Source: www.databreachtoday.com – Author: Latest Fraud Management & Cybercrime Rhysida Leaks Nursing Home Data, Demands $1.5M From Axis Marianne Kolbasuk McGee • October 11, 2024 Ransomware...
Day: October 14, 2024
Accounting of Disclosures Under the HITECH Act – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Latest Fraud Management & Cybercrime Rhysida Leaks Nursing Home Data, Demands $1.5M From Axis Marianne Kolbasuk McGee • October 11, 2024 Ransomware...
ENISA: Software vulnerability prevention initiatives – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: Latest Fraud Management & Cybercrime Rhysida Leaks Nursing Home Data, Demands $1.5M From Axis Marianne Kolbasuk McGee • October 11, 2024 Ransomware...
Whispers from the Dark Web Cave. Cyberthreats in the Middle East – Source: securelist.com
Source: securelist.com – Author: Vera Kholopova, Kaspersky Security Services SOC, TI and IR posts SOC, TI and IR posts 14 Oct 2024 minute read The Kaspersky...
Australia Intros Its First National Cyber Legislation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: David Coleman | Have Camera Will Travel via Alamy Stock Photo Australia introduced a new cybersecurity law into...
Mamba 2FA Cybercrime Kit Targets Microsoft 365 Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Matthijs Kuijpers via Alamy Stock Photo A phishing-as-a-service (PhaaS) kit dubbed Mamba 2FA is...
3 More Ivanti Cloud Vulns Exploited in the Wild – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Skorzewiak via Alamy Stock Photo In the latest wrinkle of what seems to be an ongoing saga of...
Risk Strategies Drawn From the EU AI Act – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kyle McLaughlin Source: Vitor Miranda via Alamy Stock Photo COMMENTARY As artificial intelligence (AI) becomes increasingly prevalent in business operations, organizations must...
Cloud, AI Talent Gaps Plague Cybersecurity Teams – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading A major skills gap exists for security teams when it comes to artificial intelligence (AI) and...
AI-Augmented Email Analysis Spots Latest Scams, Bad Content – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Peshkova via Shutterstock Artificial intelligence (AI) models that work across different types of media and domains —...
Building Cyber Resilience in SMBs With Limited Resources – Source: www.darkreading.com
Source: www.darkreading.com – Author: Mark Logan Source: Josie Elias via Alamy Stock Photo COMMENTARY Small and medium-sized businesses (SMBs) increasingly have become prime targets for cybercriminals....
Microsoft: Creative Abuse of Cloud Files Bolsters BEC Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: JLStock via Shutterstock Threat actors are upping the ante on business email compromise (BEC) campaigns by combining...
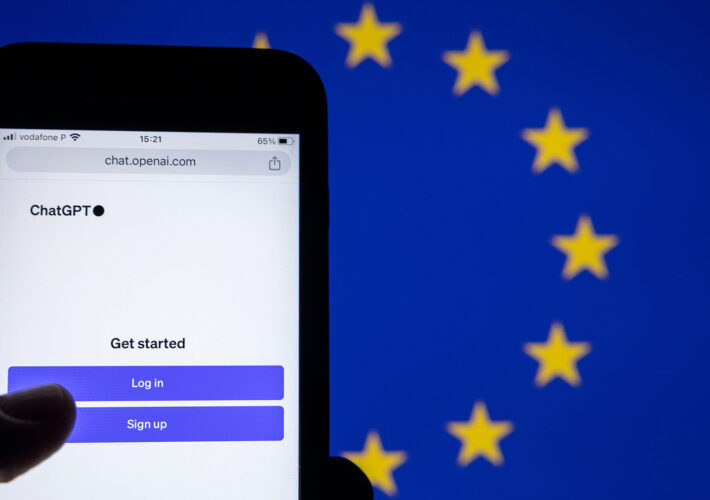
Despite Prevalence of Online Threats, Users Aren’t Changing Behavior – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jennifer Lawinski, Contributing Writer Source: Consumer Cyber Readiness Report, Consumer Reports Consumers are aware that their information can be stolen by cybercriminals...
Ex-Uber CISO Requests a New, ‘Fair’ Trial – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: Tetra Images via Alamy Stock Photo Former Uber CISO Joseph Sullivan, convicted in 2023 of...
5 Zero-Days in Microsoft’s October Update to Patch Immediately – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: fadfebrian via Shutterstock Microsoft’s October security update addressed a substantial 117 vulnerabilities, including two actively exploited flaws...
SWE Mentoring Committee: Reflections on a Year of Firsts
To honor the first anniversary of the SWE Mentoring Committee’s formation, Mandeep Gill (she/her) discusses her journey on the committee and the impact its members have...
Rising Together: Celebrating the 2024 SWE Recognition Recipients
Find the full list of the 2024 Society of Women Engineers recognition recipients who are developing new technologies and advancing the role of women in engineering....
Inspiring the Next Generation: Latinas in Engineering Outreach Programs
As part of their spotlight month, the Latinos AG celebrates Hispanic Heritage Month by reviewing resources available for Latina engineers. Views: 2
Exploring SWE Affinity Groups: SWE Athletes
Each month, we spotlight a SWE Affinity Group. This month, we are excited to highlight the SWE Athletes Affinity Group. Views: 1
Hispanic Heritage Month: Celebrating Women Trailblazers in STEM
SWENext Influencer Isabella T. highlights Hispanic women in STEM who are spearheading technological advances, breaking barriers, and inspiring the next generation. Views: 1
Six Steps to Enhance Early Career Success
Alyssa Frechette, a continuous improvement manager who has achieved several promotions and several lateral moves over the last seven years, shares insights on how she has...
SWE Diverse Podcast Ep 280: Engaging Youth STEM Voters With Jennifer McAndrew of Tufts University
Explore how to boost voting turnout and civic participation among STEM students in this episode of Diverse: a SWE podcast! Views: 2
Back-to-School Activities for SWENext Clubs
SWENext Influencer Zeynep S. shares the activities, guest speakers, and competitions planned for her SWENext Club this year. Views: 1
How a Reinvention Mindset Can Turn Setbacks Into Growth
SWE member Lori McDowell reflects on the mindset shifts that helped her bounce back and thrive after a difficult situation in her STEM career. Views: 1
Safety, Respect, and Inclusion: Our Stance Against Harassment at the WE24 Annual Conference & Career Fair
The SWE Annual Conference & Career Fair is a place where women, nonbinary individuals, and men as allies of all backgrounds can support the overall persistence...
ConfusedPilot: UT Austin & Symmetry Systems Uncover Novel Attack on RAG-based AI Systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: Claude Mandy Executive Summary Researchers at the Spark Research Lab (University of Texas at Austin)1, under the supervision of Symmetry CEO Professor...
USENIX NSDI ’24 – Spectrumize: Spectrum-Efficient Satellite Networks for the Internet of Things – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Vaibhav Singh, Tusher Chakraborty, Suraj Jog, Om Chabra, Deepak Vasisht, Ranveer Chandra Our sincere thanks to USENIX, and the Presenters...
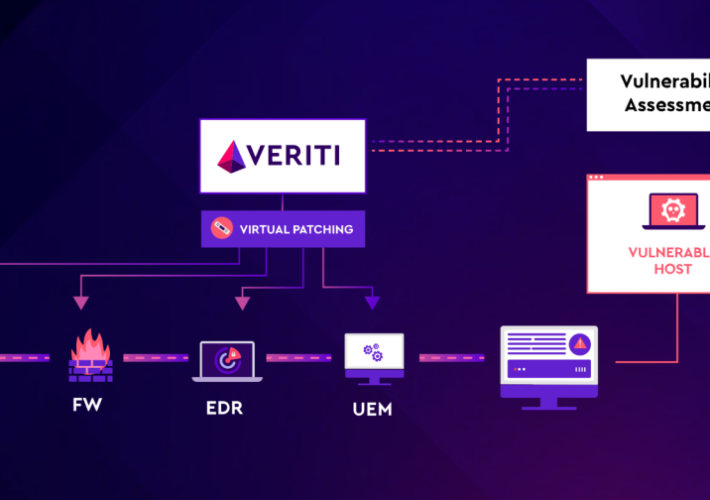
Patch-22: The Catch of Waiting to Fix Cybersecurity Vulnerabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Greenberg One of the biggest dilemmas for security teams is when to patch vulnerabilities. This is a classic “Patch-22” situation—patching immediately...
Misinformation, Online Scams Surging Following Historic Hurricanes – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity Bad actors often take advantage of natural disasters, and especially hurricanes, in times of crisis. Hurricanes Helene and Milton...