zeynep S. shares the activities, guest speakers, and competitions planned for her SWENext Club this year. Views: 0
How a Reinvention Mindset Can Turn Setbacks Into Growth
SWE member Lori McDowell reflects on the mindset shifts that helped her bounce back and thrive after a difficult situation in her STEM career. Views: 0
Safety, Respect, and Inclusion: Our Stance Against Harassment at the WE24 Annual Conference & Career Fair
The SWE Annual Conference & Career Fair is a place where women, nonbinary individuals, and men as allies of all backgrounds can support the overall persistence...
ConfusedPilot: UT Austin & Symmetry Systems Uncover Novel Attack on RAG-based AI Systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: Claude Mandy Executive Summary Researchers at the Spark Research Lab (University of Texas at Austin)1, under the supervision of Symmetry CEO Professor...
USENIX NSDI ’24 – Spectrumize: Spectrum-Efficient Satellite Networks for the Internet of Things – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Vaibhav Singh, Tusher Chakraborty, Suraj Jog, Om Chabra, Deepak Vasisht, Ranveer Chandra Our sincere thanks to USENIX, and the Presenters...
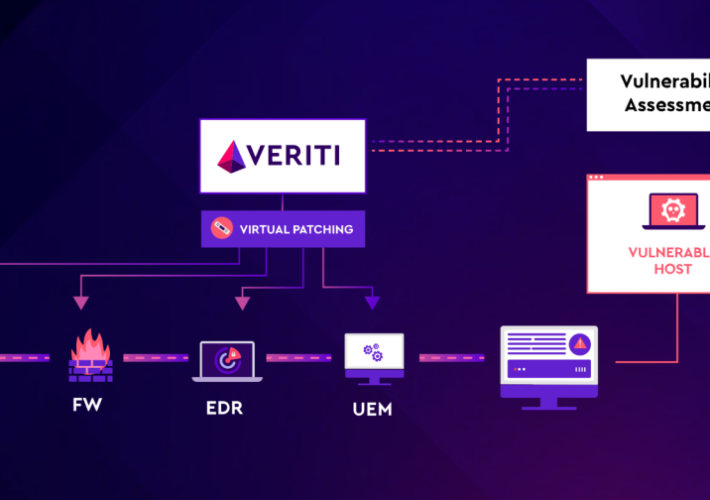
Patch-22: The Catch of Waiting to Fix Cybersecurity Vulnerabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Greenberg One of the biggest dilemmas for security teams is when to patch vulnerabilities. This is a classic “Patch-22” situation—patching immediately...
Misinformation, Online Scams Surging Following Historic Hurricanes – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity Bad actors often take advantage of natural disasters, and especially hurricanes, in times of crisis. Hurricanes Helene and Milton...